Adopting Zero Trust with Agilicus AnyX
Learn how organisations are using Agilicus AnyX to adopt Zero Trust. Read more about industry best practices with our white papers, and learn why the platform stands out when it comes to enhancing security with our brochures.
Resources
Leveraging Agilicus AnyX to adopt a best of breed Zero Trust Architecture to enhance security and resolve access challenges. Learn more, read the case studies, brochures, white papers, and articles.
-
Agilicus AnyX Brochure
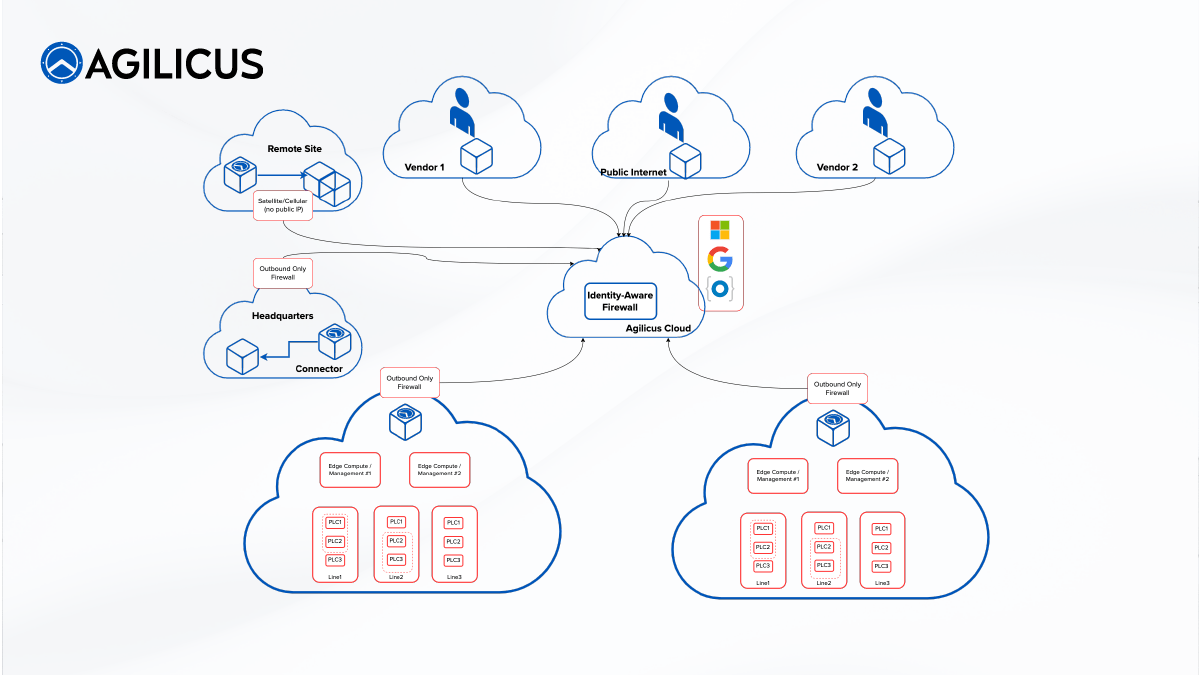
Agilicus AnyX is the only purpose-built product to solve the industry challenges of enabling any user (staff, partner, vendor) to safely, securely, simply remotely operate operational technology, without re-architecting the underlying SCADA networks.
-

Quickly Meet Cyber Security Insurance Requirements with Agilicus AnyX
Meet Cyber Security Insurance Requirements. Accelerate cyber readiness and reduce risk by adopting a network access and security strategy that meets compliance criteria while bolstering cyber defences organisation wide.
-

Strengthening Cybersecurity in Industrial Control Systems for Public Water Infrastructure
Secure and simplify your Industrial Control Systems to Improve Cybersecurity in Industrial Control Systems for Public Water Infrastructure
-
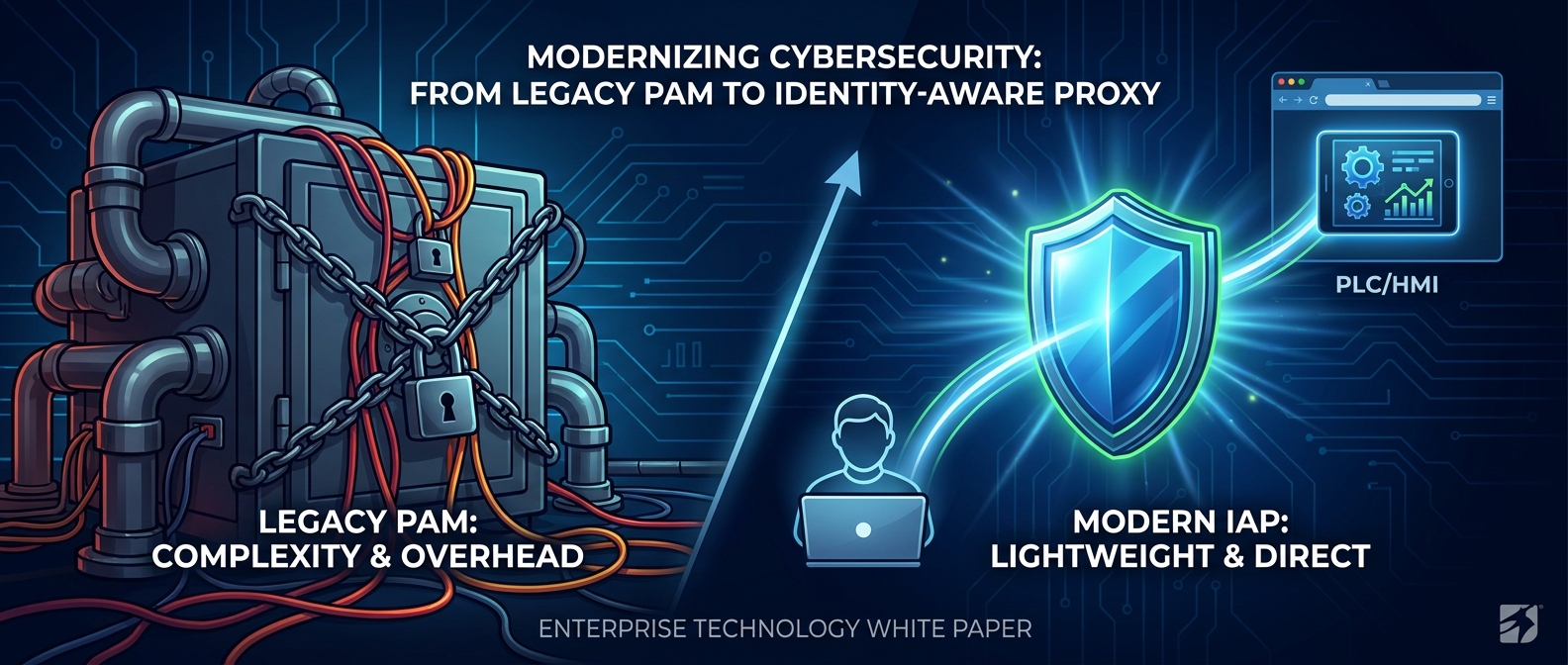
Why the Simplicity of an Identity-Aware Proxy Wins Over Legacy Privileged Access Management
Discover why Layer 7 Identity-Aware Proxies are superior to legacy Privileged Access Management suites. This whitepaper explores how Agilicus AnyX replaces complex credential vaults and vulnerable jump hosts with native identity federation, securing critical infrastructure and legacy industrial protocols like Modbus and Rockwell Studio 5000 with clientless, verifiable Zero Trust.
-

