Category: Defence-In-Depth
Defense In Depth. Don’t spend all your effort on a single moat around the castle, assume each layer of defense will be breached, and have a fallback defensive position.
-
Boundary Defence: The First Layer of Industrial Cyber Security
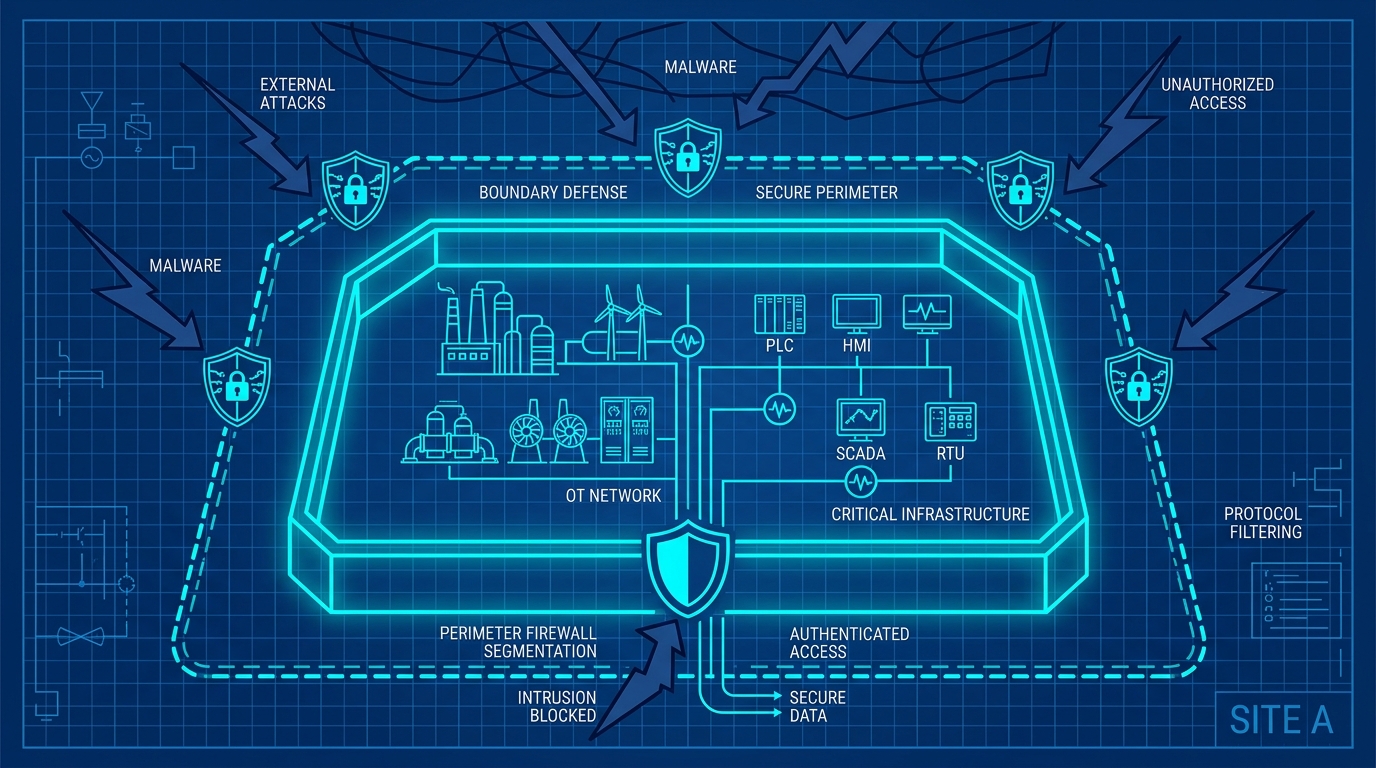 Read more: Boundary Defence: The First Layer of Industrial Cyber Security
Read more: Boundary Defence: The First Layer of Industrial Cyber SecurityModern operational technology environments require robust boundary defence. Learn how to eliminate inbound ports, enforce multi-layer boundaries, and modernise remote access.
