I’ll be back. An iconic line delivered in a memorable Austrian accent, foreshadowing the actual rise of cyber-physical systems. In the Terminator franchise, we saw for the first time the trifecta of physical machines, artificial intelligence, and, cyber-security gone awry. Science fiction moved from the War Operation Plan Response (WOPR) of the 1983 film WarGames (which merely thought about wars) to physical machines that could do something about it. While this is all good fun in a theatre, it’s now becoming a reality. And all good realities need succinct standards to guide them towards good from evil. Into this gap has emerged NIST with an update to NIST SP 800-82, expanding its scope to include these cyber-physical systems as well as building management systems and other operational technology goodness.
NIST SP 800-82 Rev 3
One of the main changes in the upcoming revision three of NIST SP 800-82 is an expansion in scope. Industrial Control Systems are a part of the greater Operational Technology (we explain this acronym soup in more detail in Piercing The Purdue Model:
Zero Trust In Operational Technology) rubric, which also includes Distributed Control Systems, Building Management Systems, etc., as well as updates to threats, vulnerabilities, risk management, and best practices. Of particular interest is the alignment to the NIST Cybersecurity Framework (CSF), which I believe is a lot more manageable and achievable for many companies. NIST CSF is also in the process of a major revision to 2.0, adding a Govern function.
Coverage
The scope of NIST SP 800-82 Revision 3 (Draft) has been broadened to include not only traditional Industrial Control Systems (ICS) used in critical infrastructure sectors but also emerging technologies like the Industrial Internet of Things (IIoT) and other systems such as Building Automation Systems (BAS) and Physical Access Control Systems (PACS). The term “Operational Technology” (OT) is now used to refer to these broader systems, including Industrial Control Systems as one of the main entities. This acknowledges the evolving threat landscape and the need for enhanced security measures.
The addition of Building Automation Systems and Physical Access Control Systems moves this from solely critical infrastructure sectors (water, energy, and transportation) into everyday life (malls, apartment buildings, and office buildings).
Risk
Risk Management: The new version emphasizes a risk-based approach to cybersecurity. It introduces the concept of risk management frameworks, which help organizations identify and prioritize potential threats and vulnerabilities. This approach enables more targeted and effective security measures.
Response Plan
Enhanced Incident Response: The latest version places greater emphasis on incident response and recovery. It provides detailed guidance on developing and implementing robust incident response plans specific to Operational Technology environments. This helps organizations minimize the impact of cybersecurity incidents and restore operations quickly.
Integration
Integration with Cybersecurity Framework (CSF): NIST SP 800-82 Revision 3 (Draft) aligns with the NIST Cybersecurity Framework (CSF), providing a cohesive approach to managing cybersecurity across an organization. This integration allows organizations to leverage existing CSF practices and frameworks to secure their Operational Technology environments.
Supply Chain
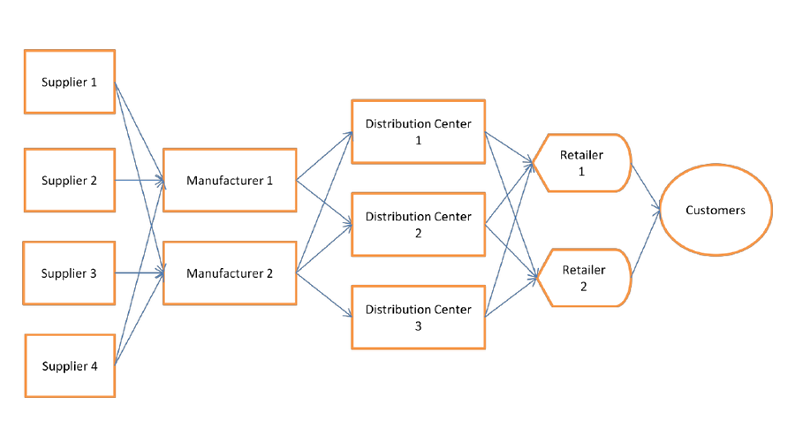
Supply Chain Security: NIST SP 800-82 Revision 3 (Draft) recognizes the importance of securing the supply chain, particularly for Operational Technology environments. It provides guidance on assessing and managing risks associated with third-party suppliers, ensuring that the software and hardware components used in Operational Technology systems are trustworthy and free from vulnerabilities.
I’ve talked many times about supply chain, e.g. “Multi-Factor Authentication and the Supply Chain“, but it remains one of the more pervasive and complex problems to solve, both on the technology side (their code inside the code of my vendor), but also on the people side (their staff supports my site).
Access
Access Control and Authentication: The new version emphasizes the importance of access control and strong authentication mechanisms. It provides guidance on implementing multi-factor authentication, password management, and user access controls. These measures help prevent unauthorized access and enhance the overall security posture.
As you can likely see by watching my video about this topic, this is an area our team at Agilicus is very passionate about.
Threat
Threat Intelligence and Monitoring: NIST SP 800-82 Revision 3 (Draft) emphasizes the need for continuous monitoring and threat intelligence. It provides guidance on implementing security controls and tools to detect and respond to potential threats in real time. This proactive approach enables organizations to stay ahead of emerging threats.
Controls
There is new tailoring guidance for NIST SP 800-53, Rev. 5 security controls with an Operational Technology overlay that provides mapped security control baselines for low-impact, moderate-impact, and high-impact Operational Technology systems.
I have covered some of the mappings between SP 800 53 and Zero Trust, and some of the risks it seeks to control, including some mappings in “NIST SP 800 53 Mapping To Zero Trust“
Program
The NIST SP 800-82 Rev 3 refers to ISA-62443-2, which I have covered in “Industrial Zero-Trust Micro-Segmentation:
Leverage Identity To Simplify IEC-62443 Zones“, giving guidelines on how to fulfill the cybersecurity requirements are described for each element of the cybersecurity program.
Conclusions
I covered a lot, but the standard covers even more. I find each of these standards pretty accessible, I recommend starting with the Cybersecurity Framework, followed by the NIST SP 800-82. Even if only to understand and assess the risks you face that you might be unaware of, these are worth reading.