Pragmatic Cyber Resilience: Achieving the Canadian Centre for Cyber Security 36 Readiness Goals with Agilicus AnyX
Critical infrastructure operators in Canada face a daunting new regulatory reality. Discover how Agilicus AnyX enables a pragmatic, identity-first path to the 36 Cyber Security Readiness Goals. By moving beyond analysis paralysis, stakeholders can achieve material compliance incrementally through unified authentication, precise authorisation, and seamless, clientless access.
-
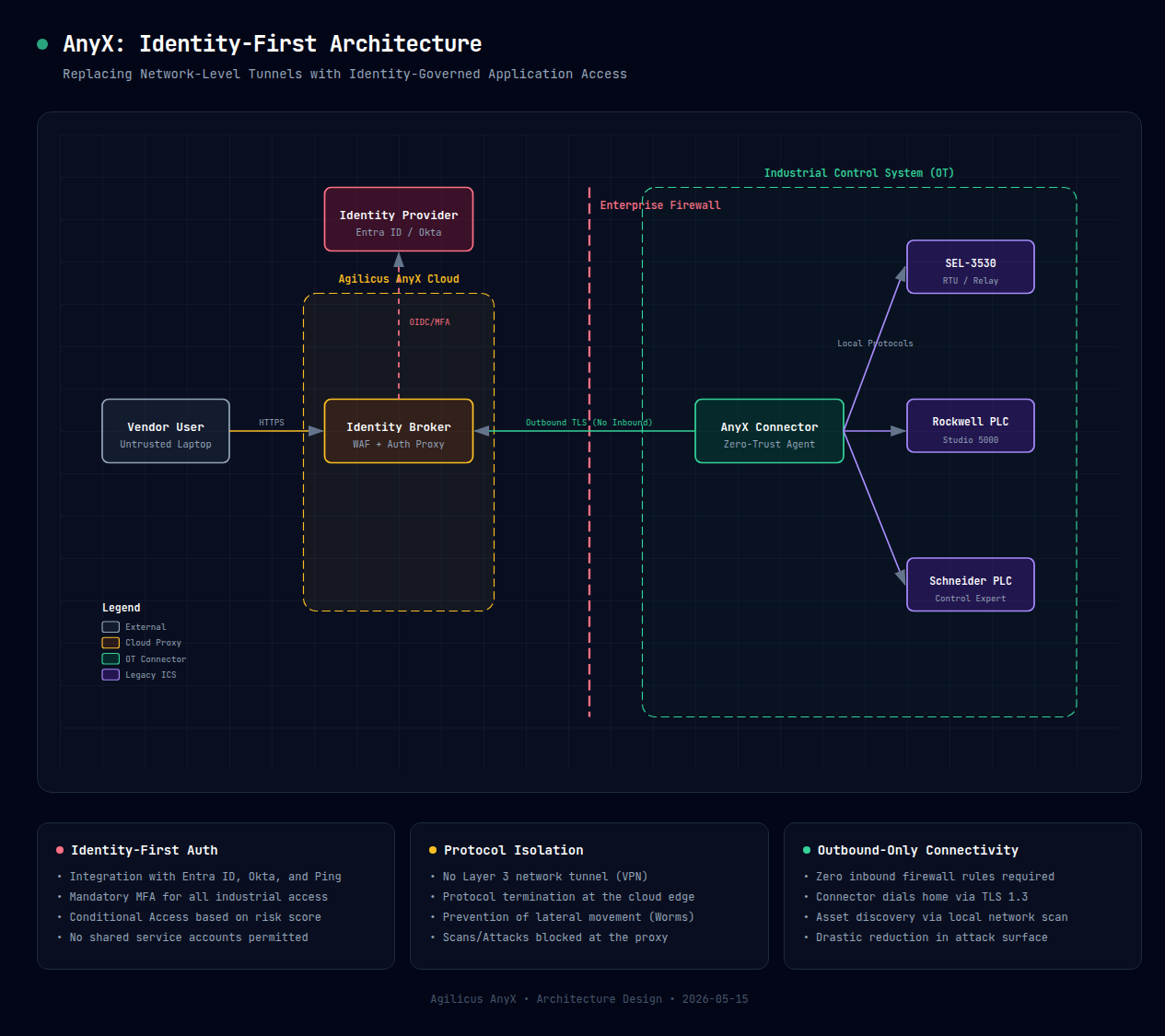
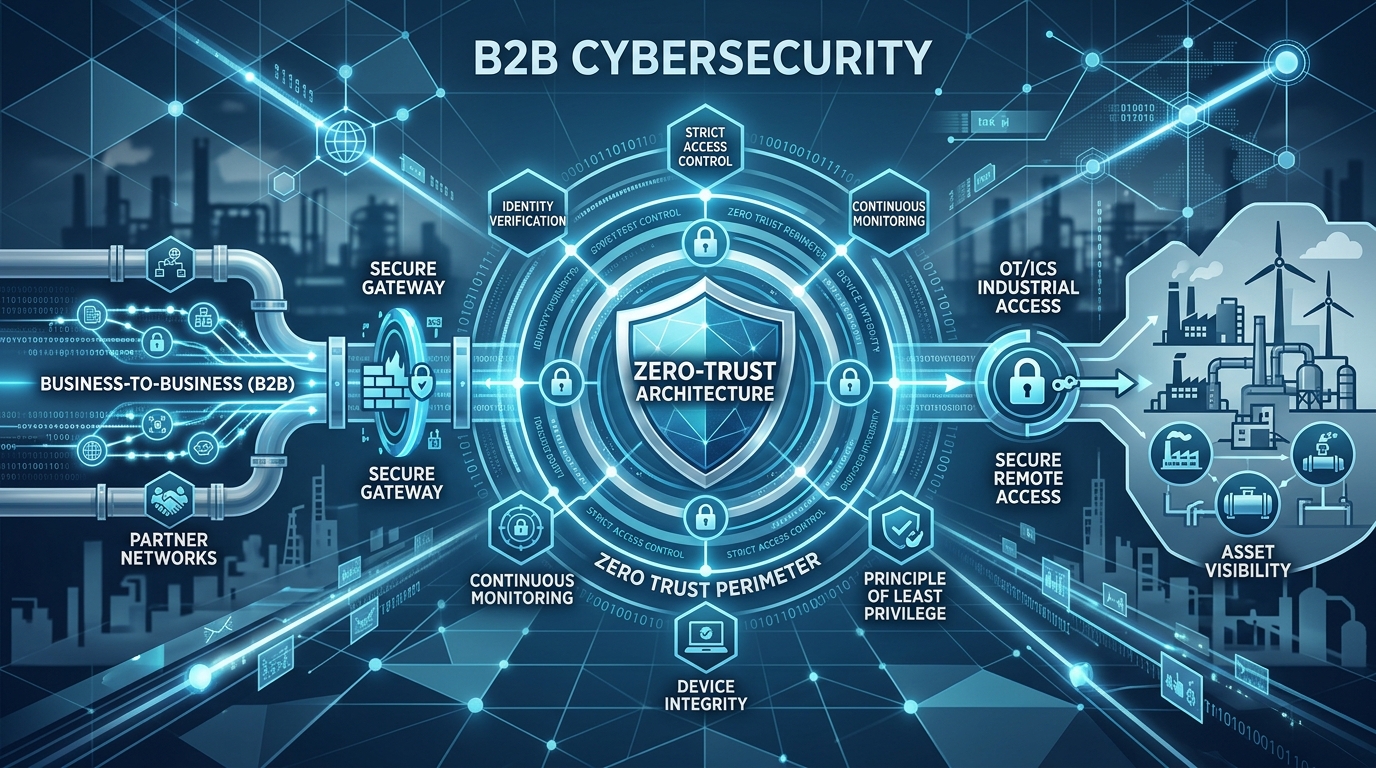
Transforming Industrial Connectivity into Identity-Governed Compliance
Critical infrastructure operators face a paradigm shift in regulatory accountability. This whitepaper examines the technical transition from Layer 3 VPN-based connectivity to Layer 7 Identity-First access. By wrapping legacy industrial protocols (VNC, RDP, Modbus/TCP) in a modern identity layer, Agilicus AnyX provides the granular authorization and cryptographic evidence required for compliance with NERC CIP-003-9, NIS2, and CCSPA. Includes implementation patterns for SEL, Rockwell, and Schneider Electric assets.
-

The evolution of NERC CIP-003: Transitioning from 9 to 11 and securing the grid
FERC’s approval of CIP-003-11 expands cybersecurity controls from vendor access to all electronic access. Learn how this impacts legacy systems, the risks of compliance over-correction, and how Agilicus AnyX delivers unified authentication to secure distributed operational technology without hindering operations.
-

Industrial Cyber Security Best Practices
Identity is the new air gap for modern industrial environments. This strategic blueprint provides a pragmatic roadmap for securing converged information technology and operational technology systems. By applying defence in depth and the Purdue model, organizations can replace obsolete virtual private networks with outbound-only tunnels, implement phishing-resistant multi-factor authentication, and use micro-segmentation to prevent lateral movement.
-

Enabling NIS2 Compliance for VNC Remote Access in Industrial Control Systems
Learn how to secure legacy factory screens and HMIs without replacing your existing architecture. Agilicus AnyX applies zero trust to legacy protocols, delivering multi-factor authentication seamlessly.
-
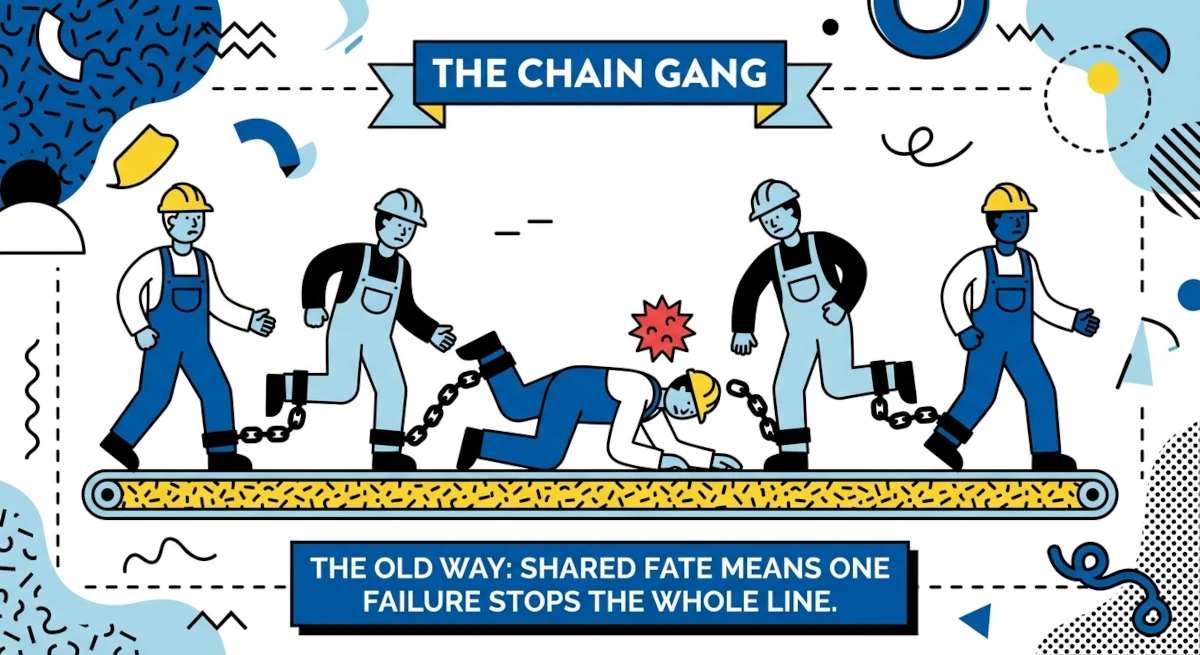
Why traditional VPNs are the weak link in NERC CIP-003-9 compliance
Discover why legacy virtual private networks fail NERC CIP-003-9 standards and how zero trust provides a secure, invisible alternative for energy utilities.
-