-
Assessing Your Industrial Cyber Security Posture
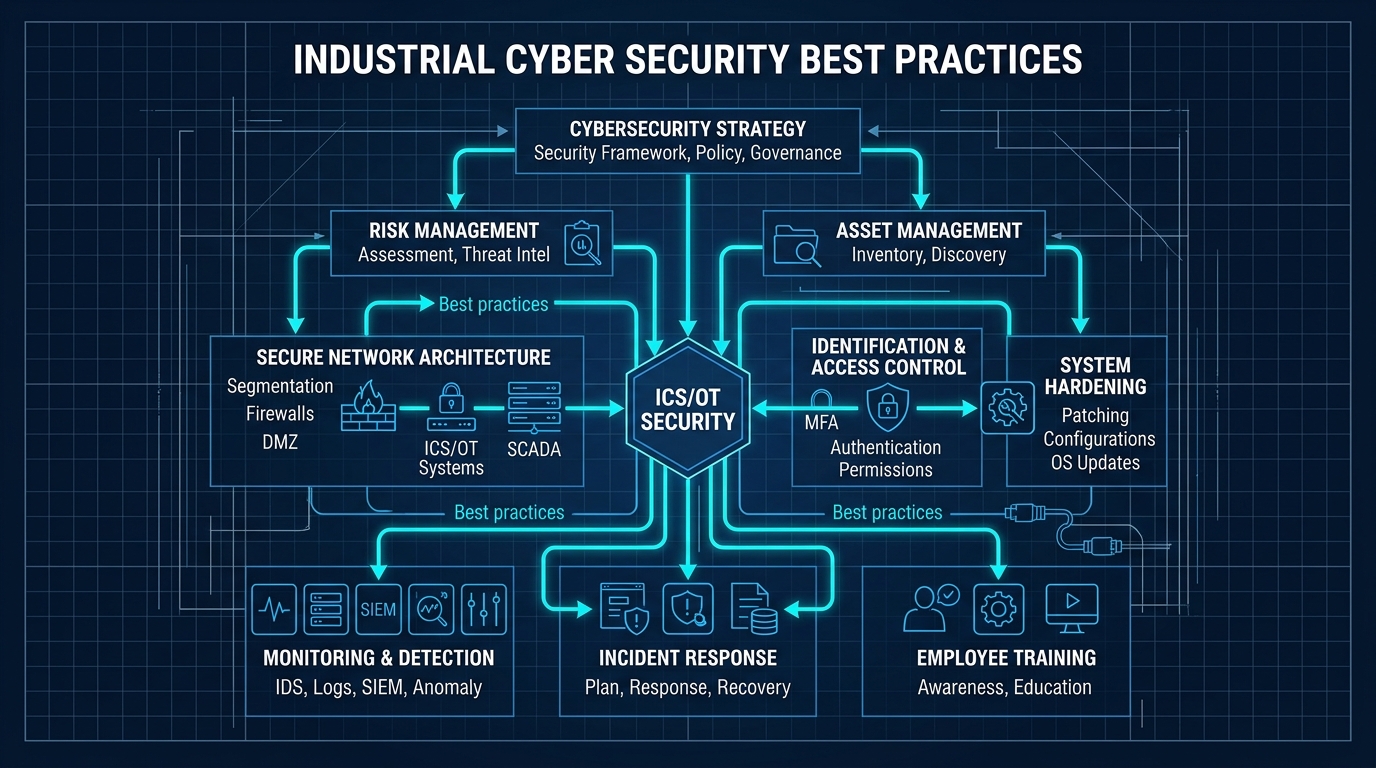 Read more: Assessing Your Industrial Cyber Security Posture
Read more: Assessing Your Industrial Cyber Security PostureThe convergence of operational technology and information technology demands a pragmatic approach. Discover our five-dimensional scorecard to evaluate and improve your industrial cyber security posture.
-
Time To Exploit Approaches Zero
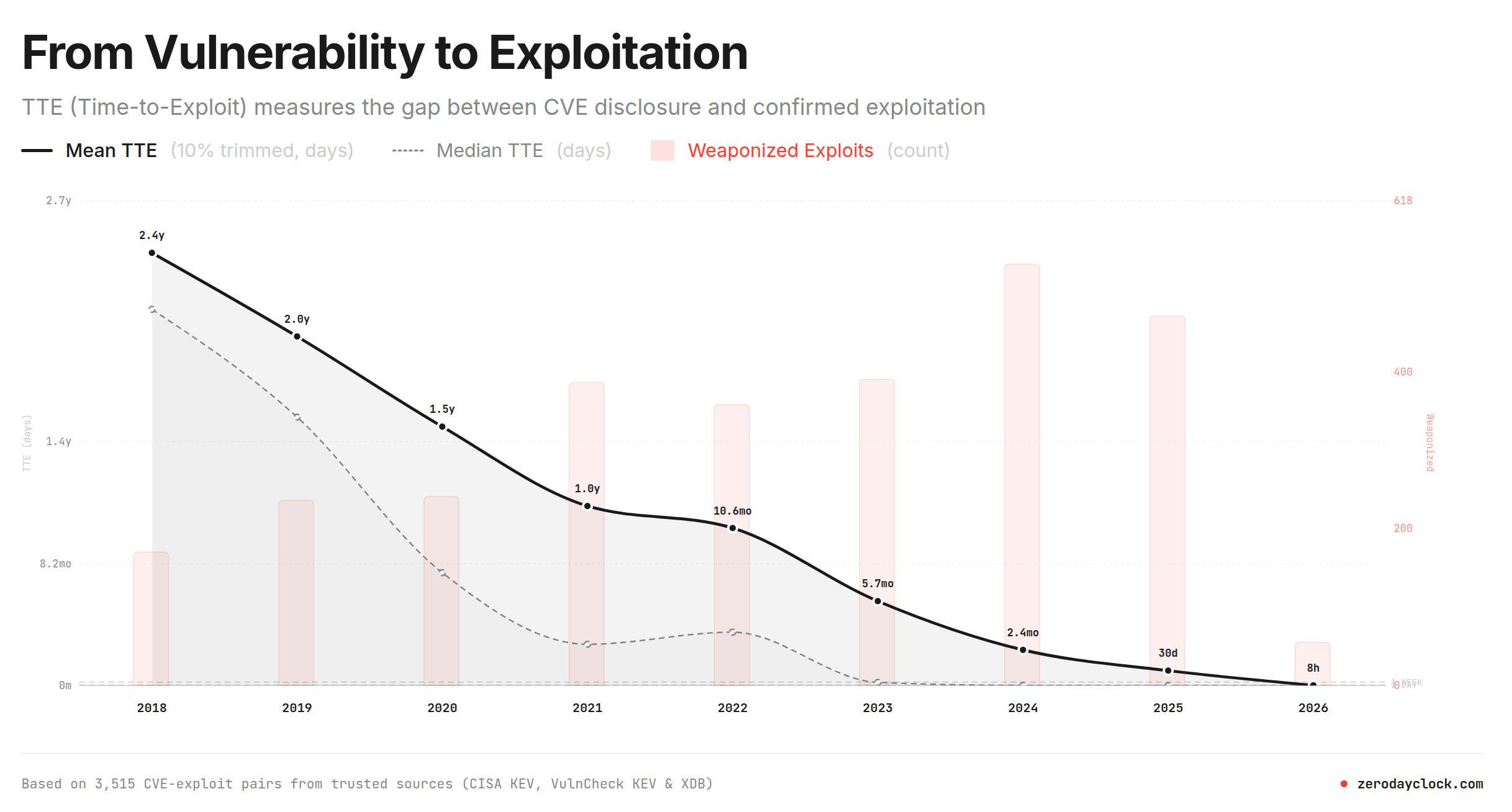 Read more: Time To Exploit Approaches Zero
Read more: Time To Exploit Approaches ZeroThe time between a vulnerability being detected to exploited has been declining. This web site https://zerodayclock.com has a great graph, below. It shows that in 2018 you had 2.5 years from detection to get a fix deployed. This worked its way through your supply chain and you updated. Think of a ‘log4j‘ type vulnerability, its…
-
