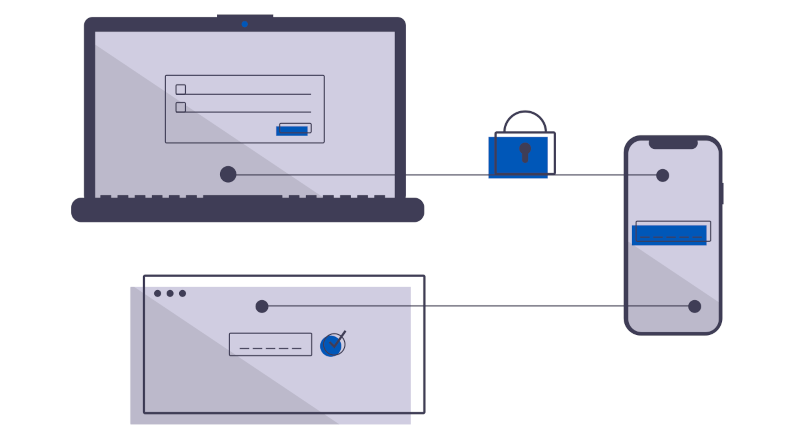
Your cyber insurance is up for review. If you can get all applications authenticated with multi-factor, you can afford it. But, you have only managed to get the new ones done, leaving the miscellaneous. Let’s talk about how an authenticating proxy can get the rest done, with no work, no fuss. Become compliant right quick.
Learn More?
Recent Articles
-
Boundary Defence: The First Layer of Industrial Cyber Security
-
Assessing Your Industrial Cyber Security Posture
-
Iran Attacking Water facilities PLC: Why defence in depth is no longer optional for PLCs
-
Time To Exploit Approaches Zero
-
NERC CIP 015-2 expands network monitoring: How zero trust secures the new perimeter
-
NERC CIP-003-9: Why your VPN is a compliance dumpster fire