The energy utility’s guide to replacing VPNs for NERC CIP secure remote access
A guide for energy utilities replacing VPNs. See how zero trust identity-aware proxies solve OT network complexity and ensure NERC CIP-003-9 compliance.
-

The Fragility of Interdependence: Securing the Hyper-Specialised Supply Chain in the Age of Cyber-Physical Convergence
Hyper-specialised supply chains are fragile. Download this whitepaper to see how zero trust secures the industrial mesh against evolving cyber threats.
-
Multi-Site Manufacturing
Multi-site manufacturing requires seamless access. Discover how identity-based zero trust delivers secure connectivity for staff and contractors at every site.
-
The Frictionless Factory: Solving the Connectivity Crisis in Hyper-Specialised
Solve the connectivity crisis in hyper-specialised factories. Decouple access from the network with Agilicus AnyX to eliminate VPN friction and cyber risk.
-

Agilicus AnyX Configuration Security
Is cloud configuration secure? Learn how Agilicus AnyX protects your settings and discover why it offers superior security compared to on-premise systems.
-

How zero trust architecture secures critical energy infrastructure and satisfies NERC CIP
Energy providers: satisfy NERC CIP-005 and CIP-003-9 with zero trust. Deliver unified authentication and precise authorisation without network changes.
-
Simplified NERC CIP compliance for low-impact BES cyber assets
Meet NERC CIP-003-9 requirements for low-impact BES assets. Agilicus AnyX delivers seamless multi-factor authentication without complex network configuration.
-

Secure remote access for energy utilities: Meeting NERC CIP standards without a VPN
Secure energy utility remote access without VPN headaches. Learn how identity-aware proxies ensure NERC CIP compliance for third-party vendors and OT networks.
-

NERC CIP-003-9: Automating access control and authorisation for remote power sites
Automate access control for remote power sites. Replace manual processes and legacy VPNs with agile zero trust to meet NERC CIP-003-9 requirements efficiently.
-

NERC CIP-003-9 and the shift to multi-factor authentication
Energy utilities: secure low-impact systems with multi-factor authentication. Discover how zero trust enables NERC CIP-003-9 compliance for legacy OT.
-

NERC CIP-003-9 – Legacy Remote Access Tools are Not Sufficient
On April 1, 2026, CIP-003-9: Cyber Security – Security Management Controls will become enforceable. Meet those requirements with a Zero Trust platform.
-

Securing the Distributed Supply Chain: Why Identity is the New Air Gap
Secure the distributed supply chain in Industry 4.0. Learn why zero trust architecture makes identity the new air gap for complex manufacturing ecosystems.
-
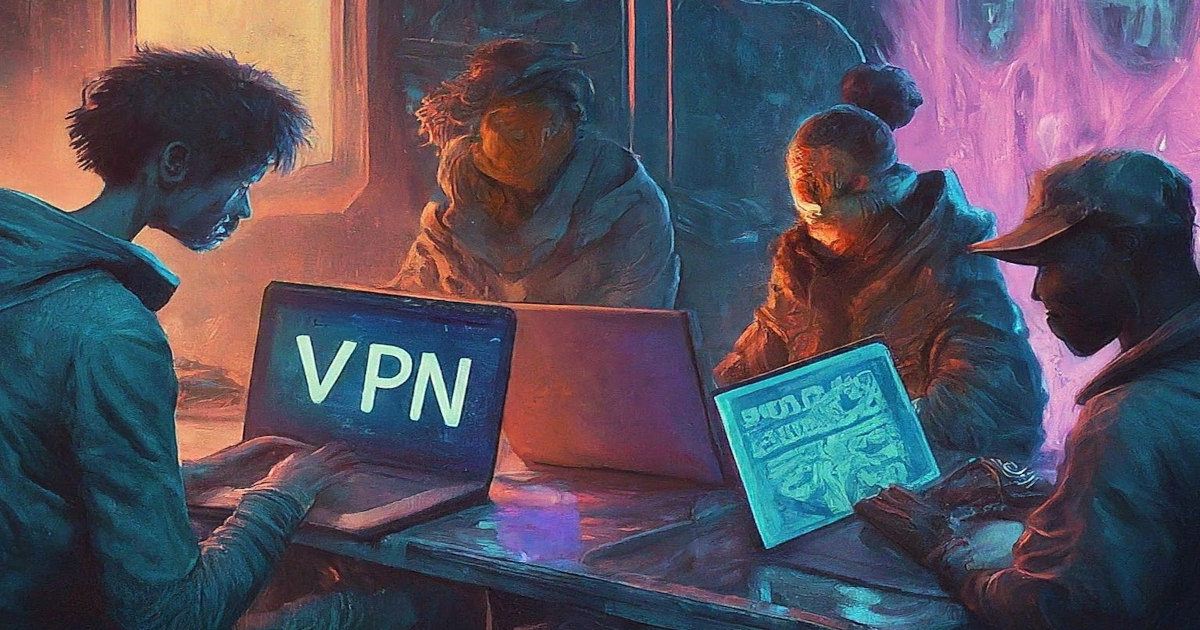
VPNs: Complex, non-compliant, and lacking security for modern remote access
VPNs are no longer sufficient for modern security. Explore why traditional remote access fails to meet compliance and how zero trust provides a safer foundation.
-