Agilicus Ready for the Quantum Leap: Securing Today’s Gear from Tomorrow’s Threats
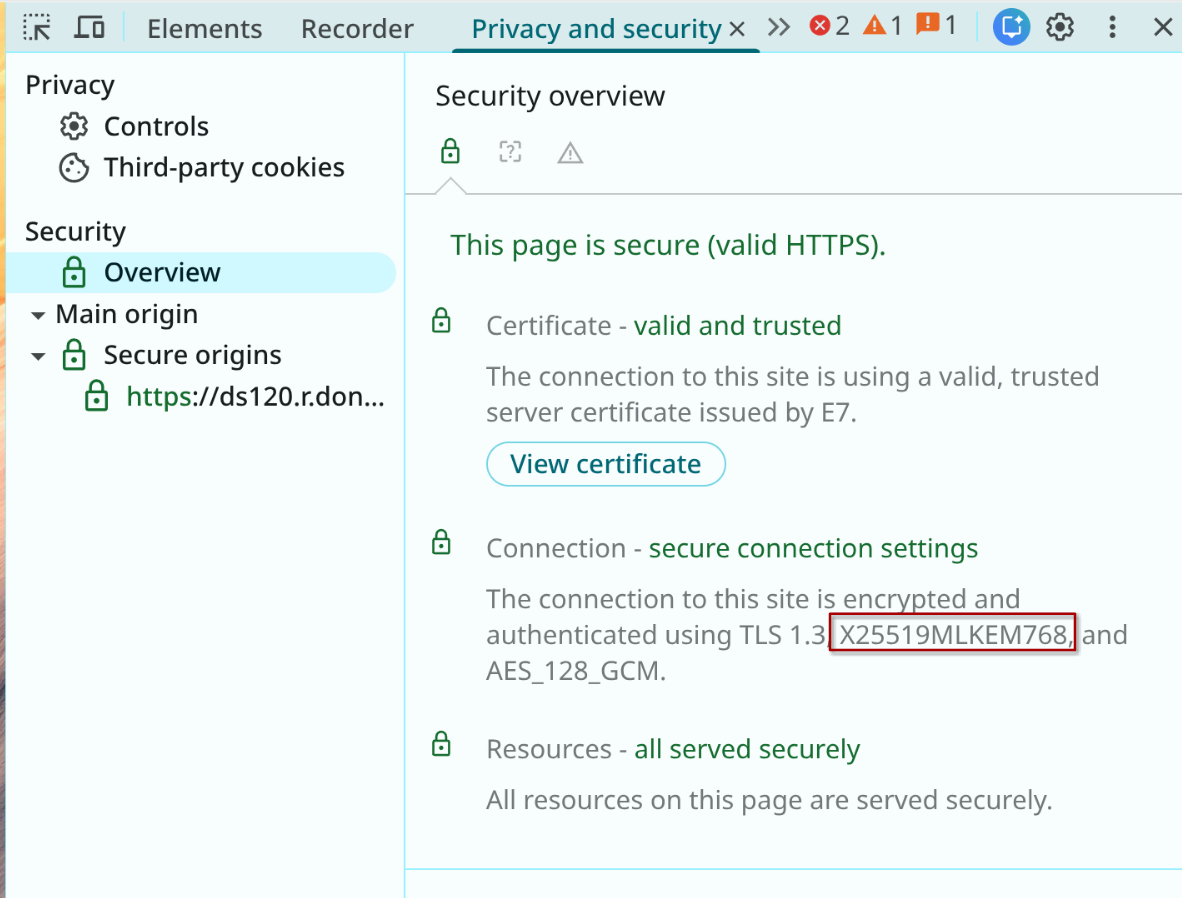 Read more: Agilicus Ready for the Quantum Leap: Securing Today’s Gear from Tomorrow’s Threats
Read more: Agilicus Ready for the Quantum Leap: Securing Today’s Gear from Tomorrow’s ThreatsIt’s a tale as old as time: we build a better lock, and someone, somewhere, starts building a better lock-pick. In the digital world, we’re on the cusp of a monumental leap in lock-picking technology: quantum computing. The cryptographic locks we rely on for everything from banking to binge-watching are in danger of becoming as…
-
Apache Tomcat: Stealthy Risk Vector
 Read more: Apache Tomcat: Stealthy Risk Vector
Read more: Apache Tomcat: Stealthy Risk VectorApache Tomcat. It is an everywhere middleware. And, quelle surprise, the time from disclosure to use is a day. Like log4j it will be with us for some time, so, time for some defence in depth.
