In the early innocent days of the Internet a few protocols reigned supreme. Telnet. SMTP. Both were architected with negligible security, it was a simpler time, people were more worried about the impending death of disco and where to buy leg warmers.
Fast forward 40 years. SMTP has been hardened via a variety of bolt-on solutions. SPF, DMARC, DKIM, TLS, etc. It now suffices. Telnet? Not so much. Open port 23 and start typing. So it should come as no surprise that I (and everyone else) suggests: get rid of it. You cannot secure it no matter how much fancy firewall and multi-factor authentication you put in front. And, this is not new advice, you’ve had years to delete this protocol from your fleet.
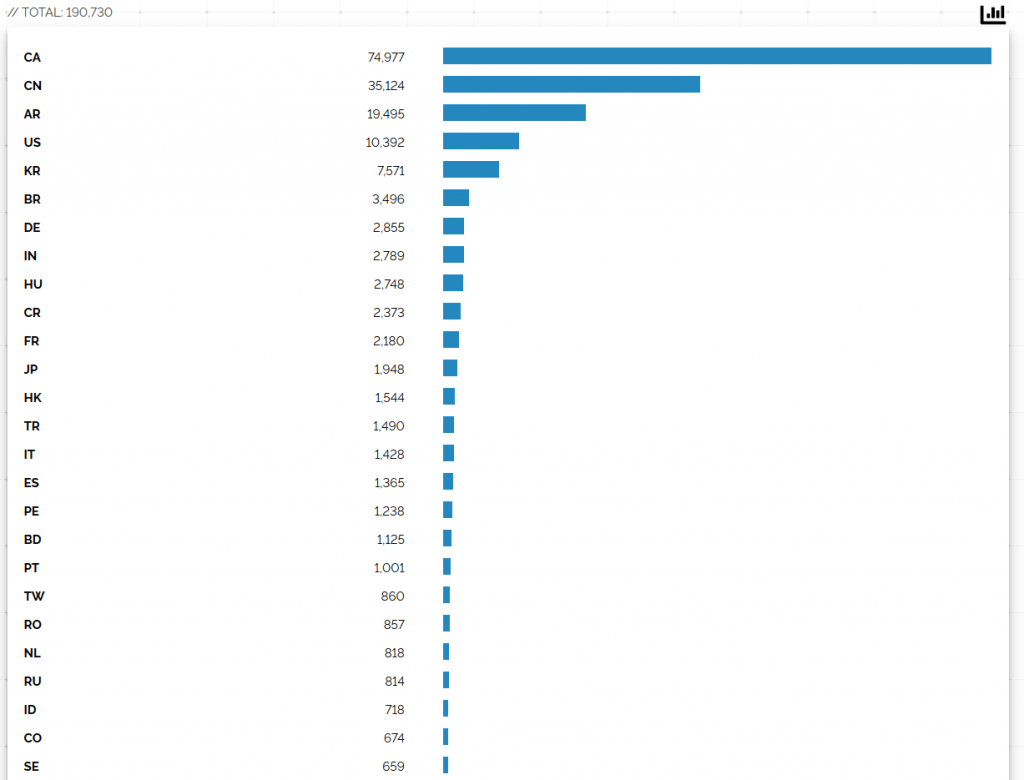
So it surprised me substantially today when, as I was explaining what Telnet was to someone who was not yet around in when Tron premiered and Telnet launched, I opened Shodan to show how dead it was… and… Sacre Bleu! There it is. Starting me in the face. Not only is Telnet alive, but, Canada is half of the worlds Telnet.
What can possibly be the reason the Great White North is a safe-haven for the devil’s port? TekSavvy and Primus are the majority. Perhaps they don’t filter port 23 and all the other worlds’ ISPs do? Perhaps Tim Horton’s uses it in Point-Of-Sale? What can be the reason?
When we look at risky protocols (like Telnet), we often think about ‘mitigation’. E.g. smart firewalls, forced multi-factor, nonce-based-one-time-passwords.
But when the underlying transport is insecure, the option negotiation is fraught with peril, the password is in the clear, and, well, SSH exists, there is just no reason.
Friends don’t let friends run Telnet. If you know why its still alive here, drop me a line.