Secure Remote Updates For Air-Gapped Systems
Challenges with, and solutions for, Secure Remote Updates in modern complex control systems deployed in locked-down, air-gap-style networks. Agilicus AnyX enables and secures remote updates for air gaps.
-
High Availability Dual WAN Remote Industrial Connectivity
Industry cannot stop. Industry is also commonly located in remote areas with less network connectivity choices. Learn how Agilicus AnyX facilitates High Availability Dual WAN Remote Industrial Connectivity.
-
Subscription Model and Remote Access In Industrial Control
Subscription Model and Remote Access In Industrial Control. The quest for revenue creates risks for operation.
-
Merging Local Identity With Online Identity
Modern online Identity with Azure, Google, Okta. Manufacturing plants with Local Identity — onsite users Unify with Agilicus AnyX
-
NIST SP 800 53 Mapping To Zero Trust
NIST SP 800 53 Mapping To Zero Trust. NIST SP 800 53 is a comprehensive set of security controls. Zero Trust Network Architecture is a technology. Explore the intersection.
-
NIST SP 800-53 in Critical Infrastructure
NIST SP 800-53 is a core part of the NIST cybersecurity framework. It provides mappings of controls to various other standards. Zero Trust is a complementary architecutre supporting these controls.
-
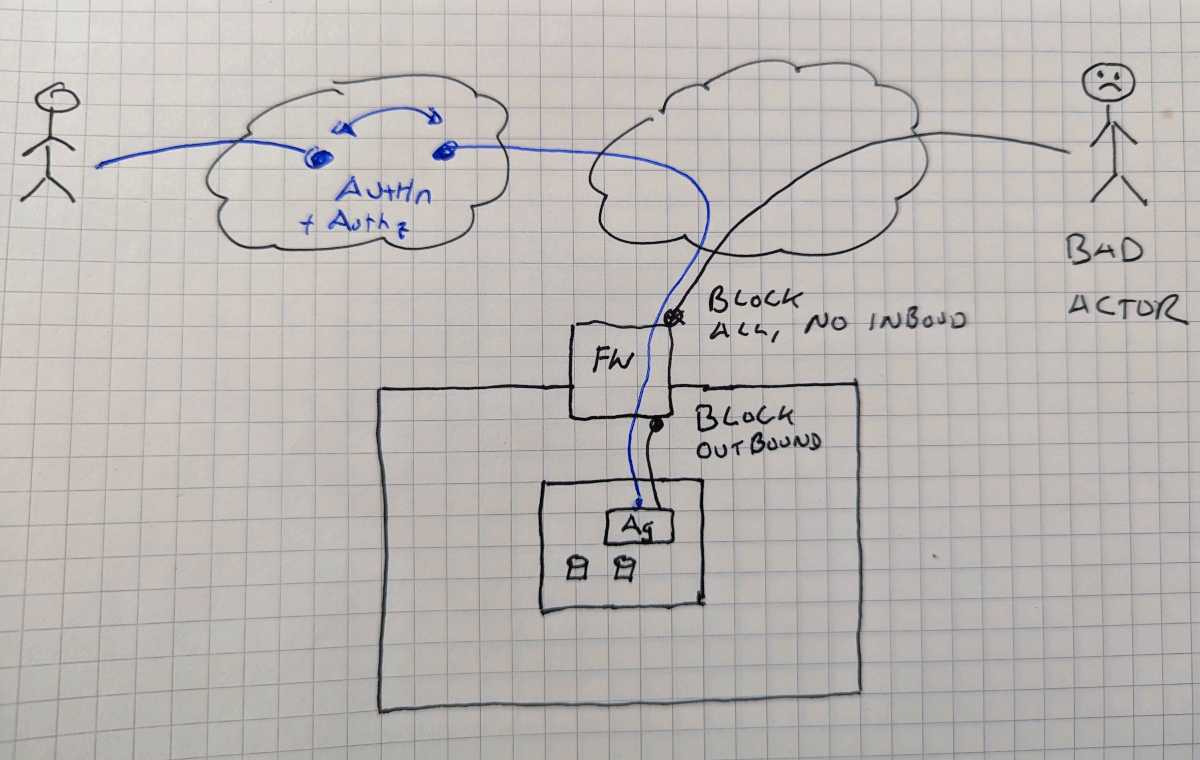
Zero Trust Air Gap Lock Down Inbound and Outbound
Air Gaps are a useful but inconvenient tactic as a part of a defense in depth strategy. Learn how a Zero Trust Air Gap Lockdown Inbound and Outbound can provide convenience and security together.
-
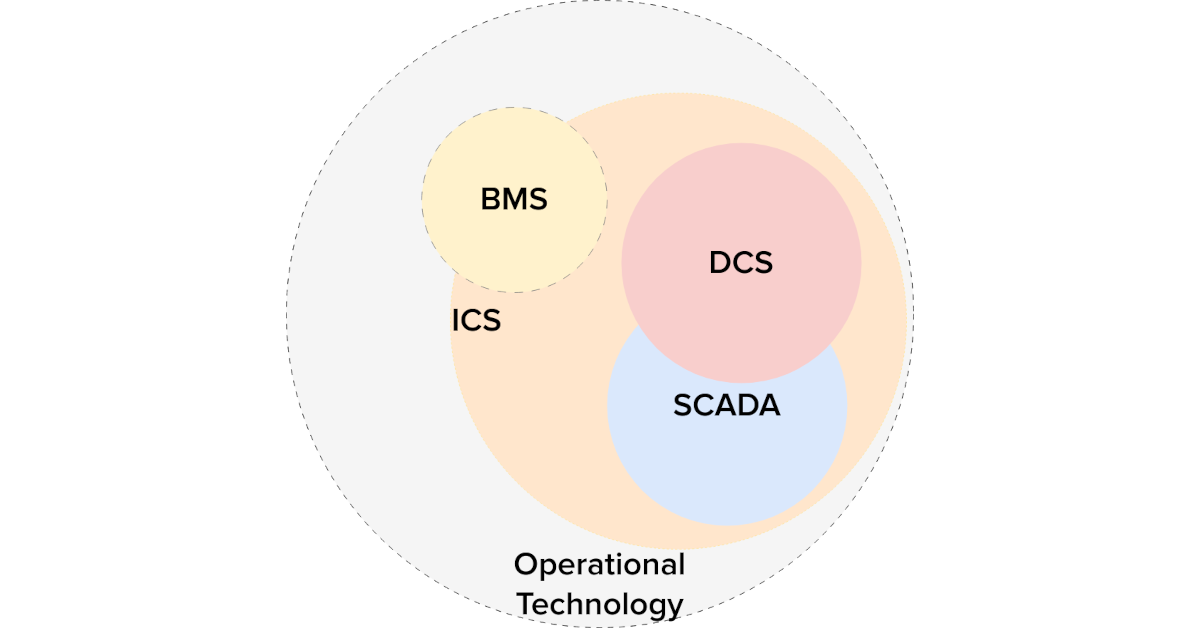
Piercing The Purdue Model: Zero-Trust In Operational Technology
Unravelling the interaction between the Purdue Model and Zero Trust: When married together in operational technology, the outcomes can be transformative.
-
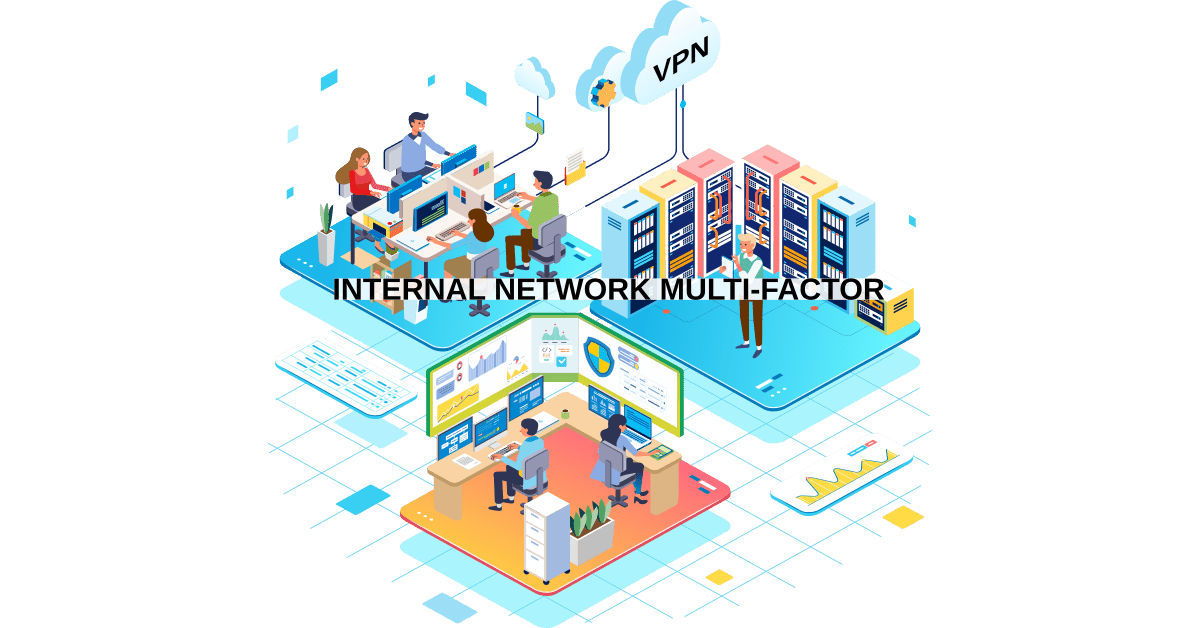
Multi-Factor Authentication On The Internal Network
Cyber-Insurance compliance require multi-factor on internal network resources? Routers? Servers? Learn how to implement without a VPN, without changes.
-
Industrial Zero-Trust Micro-Segmentation
Micro-Segmentation Zones are a best practice for Industrial Control security. Simplify and increase effectivity with identity-based Zero-Trust. Industrial Zero-Trust Micro-Segmentation
-

Eliminate Attack Vectors and Stop Cyber Threats in Their Tracks with a Zero Trust Architecture
Eliminate Attack Vectors and Stop Cyber Threats in Their Tracks with a Zero Trust Architecture. Cyber threats come from all angles these days, yet most businesses are still ill equipped to properly keep the bad actors out.
-

Remote Desktop Access: Managing Cyber Risk with Zero Trust Network Access
Eliminate unmanaged cyber risk by securing remote desktop access through zero trust network access and improve your cybersecurity posture.
-
Azure Application Consent
The Agilicus AnyX platform uses external Identity Providers rather than creating ‘parallel’ identities for users to remember. What permissions are being granted on those upstream systems?
-

Starlink Port Forwarding
Starlink. Good enough except for starlink port forwarding. Reach your devices from remote with Agilicus, securely, simply, reliably.
-

From Smoke Stacks to Smartscapes: Evolving Industrial Operations in the Digital Age
Smoke Stacks to Smartscapes. Past, Present, Future, the evolution in-place of the industrial control system, and the airgrap that once protected it.
-
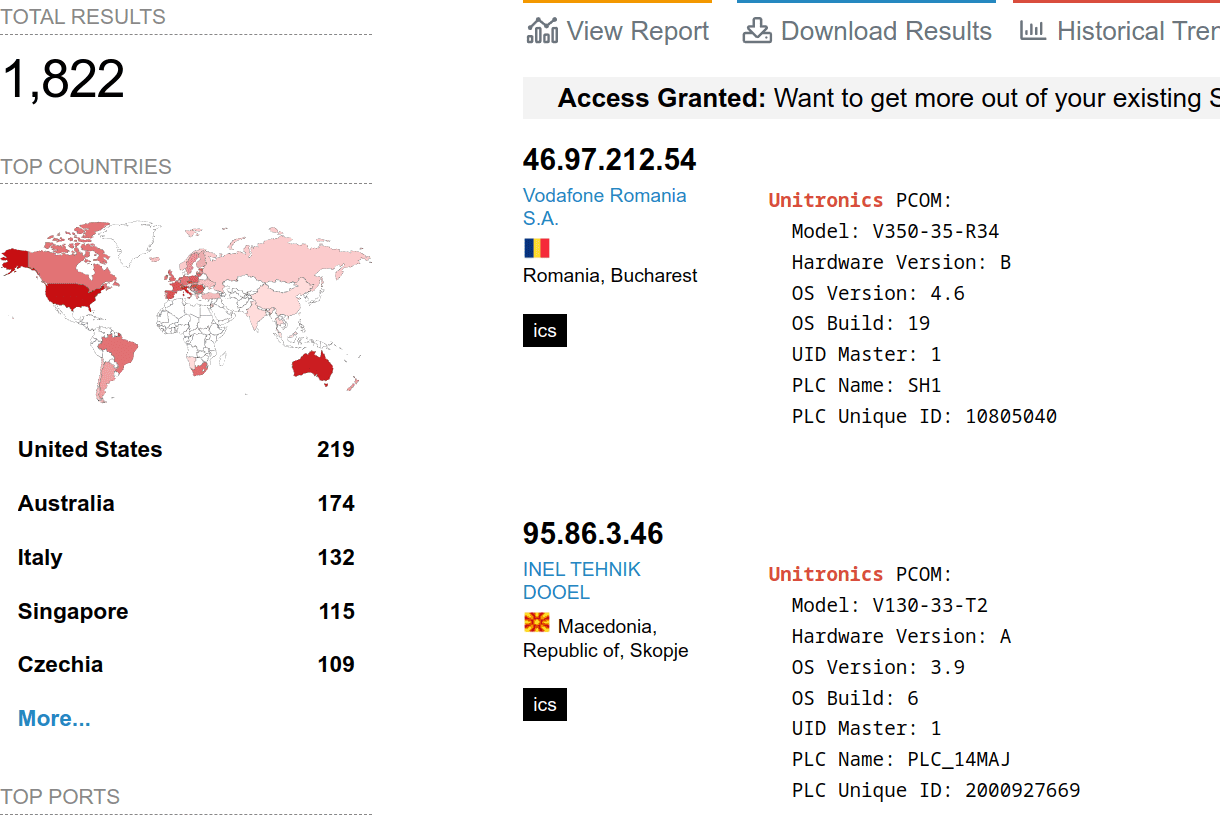
Avoid Exploitation of Unitronics PLCs used in Public Water Systems
Exploitation of Unitronics PLCs used in Public Water Systems for political purposes. Recommendations.
-