-
It’s Been 0-Days Since The Last Municipal Cyber Security Attack
 Read more: It’s Been 0-Days Since The Last Municipal Cyber Security Attack
Read more: It’s Been 0-Days Since The Last Municipal Cyber Security AttackAsymmetric warfare: Big governments attack little governments. Attackers need to be right once, defenders need to be right 24x7x365. Municipalities continue to be a target.
-
FTC To GoDaddy: Heal Thyself
 Read more: FTC To GoDaddy: Heal Thyself
Read more: FTC To GoDaddy: Heal ThyselfFTC orders GoDaddy to improve security, marking an expansion in supply chain hardening tactics of government regulators.
-
Krooked Kriminals Krack Krispy Kreme
 Read more: Krooked Kriminals Krack Krispy Kreme
Read more: Krooked Kriminals Krack Krispy KremeKrispy Kreme materially impacted by cyber security issue, files SEC-8K disclosure.
-
Windows Update Breaks VPN, Good Riddance #zerotrust
 Read more: Windows Update Breaks VPN, Good Riddance #zerotrust
Read more: Windows Update Breaks VPN, Good Riddance #zerotrustMicrosoft Windows Update Breaks VPN for Windows 10 and 11. 3rd party VPN’s have known exploited vulnerabilities. Let’s talk about VPN alternatives!
-
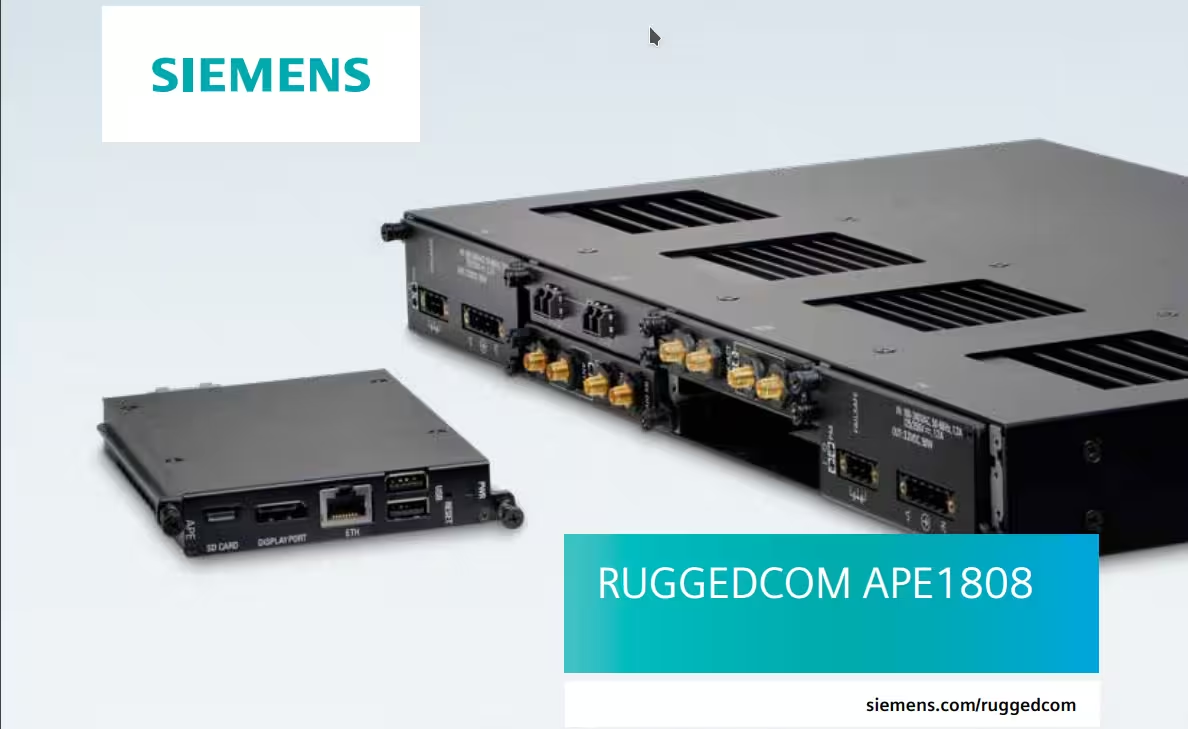
Industrial Supply Chain Matryoshka Risk
 Read more: Industrial Supply Chain Matryoshka Risk
Read more: Industrial Supply Chain Matryoshka RiskLast weeks hyper-critical NGFW vulnerability is this weeks embedded operational technology challenge due to nested risk and supply chain.
