Industrial Cybersecurity Best Practices
- Assessing Your Industrial Cyber Security Posture
- Boundary Defence: The First Layer of Industrial Cyber Security
- Identity and Credentials: The New Air Gap
- Halting Lateral Movement in Operational Technology
- System Hardening: Fortifying Industrial Infrastructure
- Visibility and Detection: Illuminating the Industrial Network
- A Pragmatic Blueprint for Industrial Cyber Security
Welcome to the final post in our seven-part series on industrial cyber security best practices. Over the last few weeks, we have unpacked the reality of securing hybrid Information Technology and Operational Technology environments. We have moved past the myth of the air gap and confronted the technical friction caused by connected industrial control systems.
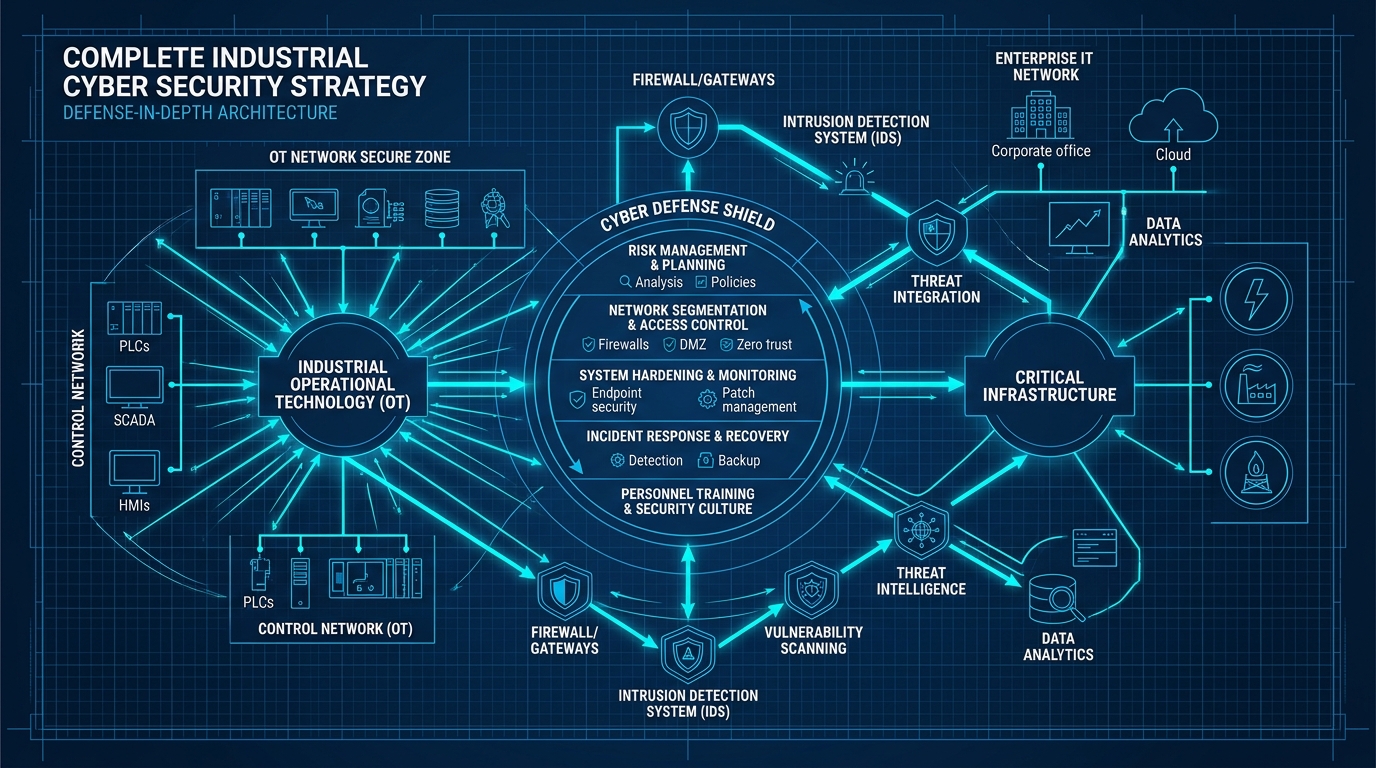
The core philosophy we have explored is the necessity of orthogonal defences. No single security control is absolute. Every perimeter, no matter how robust, will eventually face a threat it was not designed to handle. If you rely solely on a firewall, a stolen password renders it useless. If you rely solely on multi-factor authentication, an unpatched vulnerability bypasses the login screen entirely.
To build true resilience, we must stack multiple, independent layers of defence. As we have discussed, this is the Swiss cheese model in action. When the holes in one layer are bypassed, the next layer must catch the threat using an entirely different mechanism. Our program distils this strategy into five distinct dimensions.
Reviewing the Five Dimensions
- Boundary Defence: We established that flat networks are an open invitation for total compromise. By enforcing strict logical separation, eliminating open inbound ports, and replacing legacy remote access with outbound-only reverse tunnels, we create structural friction at the edge of the network.
- Identity and Credentials: We recognised that identity is the new air gap. By mandating phishing-resistant multi-factor authentication, unifying corporate directories, and enforcing least privilege authorisation, we ensure that an attacker who bypasses the network boundary is immediately halted by robust identity controls.
- Lateral Movement: We addressed the scenario where a threat actor breaches the perimeter and steals a credential. By deploying network micro-segmentation and eradicating legacy protocols like Remote Desktop Protocol, we contain the blast radius, preventing the attacker from navigating to critical process controllers.
- System Hardening: We looked at the assets themselves. By eradicating default credentials, disabling unused services, and implementing application allowlisting, we reduce the attack surface of individual devices, ensuring they are inherently resilient against exploitation.
- Visibility and Detection: Finally, we acknowledged that preventative controls will eventually fail. By implementing continuous asset discovery, industrial-aware network monitoring, and centralised log aggregation, we illuminate the network, allowing for rapid detection and response before a cyber event becomes a physical disaster.
The Path Forward
These five dimensions are not a binary checklist to complete once and forget. They represent a strategic architectural roadmap to govern your ongoing security investments. They provide a pragmatic approach for mid-market companies to reduce risk and increase control without crippling operational efficiency.
The threats facing critical infrastructure are not theoretical. As highlighted by the Cybersecurity and Infrastructure Security Agency’s Risk and Vulnerability Assessments, adversaries are actively exploiting weak boundaries and compromised credentials. However, the defences are entirely within your control.
Your next step is to measure your current posture against this blueprint. We urge you to take our Cyber Security Assessment. This scorecard will benchmark your environment against these five orthogonal dimensions, highlighting your specific gaps. Once completed, you will be directed to download the full Industrial Cyber Security Best Practices guide, providing the actionable roadmap to address those vulnerabilities.
Do not wait for an incident to test your defences. Implement orthogonal controls, secure your hybrid environment, and ensure the resilience of your operations. Take the assessment today.
Industrial Cybersecurity Best Practices
- Assessing Your Industrial Cyber Security Posture
- Boundary Defence: The First Layer of Industrial Cyber Security
- Identity and Credentials: The New Air Gap
- Halting Lateral Movement in Operational Technology
- System Hardening: Fortifying Industrial Infrastructure
- Visibility and Detection: Illuminating the Industrial Network
- A Pragmatic Blueprint for Industrial Cyber Security