NIST sp 800-63A: Introduce Yourself
Who are you? Identity involves knowing who you are, and then later proving it. NIST sp 800-63A enrollment is the first step, let’s talk about that!
-
EPA Cybersecurity Recommendations: Unpacking the Impact on Public Water Systems
This article will help you understand the new EPA cybersecurity recommendations, why they matter for public water systems, and the recommended solution.
-
Protecting Against the OWASP Top 10 Web Application Vulnerabilities
The OWASP Top 10 is a standard awareness document that outlines the most critical web application security risks and vulnerabilities. Learn how Agilicus AnyX is designed to eliminate an attacker’s visibility into the potential OWASP Top 10 web application vulnerabilities.
-
Agilicus and Operational Technology
Zero Trust Network Architecture can effectively meet the growing demand for enhanced cyber security in industrial and operational technology.
-
Industrial Air Gap – A Tale Of 2 Users
Industrial devices are hard to secure. Commonly done only via direct local access. Teams, however, wish remote access to improve efficiency. A solution to this battle is Zero Trust.
-

NIST sp 800-63A: Introduce Yourself
Who are you? Identity involves knowing who you are, and then later proving it. NIST sp 800-63A enrollment is the first step, let’s talk about that!
-
NIST sp 800-63B: How Well Do I Know You?
Zero-Trust Network Architecture has 3 steps: Authenticate (Who), Authorise(What), Access(How). 3 Levels of strength of the who are defined in NIST sp 800-63B. Does the goldilocks principle apply to you? Read on!
-
Agilicus AnyX versus Cloudflare Zero Trust
Compare Agilicus AnyX and Cloudflare Zero Trust. See how Agilicus provides secure, clientless access for critical infrastructure without complex DNS changes.
-

Agilicus AnyX versus Tosibox
Compare Agilicus AnyX and Tosibox. See how Agilicus provides a Zero Trust, clientless proxy for OT environments with granular audit and identity integration.
-

Agilicus AnyX versus Nebula
Compare Agilicus AnyX and Nebula. See how Agilicus provides secure, clientless Zero Trust access for OT systems without the complexity of layer-3 VPN overlays.
-
Agilicus AnyX versus FortiSRA
Compare Agilicus AnyX and Fortinet FortiSRA. Discover how Agilicus provides a complete Zero Trust solution for OT with native identity and agentless access.
-
Understanding Cyber Security Risk
Risk management is not about achieving zero risk: it is about aligning security controls with organisational appetite and opportunity.
-
Agilicus AnyX versus Splashtop
Compare Agilicus AnyX, a comprehensive Zero Trust Network Access platform, with Splashtop, a tool for remote desktop access. This article evaluates both solutions on features like native client support, single sign-on, multi-factor authentication, detailed auditing, and embedded HMI support, highlighting the security and functionality differences.
-

Agilicus AnyX versus TeamViewer
Compare Agilicus AnyX and TeamViewer. Discover why identity-aware zero trust beats shadow-IT backdoors for secure remote desktop and industrial access.
-
Zero Trust VTScada Twilio Alerts
Zero Trust VTScada Twilio Alerts. Monitor your VTScada system with Twilio. Without exposing its login to the Internet. Simple, secure, no config change.
-

Zero Trust VNC Remote Desktop
1-click VNC remote desktop, single-sign-on, multifactor authentication. Zero Trust VNC Remote Desktop provides high-convenience with high security.
-

Northern Rockies Regional Municipality
How Northern Rockies Regional Municipality Transitioned to a Zero-Trust Enabled Work From Anywhere Environment with Agilicus AnyX
-
Managed Industrial Remote Access
Learn how Water Control Automation uses Agilicus AnyX for Zero Trust managed industrial remote access, providing secure, clientless connectivity for OT systems.
-

Midland Texas Transforms Water Purification Cyber Security
The City of Midland, Texas chose Agilicus AnyX Zero Trust to secure its Water Purification plant
-
ACME Manufacturing Transforms Security and Efficiency with Agilicus AnyX
ACME manufacturing chose Agilicus AnyX to enable SAP access to a multi-division, contract-manufacturing environment. Safely, Securely, Simply.
-
Wastewater Zero Trust Remote Operations and Asset Management
Wastewater Zero Trust Remote Operations and Asset Management. Learn how this industrial control systems engineering company expanded their service offering with Agilicus AnyX.
-

How the Town of Mono Future-Proofed its Cybersecurity Infrastructure and Transformed Municipal Operations
The Town of Mono future-proofed its cyber security infrastructure and exceeded compliance requirement by transitioning to Zero Trust.
-
Starlink Remote Cameras: 3-Steps to Enable Inbound Remote Access
Learn to use Agilicus AnyX to enable Starlink Remote Camera inbound remote access, despite CGNAT. Access your security video from anywhere.
-
Starlink and Synology NAS: How to Enable Inbound Remote Access
Learn to use Agilicus AnyX to enable inbound remote access to your Starlink and Synology NAS setup, despite CGNAT. Access your files from anywhere.
-

Case Study: Apple Screen Sharing, Zero Trust, Multi Factor Authentication
Remote Apple Screen Sharing with Zero Trust, Single-Sign-On, Multi-Factor Authentication. Without a VPN.
-

How the City of Kenosha Transitioned to Zero Trust
How the City of Kenosha Transitioned to Zero Trust using Agilicus Zero Trust to achieve EPA compliance and gain multi-factor authentication, vendor security, audit trails, and network visibility.
-
Case study: Protecting Critical Municipal Infrastructure and Securing Operational Technology at a Water Treatment Facility
Protect a municipal SCADA water treatment facility. Provide multi-factor authentication, secure remote access to staff and partners with single-sign-on.
-
Case Study: Secure Access to Critical Infrastructure for Partners and Vendors
Critical Infrastructure for Partners and Vendors. A Municipality modernised a water treatment facility to enable secure connectivity for various internal teams (IT, Public Works), partner organisation, and their systems integrator.
-

Third Party and Vendor Access Management for Critical Infrastructure
Adopting Vendor Access Management and enforcing multi-factor authentication for access to municipal critical infrastructure.
-

Add Multi-Factor Authentication to Legacy Systems with Agilicus AnyX
A municipality was seeking a method for securing access to the SCADA systems through the implementation of Multi-Factor Authentication.
-
Case Study: A VPN Alternative for Securing Remote Access to Legacy Applications
A municipality in Southern Ontario was seeking a method of securing remote access to legacy applications – responsible for the treasury, billing, and permit functions.
-
Secure Remote Connectivity to 100 Critical Infrastructure Sites, Nationwide
A major systems integrator that services critical infrastructure across the United States seamlessly transformed their service model through Zero Trust, to reduce costs while enabling secure remote connectivity to over 100 customer sites. Learn how Agilicus AnyX was used to simplify access while ensuring the systems integrator could adhere to each customers expectations on security.
-

Enabling Secure Access to Web Applications through Zero Trust
Learn how Agilicus helped a Canadian Municipality extend secure access to web applications for mobile workers through a zero trust framework.
-

De-Risking Operational Technology: 5 Security Investments That Deliver Disproportionate Returns
Stop relying on the mythical air gap to protect your Operational Technology. In this webinar, Don Bowman reveals five practical, orthogonal security investments to systematically de-risk your hybrid IT/OT environment. Discover how to implement true defense-in-depth without disrupting operations or breaking the bank
-

VTScada inbound Twilio
Securely integrate VTScada with Twilio for remote alarm monitoring over Starlink or cellular networks. The Agilicus AnyX Zero Trust architecture requires no VPN, no firewall changes, and no inbound connections, keeping your operational technology safe from the public internet.
-
Simplify NERC CIP Compliance Without the Friction of Legacy VPNs
See how Agilicus simplifies NERC CIP compliance and secures remote access for critical infrastructure by replacing complex, outdated perimeters with a modern Zero Trust platform.
-

Enabling NIS2 Compliance for VNC Remote Access in Industrial Control Systems
Learn how to secure your legacy factory screens and Human Machine Interfaces without replacing existing architecture. Apply zero trust to legacy protocols, delivering multi-factor authentication and end-to-end encryption for full NIS2 compliance.
-