-
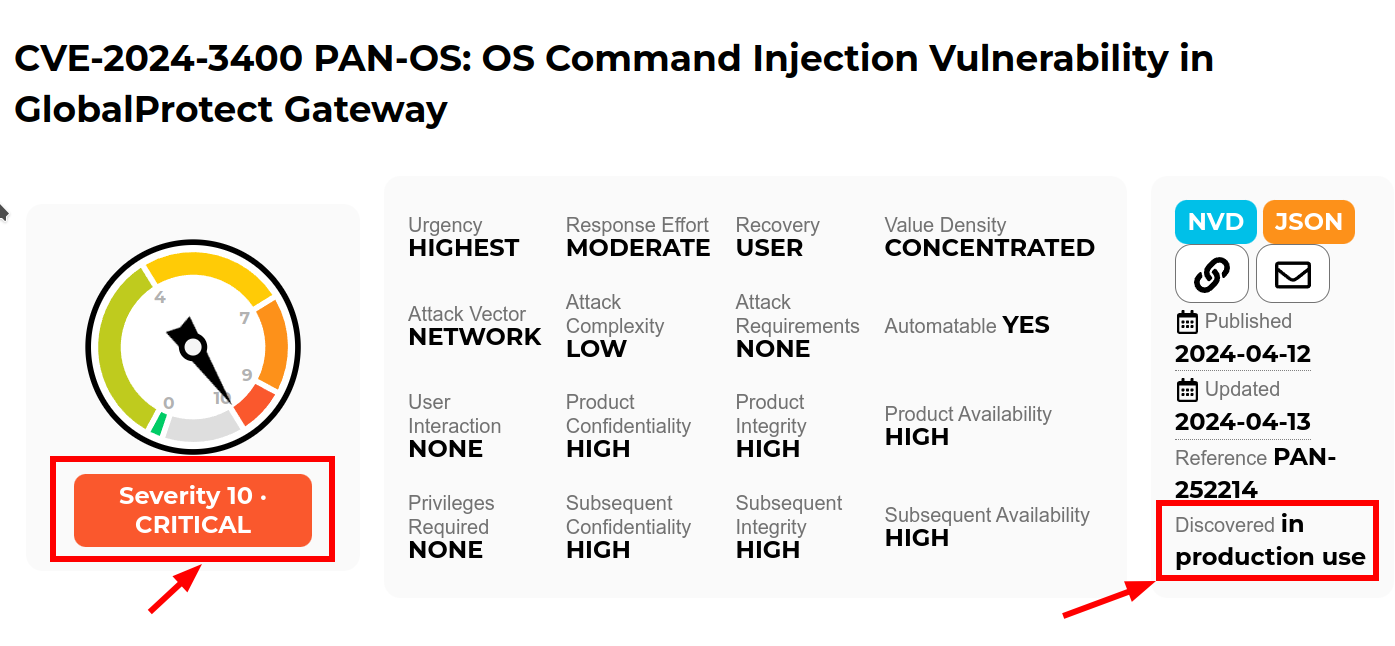
Quis custodiet ipsos custodes: When Good Firewalls Go Bad
 Read more: Quis custodiet ipsos custodes: When Good Firewalls Go Bad
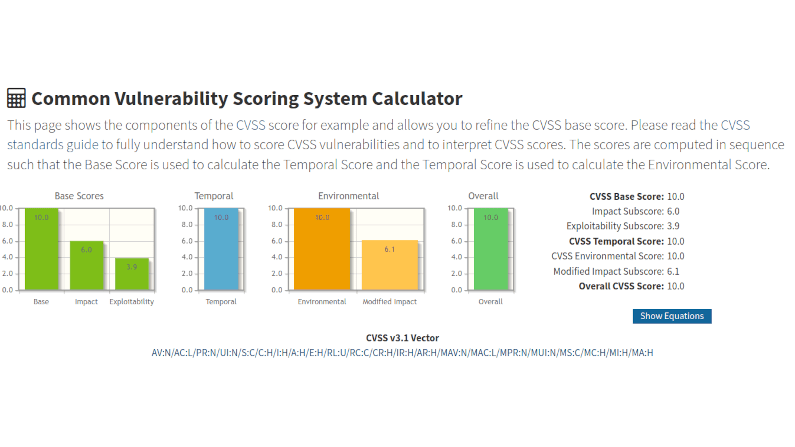
Read more: Quis custodiet ipsos custodes: When Good Firewalls Go BadRecently Palo Alto announced a 10.0 CVE in the Global Protect feature of their PAN-OS firewall. “Unauthenticated attacker [can] execute arbitrary code with root privileges on the firewall”. Well, that is not good. But, how “not good” is it? It’s terrifyingly bad ungood in fact.
-
Three Strategies To Help: Cisco ASA AnyConnect and WebVPN added to CISA Known Exploits
 Read more: Three Strategies To Help: Cisco ASA AnyConnect and WebVPN added to CISA Known Exploits
Read more: Three Strategies To Help: Cisco ASA AnyConnect and WebVPN added to CISA Known ExploitsCisco ASA AnyConnect and WebVPN added to CISA Known Exploits. Do you have one running on autopilot in your plant somewhere? Maybe between the IT and OT network? Maybe running the DMZ?
-
Ground Hog Day: Fortinet VPN Edition
 Read more: Ground Hog Day: Fortinet VPN Edition
Read more: Ground Hog Day: Fortinet VPN EditionAnother day, another VPN letting the world in to snoop around and fondle your crown jewels: Fortinet edition.
-
Dutch Defence Detail Dastardly Dirty Deed
 Read more: Dutch Defence Detail Dastardly Dirty Deed
Read more: Dutch Defence Detail Dastardly Dirty DeedThe Netherlands ministry of defence just published the cliff-hanger document TLP:CLEAR MIVD AIVD Advisory COATHANGER regarding a remote access attack of their Fortinet FortiGate VPN by “a state-sponsored actor from the People’s Republic of China”. CVE-2022-42475 was the weakness. One thing that is unusual about the report is the direct attribution: this is rare.
-
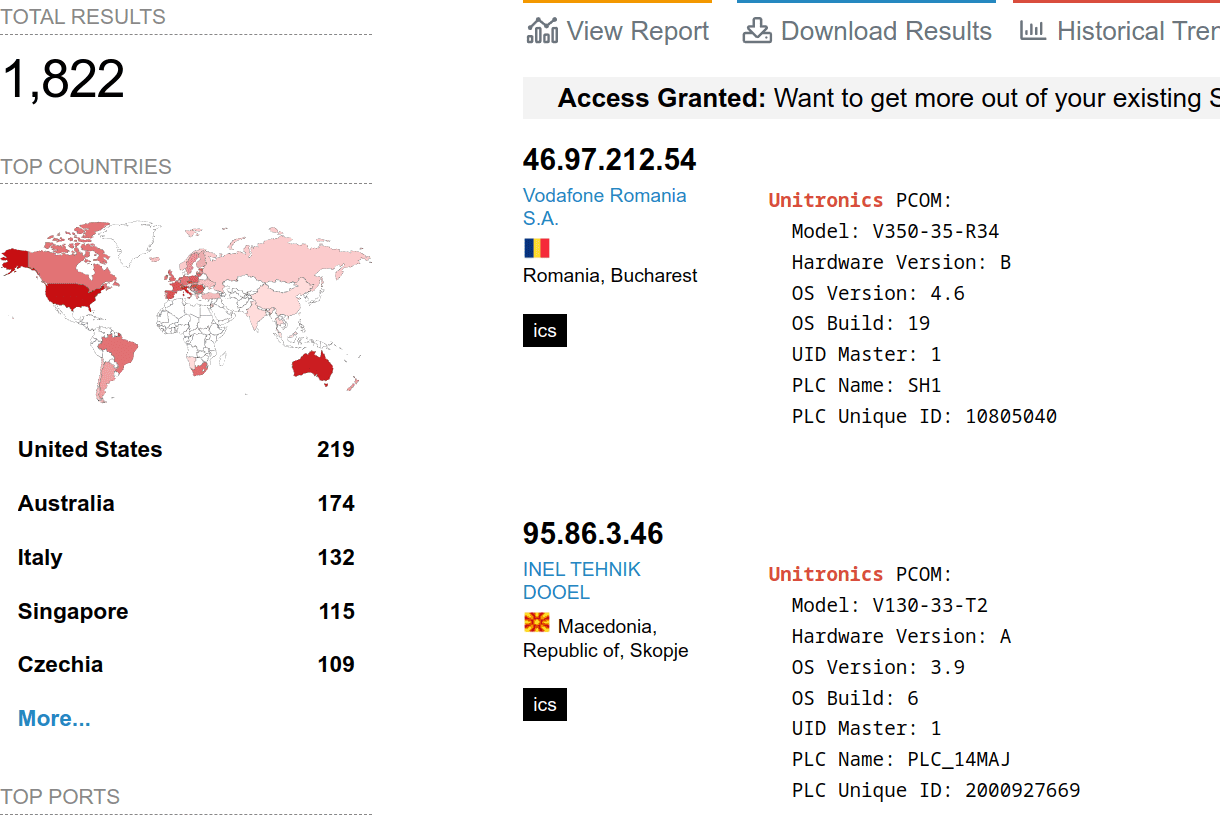
Howto: Open Source Intelligence and your Digital Footprint
 Read more: Howto: Open Source Intelligence and your Digital Footprint
Read more: Howto: Open Source Intelligence and your Digital FootprintLet me show you a very simple means of Open Source Intelligence (OSINT) on yourself. If I can do this, anyone can do this, and if anyone can do this, someone bad can do this.