SSH via Zero Trust. No public IP needed.
Use Zero Trust networking to provide access with no public IP, no inbound firewall changes, and, remain end-to-end encrypted.
-
Authentication and the API Key
We all think about authentication as a user signing-in. But what about, once signed in, the ‘create api key’ that is a permanent password? Where does that go? Zapier? Script in home dir?
-
Simple 3-Step Program To Reduce The Risk Of Ransomware
Learn a simple 3-step program to significantly reduce the risk of ransomware attacks. This video outlines the foundational principles of modern security: Authentication, Authorization, and Access. Key steps include enabling multi-factor authentication on your identity provider and consolidating all applications to use a single identity, eliminating locally stored accounts. Discover how implementing these measures can shift your security posture from risk to reward.
-

De-Risking Operational Technology: 5 Security Investments That Deliver Disproportionate Returns
The convergence of factory floors and corporate networks creates immense technical friction. Learn the five orthogonal dimensions of industrial security to practically eliminate operational exposure without disrupting uptime.
-

The False Choice of NERC CIP-003-9: Keep Remote Access and Stay Compliant
NERC CIP-003-9 forced many operators to shut down remote access to achieve compliance. This is a false choice. Learn how to restore vendor connectivity, maintain operational workflows, and satisfy auditors simultaneously using Zero Trust architecture.
-
The Vendor Vulnerability: 5 Lessons from the Major Breaches of 2025
Still trusting vendors with shared VPN keys? That’s how you get breached. Join us to learn how to replace porous network access with bulletproof Zero Trust, Single Sign-On, and Multi-factor Authentication.
-

NERC CIP-003-9: Why Your VPN is a Compliance Dumpster Fire
April 1 brings the enforcement of NERC CIP-003-9 Section 6. Discover why VPNs fail the new Low-Impact BES requirements for vendor remote access and how to implement time-of-need, pre-authorised access with granular audit trails.
-

The Rising Tide of Regulation: Zero Trust for Water Utilities
State mandates for water utility cybersecurity are increasing. Learn how to navigate regulations like CA AB 749 and IN SEA 472 by moving from unsafe VPNs to a Zero Trust Architecture.
-

Why VPNs Are Not a Viable Solution for Multi-Site Manufacturing
As manufacturing networks expand, traditional VPNs create dangerous security gaps like lateral movement and unrestricted access. Join us to discover a safer alternative for multi-site connectivity. Learn how to implement secure, granular remote access that streamlines maintenance, enforces MFA, and protects your critical industrial systems—without the clunky VPN.
-
Improve Mean Time To Repair with a Zero Trust Architecture for Remote Maintenance
When a system suffers an outage or other operational issues, requiring internal or third-party users to be on-site can cost valuable time and money. Allowing your users to remotely access systems allows you to resolve issues faster.
-

How AI Threatens the Industrial Control Systems in Small and Mid-Size Manufacturing
As we move towards 2026 and AI tools become more capable, hackers are turning to them more and more, creating new threats across the board. Explore how you can protect your organization by adopting Zero Trust
-

Cyber Breaches Can Shut Down Your Production Floor
The manufacturing industry is going through a revolution, industry 4.0, impacting the industrial control systems on your manufacturing floor. Protect your organization from evolving threats.
-

Protecting Local Governments from Evolving Cyber Threats
With a recent rise of threat actors conducting large scale cyber attacks you need to ensure that remote access is properly implemented and systems aren’t reachable to threat actors.
-

Upcoming Remote Access Regulation: How Zero Trust Prepares Your Water Infrastructure
Maryland is mandating water facilities and critical infrastructure adopt strict cybersecurity policies for their remote access and network operations. States like New York, California, Texas, and others are quickly following suit. Stay Ahead with Zero Trust
-

Zero Trust: The Cyber Security Mandate for Insuring Your Municipality.
Learn how a Zero Trust framework helps municipalities meet evolving cyber insurance requirements, comply with state mandates, and secure remote access.
-

Municipal Remote Access: Protecting Against Cyber Threats While Streamlining How Users Access Shared Resources
Cyber threats against municipalities are increasing and becoming smarter. With AI backed threat actors and new network vulnerabilities being taken advantage of, the threat to municipalities is larger today than ever. This webinar offers a look into protecting your municipality resources while streamlining remote access.
-

The New Standard for Industrial Water Systems: Industry 4.0 and Hybrid Workforces
Water/wastewater facilities are going through a revolution with technology becoming engrained in critical infrastructure operations. Learn how to safely allow remote access to your critical infrastructure.
-
Cyber Criminals are Adopting AI: Keep your Critical Infrastructure Protected
As threat actors increasingly adopt the use of AI they’ve become able to execute cyber attack attempts at a more personal level, faster. Learn how you can protect your critical infrastructure in a new cyber threat landscape.
-
Protecting Water Systems from Cyber Threats
Don’t choose between security and accessibility. Learn how to secure your water systems while empowering your team to remotely access the resources they need.
-

Remote Operations: Support Client Systems Without VPNs
Your clients rely on your team to keep their industrial control systems up and running smoothly through routine maintenance and ongoing remote support. Learn how you can deploy efficient and effective remote operations while exceeding client security policies
-

Improving Wastewater Remote Connectivity with Zero Trust
Learn how you can enable remote connectivity to industrial water systems on wastewater treatment facility networks.
-

How Securicore Utilizes Zero Trust for Remote Access
Join Agilicus and Securicore to learn how you can enable Zero Trust remote access to the systems/resources on your network
-

Eliminate Shared Passwords for Vendor Access
Learn how you can – without sacrificing security or creating a large spend in time, effort, and resources – enable remote access to industrial control systems on your floor
-

How to Implement Zero Trust for Local Government
Local governments are making the switch to a Zero Trust security model to protect their systems against modern threats. Join us to learn how.
-

Securely Connect to Client Resources, Streamline Operations
Your clients rely on your team to help keep their industrial control systems up and running (HMI, PLC, SCADA) smoothly through routine maintenance and ongoing remote support. Providing remote support can become a headache when firewall/VPN configurations are unique for each client, requiring multiple logins, settings, and platforms for each support ticket.
-
HMI, PLC, and SCADA Water Systems with Multi-Factor Authentication
Multi-factor authentication and single sign-on are two quick and effective ways to improve your security posture without causing a major disruption in your users’ workflow
-
VNC & RDP for Water: Access Dashboards Remotely
Learn how to get the most out of your Virtual Network Computing (VNC) and Remote Desktop Protocol (RDP) for HMI and other usage
-
Add Remote Operations: Support Clients Faster & Reduce Costs
Learn how implementing remote operations to your organization can unlock new efficiencies in the way you troubleshoot and service client systems.
-

Master Vendor and Contractor Access Management
Learn to establish and leverage a robust vendor access management program that reduces third-party cyber risk without complicated workarounds
-

Add Wastewater Remote Operations, Streamline Service
Join us to learn how implementing remote operations to your organization can unlock new efficiencies in the way you troubleshoot and service public water systems.
-
VPN Alternatives for Water and Critical Infrastructure
Learn how we can connect the people who need it. Single Sign On for all, regardless of partner or employee. Multi-factor where needed, even on legacy applications. WITHOUT granting full VPN access.
-

Legacy Life-Extend: More Users, More Secure, No Changes
Legacy municipal support systems are difficult to make widely available without compromising security. Learn how to solve.
-
Cyber Alerts, Best Practices: Put Advice To Action
Government agencies are publishing cyber advice. Each notice is individually full of good facts and advice, but collectively, they are creating indecision: what do I do first? when? how? With what budget? Today we will talk about how to interpret, how to implement, economically, without disruption.
-
-
A VPN Alternative for Local Governments
The VPN, a powerful tool, is not appropriate for all users. Learn how we can connect the digitally disenfranchised. Single Sign-on for all, multi-factor on everything.
-
A VPN Alternative for Manufacturing
The VPN, a powerful tool, is not appropriate for all manufacturing users. Learn how we can connect the people who need it.
-

Cybersecurity on a Budget, Secure and Simple
Whether it’s remote operations and support, on site staff, or routine maintenance – ensuring your industrial water systems have proper access controls without causing a strain on your budget is crucial.
-

Add Remote Support, Leverage Your Specialists
Learn how to enhance efficiency and reduce costs by enabling remote support for your specialist teams. This webinar explores how Agilicus AnyX allows you to meet customer security requirements, incorporate remote access into your service offerings, and lower mean time to repair. Discover how to empower your automation and support specialists to manage multiple client needs simultaneously without the need for costly site visits, VPNs, or hardware installations.
-

Simplify Remote Access, Secure Industrial Equipment
No VPN, No Shadow IT Like TeamViewer. Simplify and Secure remote manufacturing industrial access for multiple divisions, contract manufacturers, vendors
-
Nation State Attacks on Critical Infrastructure – Assess, Understand, Protect
This webinar addresses the increasing threat of nation-state attacks on critical infrastructure, particularly water systems. Learn how easily threat actors can identify vulnerabilities using open-source intelligence (OSINT) and tools like Shodan.io. We’ll discuss recent incidents and demonstrate how to protect your SCADA, PLCs, and HMIs with Agilicus AnyX, implementing essential security controls like multi-factor authentication, single sign-on, and privileged access management to eliminate risks associated with remote access.
-
Nation State Attacks on Water – Assess, Understand, Protect
See how an attacker gains access to information of public water systems. We will use tools like Shodan and nmap to detect and assess common vulnerabilities within industrial water systems.
-
VPN Alternative: Decrease Risk, Increase Simplicity
Local Governments have many different systems to safeguard and manage. Learn how a VPN Alternative can help you safeguard systems without restricting access
-