-
Off-Grid Agricultural Cyber Physical Systems
 Read more: Off-Grid Agricultural Cyber Physical Systems
Read more: Off-Grid Agricultural Cyber Physical SystemsThe “John Deere Business Model” of taking something traditional and making it subscription. Starlink and its complex remote access needs due to CGNAT. And, cybersecurity, notably Cyber Physical Systems with their scary downsides of being able to move and cause damage.
-
Hard Industrial Cybersecurity is hardly secure, nuclear waste edition
 Read more: Hard Industrial Cybersecurity is hardly secure, nuclear waste edition
Read more: Hard Industrial Cybersecurity is hardly secure, nuclear waste editionOne thing all industrial control installations have in common, they straddle the complexity of modern information technology with the dangers of operational technology and its inherent control of things which can go bump and boom. Hard Industrial Cybersecurity
-
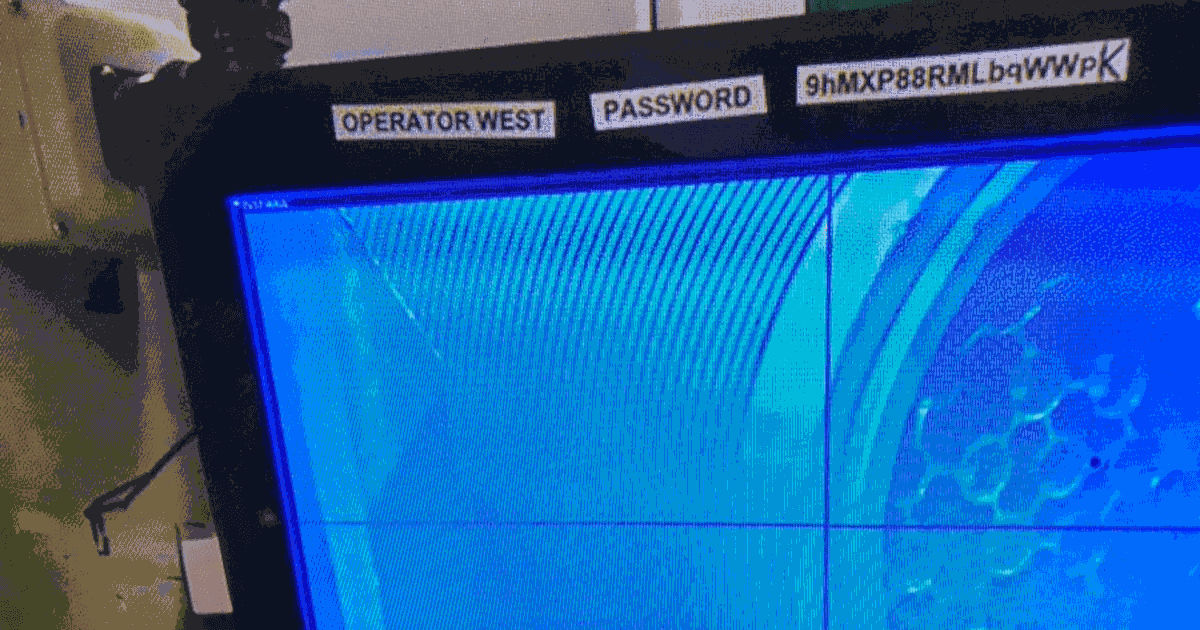
Avoid Exploitation of Unitronics PLCs used in Public Water Systems
 Read more: Avoid Exploitation of Unitronics PLCs used in Public Water Systems
Read more: Avoid Exploitation of Unitronics PLCs used in Public Water SystemsExploitation of Unitronics PLCs used in Public Water Systems for political purposes. Recommendations.
-
Attainable Municipal Zero Trust
 Read more: Attainable Municipal Zero Trust
Read more: Attainable Municipal Zero TrustAttainable Municipal Zero Trust: Key insights from recent Zero Trust implementations by Municipalities. Why, How, What ROI, Lead use cases.
-
CISA Cyber Scan Water
 Read more: CISA Cyber Scan Water
Read more: CISA Cyber Scan WaterCISA has announced a free (as in beer) service to scan water systems for vulnerabilities. Agilicus has used this scan for a year, receiving weekly reports.
-
Terminator Becomes National Standard
 Read more: Terminator Becomes National Standard
Read more: Terminator Becomes National StandardI’ll be back. Iconic line foreshadows rise of cyber-physical-systems. Terminator trifecta of physical machines, artificial intelligence, cyber-security awry.
-
Another Day, Another Exploit – Protecting Against the ProxyNotShell Exchange Server Zero-Day Vulnerability
 Read more: Another Day, Another Exploit – Protecting Against the ProxyNotShell Exchange Server Zero-Day Vulnerability
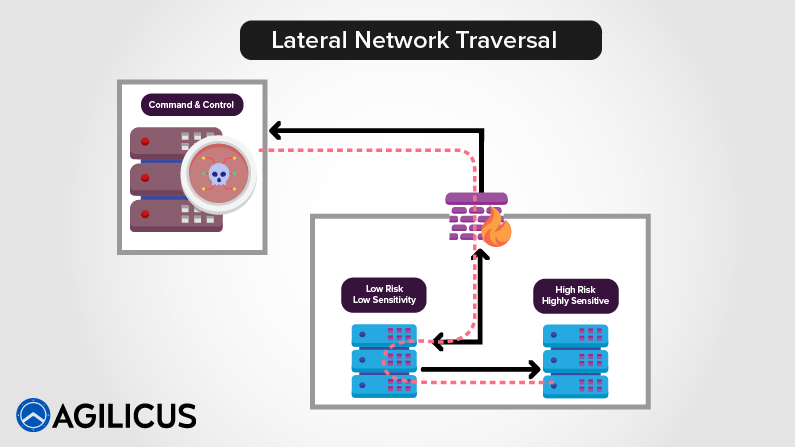
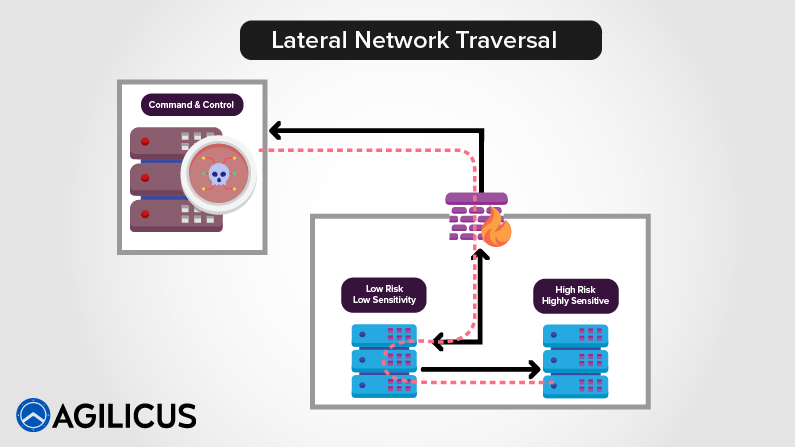
Read more: Another Day, Another Exploit – Protecting Against the ProxyNotShell Exchange Server Zero-Day VulnerabilityLearn how zero trust protects against the new Microsoft Exchange Server zero-day exploit affecting Outlook Web Access (OWA), ProxyNotShell. With Agilicus, you’ll block lateral traversal and prevent unauthorised traffic from arriving at your resources while ensuring they are still accessible to legitimate users.
-
Well Timed or Coincidental, Cue the Phishing Attacks as 2.5M Students Affected by Data Breach
 Read more: Well Timed or Coincidental, Cue the Phishing Attacks as 2.5M Students Affected by Data Breach
Read more: Well Timed or Coincidental, Cue the Phishing Attacks as 2.5M Students Affected by Data BreachDays after announcing student loan forgiveness in the United States, 2.5 million student borrowers had their personal information exposed in a data breach and are at an increased risk of being targeted in a phishing attack.
-
Protecting Against the OWASP Top 10 Web Application Vulnerabilities
 Read more: Protecting Against the OWASP Top 10 Web Application Vulnerabilities
Read more: Protecting Against the OWASP Top 10 Web Application VulnerabilitiesThe OWASP Top 10 is a standard awareness document that outlines the most critical web application security risks and vulnerabilities. Learn how Agilicus AnyX is designed to eliminate an attacker’s visibility into the potential OWASP Top 10 web application vulnerabilities.
-
570 News Agilicus Interview
 Read more: 570 News Agilicus Interview
Read more: 570 News Agilicus InterviewInterviewed on 570 News Tech Spotlight. listen to the interview here, I talk through some of the simple risks and how we help. And a bear joke.
-
Chewy Centre Protected By A Sponge
 Read more: Chewy Centre Protected By A Sponge
Read more: Chewy Centre Protected By A SpongeThe M&M is not a good network design: chewy centre, hard shell. Recent cisco router vulnerabilities discussed for defense in depth.
-
Log4Shell – Not Even the Smart Thermostat is Safe
 Read more: Log4Shell – Not Even the Smart Thermostat is Safe
Read more: Log4Shell – Not Even the Smart Thermostat is SafeIgnoring systems that may be deemed ‘unimportant’ in comparison to your revenue-generating technology stack will leave your organization open to compromise from the Log4Shell vulnerability.
-
A Little Consequences Go A Long Way: Return Of The Bear Joke
 Read more: A Little Consequences Go A Long Way: Return Of The Bear Joke
Read more: A Little Consequences Go A Long Way: Return Of The Bear JokeTwo hikers see a bear. One bends over to tie shoes. Other says, you can’t out run a bear. First says, just need to outrun you. Pause laughter
-
Fake It Till You Make It: Canadian Bank Multi-Factor Authentication Edition
 Read more: Fake It Till You Make It: Canadian Bank Multi-Factor Authentication Edition
Read more: Fake It Till You Make It: Canadian Bank Multi-Factor Authentication EditionA big 5 Canadian bank has a fake multi-factor authentication sytem, allowing anyone to fall back to password. Why? How is this acceptable?
-
The Economic Cost Of Not Having Multi-Factor: MSP Lawsuit Edition
 Read more: The Economic Cost Of Not Having Multi-Factor: MSP Lawsuit Edition
Read more: The Economic Cost Of Not Having Multi-Factor: MSP Lawsuit EditionManaged Service Provider Breached. Customer pays out. Who is at fault? Lawsuit to determine. Multi-factor authentication to prevent.