Remote Operations: VPN Alternatives to Improve Simplicity and Security
The VPN, a powerful tool, is not appropriate for all users. Learn how Agilicus can connect the people who need it.
-
VPN Alternatives for Manufacturing
Learn how Agilicus connects the people who need it with a VPN Alternative for manufacturing. Single Sign On for all, regardless of partner or employee. Multi-factor where needed, even on legacy applications.
-
VPN Alternatives for Water and Critical Infrastructure
VPN Alternatives for Water: Emergency directives regarding VPNs serve as a wake up call for a rethink.
-
VPN Alternative for Local Governments
3 recent emergency directives on VPNs? A VPN is a security risk in local government networks. Examine Zero Trust VPN Alternative for Local Governments
-
Securing Wastewater Remote Connectivity with Segmentation and Zero Trust
The modern wastewater plant is now a blend of data centers and pipes. Learn about the complex challenges of allowing remote connectivity to systems in a wastewater treatment facility
-

Solve Vendor Multi-Factor and Single Sign-On for Industrial Support
Learn how you can securely enable vendor remote access to industrial control systems with multi-factor authentication, least privilege access, and single sign-on.
-
Add Wastewater Remote Operations, Expand Revenue
Learn how wastewater remote operations is unlocking new, more profitable and predictable revenue streams by adding pre-defined remote operations services to their portfolio.
-
Fortifying Manufacturing Systems: A Foolproof Framework for Secure Remote Access
Fortifying Manufacturing Systems. Enable secure remote access for any user (with any company) who requires access to systems on the manufacturing floor.
-

Secure Remote Access for Water: Sharing Multiple Dashboards Over VNC
Learn how to get the most out of your VNC apps and workflows with Agilicus AnyX. Discover how to streamline access while limiting it to the right people at the right time.
-

Municipal Cybersecurity Success Stories from Across Canada
Two Canadian Municipalities share their experience deploying Zero Trust with Agilicus AnyX to increase their Cyber Security.
-

Streamlining User Management: Master Vendor Access with Zero Trust
Tune in to this webinar to learn how to streamline vendor access with Zero Trust without a VPN or hardware install.
-

Secure Access for Water: Unlock Application-Only Remote Desktop Access Anytime, Anywhere
Learn how to secure Remote Desktop Protocol (RDP) access for water organizations with Agilicus AnyX. This webinar demonstrates how to provide application-only RDP access, preventing users from accessing the entire desktop environment when only specific applications are needed. Discover how to implement crucial security controls like multi-factor authentication, single sign-on, and least privilege access, while streamlining workflows and enabling secure remote application access from any device.
-

Rockwell Studio 5000™ for Industrial Control Systems: How to Properly Secure & Grant Access
Remotely view tags, program PLC with Rockwell Studio 5000, with no VPN.
-

A Modern Air Gap for Operational Technology
Learn how creating a modern air gap increases your security posture drastically compared to legacy solutions like the VPN and TeamViewer.
-
VPN Alternative for Local Governments: Why and How
A VPN is a security risk in local government networks. Examine Zero Trust alternatives.
-
A Modern Air Gap for Operational Technology
Learn how creating a modern air gap increases your security posture drastically compared to legacy solutions like the VPN.
-

Strengthening the Security Structure of a Water Treatment Facility
Join us online on February 9 and learn how a modern security structure can be strengthened in a water treatment facility.
-
How to Connect to an HMI without a VPN
Connect to an HMI without a VPN. Extend secure access to employees and vendors.
-
The City of Kenosha’s Zero Trust Cybersecurity Transformation
Discover how the City of Kenosha seamlessly pivoted towards a resilient, Zero Trust environment. Embrace a non-VPN paradigm to safeguard your local government.
-

Securing Access to Industrial Control Systems with Zero Trust
Learn how to modernize the manufacturing floor with secure, remote access to Industrial Control System without a VPN or new hardware.
-

Keeping Manufacturing Lines Safe and Efficient: The Power of Least Privilege Access
Keeping Manufacturing Lines Safe and Efficient: The Power of Least Privilege Access. Discover how the principle of least privilege access can ensure your manufacturing systems are safe and running smoothly.
-
Simple, Seamless, Secure: A New Era of Vendor Access for Manufacturing
Join us to learn how organizations are mastering vendor access management to reduce cyber risk without complicated workarounds or disruptive implementations.
-
Guarding the Gate: Embracing Cybersecurity in Public Water Systems
Explore the evolving cybersecurity landscape for public water systems, especially in light of new EPA requirements. Embracing Cybersecurity in Public Water Systems
-
Protecting Industrial Networks with Vendor Access Management
Learn how proper Vendor Access Management reduces cyber risk in a manufacturing setting by reducing your attack surface while enabling secure, auditable access for authorized non-employees.
-
Protecting Critical Infrastructure – Zero Trust and NIST 800-53 CyberSecurity Framework
Learn how Zero Trust strengthens the security of Critical Infrastructure systems with role-based access controls, multi-factor authentication, and detailed audit trails.
-
Securing Access to Industrial Control Systems with Zero Trust
Modern, Simple, Secure Securing Access to Industrial Control Systems with Zero Trust Learn how to modernise your Industrial Control System applications and resources through implementing secure, remote access without a VPN or new hardware. You’ll learn how to enable remote maintenance and troubleshooting while keeping systems off the public internet. During this session we’ll demonstrate how modernising your Industrial Control Systems can improve your cyber posture while also saving time and money. Read MORE Securing Access to Industrial Control Systems…
-
VPN Alternative Access to SCADA Systems
VPN Alternative Access to SCADA Systems. Learn how to enable secure remote access to public sector critical infrastructure and SCADA applications without a VPN.
-
Aligning Critical Infrastructure Security with National Priorities through Zero Trust
Learn how zero trust can help critical infrastructure enhance security and reduce cyber risk without disrupting workflows and operations.
-

Web Application Security – Protecting Against the Top 10 OWASP Threats with Zero Trust
Join us and learn how your organisation can improve web application security and protect against the OWASP Top 10 threats with Zero Trust.
-

How to Connect to SCADA Systems without a VPN
Enable secure connectivity for municipal SCADA systems without a VPN through a Zero Trust Network Architecture.
-

Municipal Cyber Insurance: Improve Security and Meet Minimum Hygiene Requirements
Learn how municipalities can leverage Zero Trust to improve security and meet minimum hygiene requirements for cyber insurance.
-
Eliminating the Business Risk of Shared Credentials
Join us and learn how to eliminate the business risk of shared credentials without burdening your employees or compromising on security.
-

How to Connect to Operational Technology and Critical Systems without a VPN
How to connect to critical systems and operational technology without the need for a VPN. That means authorised users can get the remote access they need without exposing business-critical systems and infrastructure to the public internet.
-
Multi-Factor Authentication for Municipal Cyber Insurance
Join us on December 7 at 1:00pm ET, for an online event where we’ll be diving into Multi-Factor Authentication for Cyber Insurance and what you need to know
-
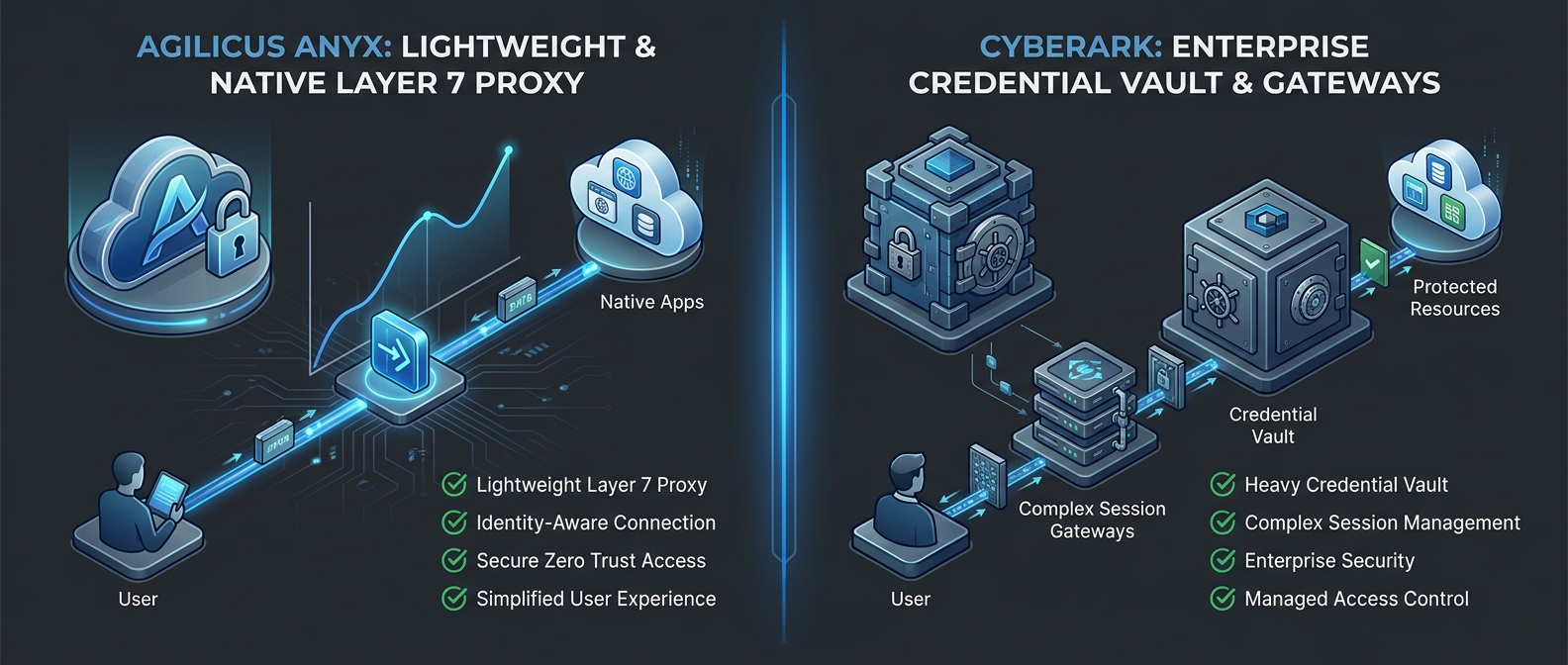
Agilicus vs CyberArk
Compare Agilicus AnyX (native Layer 7 application access) with CyberArk Privileged Access Management (PAM), a vault-centric enterprise credential manager and session proxy. Learn why a software-only, clientless Zero Trust architecture is superior.
-

Agilicus vs Siemens
Compare Agilicus AnyX vs Siemens Smart Server and SINEC Secure Connect. Learn why clientless, identity-aware zero trust access is superior to VNC-based apps and complex network overlays for industrial control systems.
-
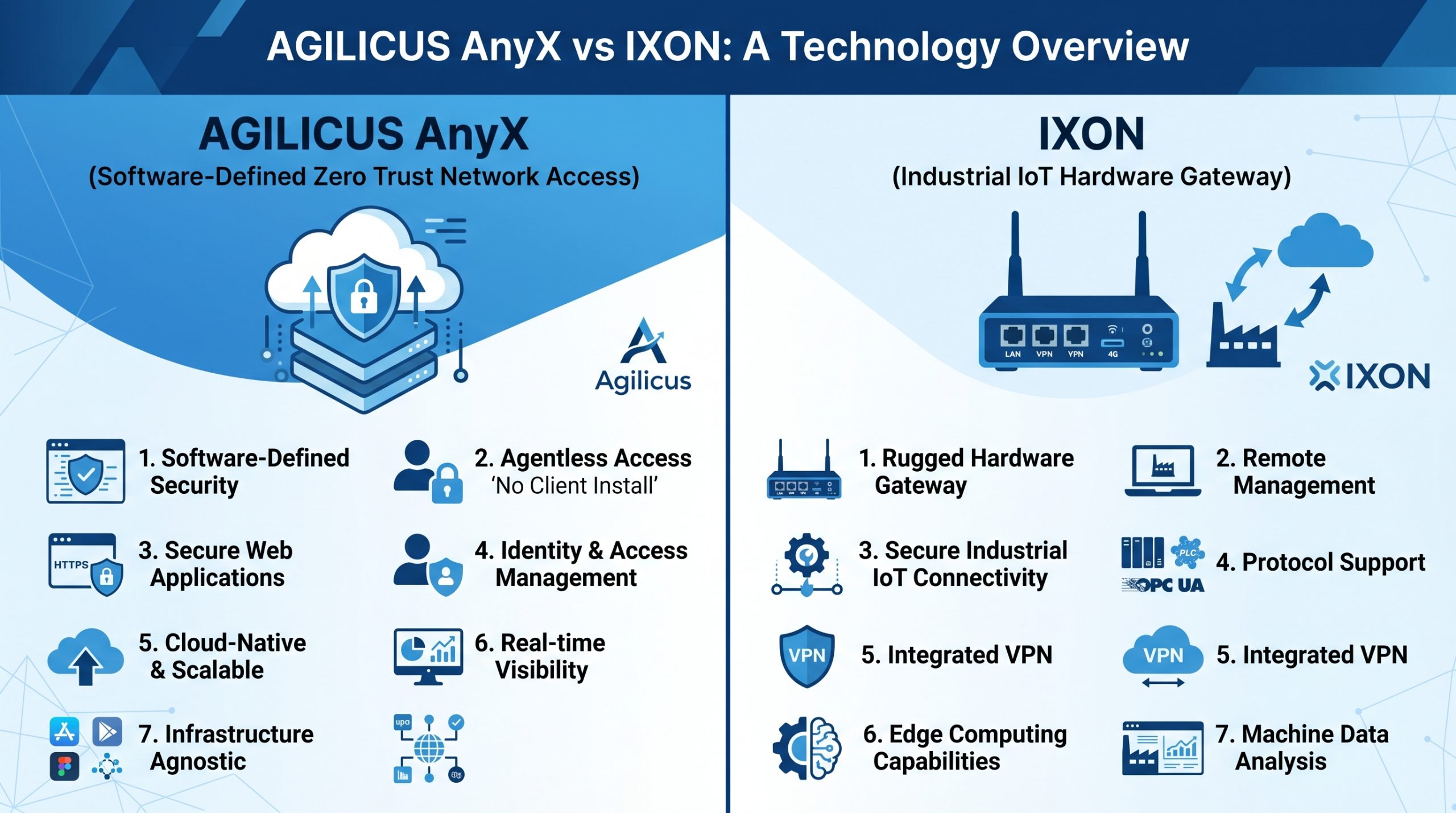
Agilicus vs IXON
Compare Agilicus AnyX vs IXON Cloud. Learn why identity-aware, software-only zero trust access is superior to hardware-based industrial VPNs and IXrouter gateways for machine builders and critical infrastructure.
-
Agilicus vs BlastWave
Compare Agilicus AnyX and BlastWave BlastShield. Discover how Agilicus provides native Layer 7 application access without requiring client-side agents or managing network-level tunnels.
-

Agilicus vs Dull
Compare Agilicus AnyX and Dull. Discover how Agilicus provides native Layer 7 application access without relying on ephemeral virtual machines or jumpboxes.
-
Agilicus vs BeyondTrust Privileged Remote Access
BeyondTrust Privileged Remote Access Provides users with access to shared resources utilizing a Jump box / gateway Architecture. Discover why an identity aware proxy beats a jump box / gateway architecture for secure remote access.
-
Agilicus vs Xona
Xona’s video-streaming approach successfully isolates the network, Agilicus achieves Zero Trust isolation. Discover why an outbound only network is the only secure option for modern remote access tools.
-
Agilicus vs Dispel
Dispel Provides Zero Trust Access to a Virtual Machine, Agilicus Anyx Zero Trust Access Eliminates the Need for One Discover Why Identity-Aware Zero Trust Access Beats a Platform Driven Virtual Machine
-
Agilicus vs Cisco Secure Client
Agilicus AnyX provides a complete Zero Trust platform. Discover why Identity-Aware access beats a socket intercepting VPN agent.
-
Agilicus vs Phoenix Contact mGuard
Compare Agilicus AnyX identity-aware Layer-7 application access with Phoenix Contact mGuard hardware-bound IPsec VPN.
-
Agilicus vs FactoryTalk Remote Access
Compare Agilicus AnyX identity-aware Layer-7 application access with Rockwell Automation’s FactoryTalk Remote Access industrial VPN tunnel.
-
Agilicus vs Secomea
Secomea creates secure OT tunnels. Agilicus AnyX replaces the need for them. Discover why Layer 7 precision and native, multi-provider SSO beats Layer 2/3 connectivity for modern industrial security.
-
Agilicus vs Port Forwarding
Port forwarding exposes internal ports directly to the internet, providing zero authentication, no policy control, and zero audit trails. Agilicus AnyX (Zero Trust) verifies identity and context first, keeping all inbound ports fully closed.
-
Agilicus vs TeamViewer
TeamViewer provides legacy remote desktop access. Agilicus AnyX provides a complete Zero Trust platform. Discover why Identity-Aware access beats shadow-IT backdoors for critical infrastructure.
-
Agilicus vs Claroty xDome Secure Access
Claroty xDome ensures anybody accessing their client is authenticated. Agilicus elimited the needs for clients and encrypted tunnels. Discover why an identity aware proxy beats a dual tunnel architecture for modern security.
-
Agilicus vs Xage
Xage offers complex decentralized access. Agilicus AnyX offers simple, clientless Zero Trust. Discover why straightforward Layer 7 precision beats complex mesh overlays for modern security.
-
Agilicus vs Cloudflare Access
Agilicus AnyX is a complete Zero Trust platform, providing identity based access to shared resources, whereas Cloudflare Access offers Zero Trust to the perimeter, and DNS based access to shared resources.
-
Agilicus vs Tailscale
Tailscale creates a better VPN. Agilicus AnyX replaces the need for one. Discover why Layer 7 precision beats Layer 3 connectivity for modern security.
-
Agilicus vs NetBird
NetBird creates a better VPN. Agilicus AnyX replaces the need for one. Discover why Layer 7 precision beats Layer 3 connectivity for modern security.
-
Agilicus vs ZeroTier
ZeroTier creates a better virtual network. Agilicus AnyX replaces the need for one. Discover why Layer 7 precision beats Layer 2/3 connectivity for modern security.
-
Agilicus vs Johnson Controls Airwall
Compare Agilicus AnyX (identity-native Layer 7 access) with Johnson Controls Airwall (formerly Tempered Networks), a cloaked overlay network.
-
Agilicus vs Tosibox
Tosibox relies on legacy physical hardware and vulnerable client software. Discover how Agilicus AnyX replaces the need for both, providing frictionless, identity-aware Zero Trust access for OT networks without the endpoint risks.
-
Agilicus vs eWon
Compare Agilicus AnyX vs eWon. Learn why identity-aware, software-only zero trust access is superior to hardware-based Layer-3 VPNs and cellular backdoors for industrial remote access.