Industrial Cybersecurity Best Practices
- Assessing Your Industrial Cyber Security Posture
- Boundary Defence: The First Layer of Industrial Cyber Security
- Identity and Credentials: The New Air Gap
- Halting Lateral Movement in Operational Technology
- System Hardening: Fortifying Industrial Infrastructure
- Visibility and Detection: Illuminating the Industrial Network
- A Pragmatic Blueprint for Industrial Cyber Security
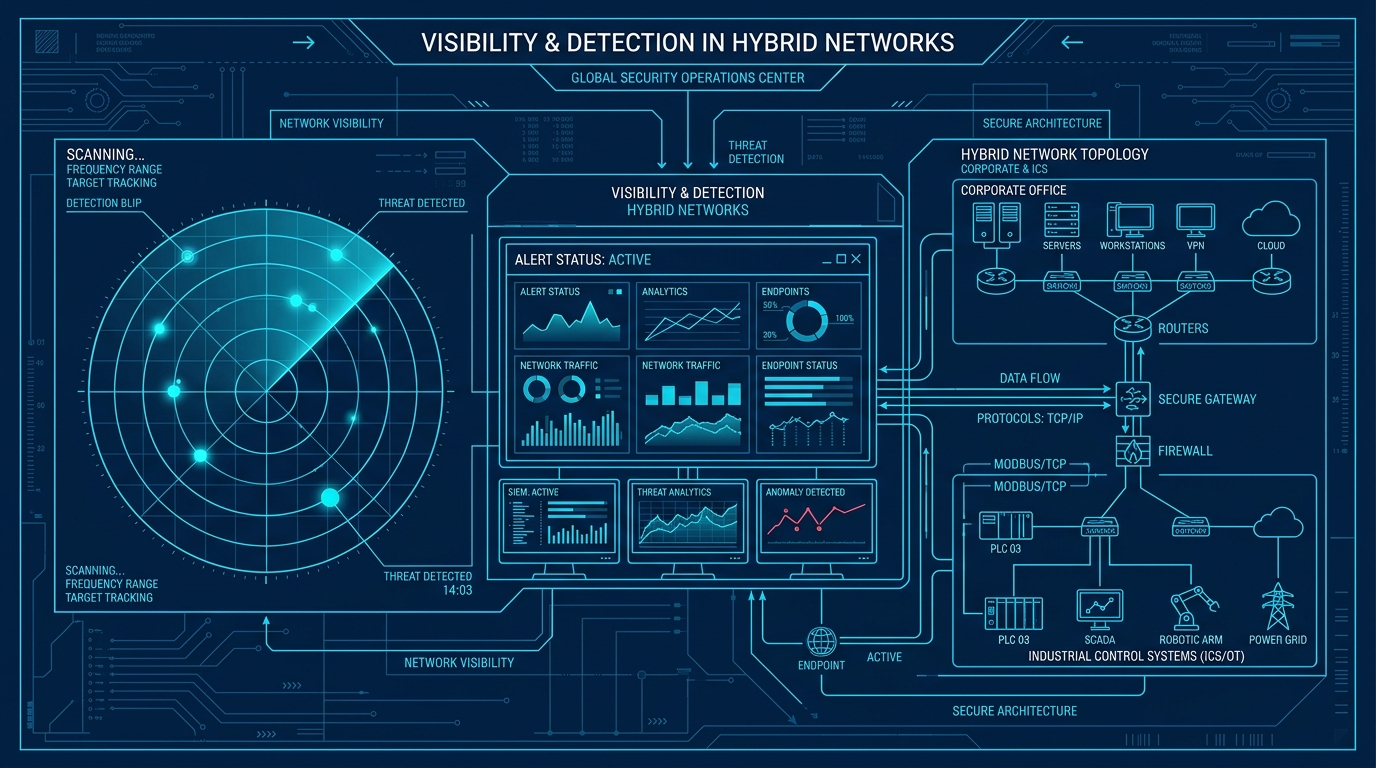
Welcome to the sixth post in our series on industrial cyber security best practices. We have covered the preventative controls: boundaries, identity, lateral movement, and system hardening. Today, we address the reality that preventative controls can, and eventually will, fail. This brings us to the fifth orthogonal dimension: Visibility and Detection.
You cannot protect what you cannot see. In many operational technology environments, the network is a black box. If an adversary bypasses the perimeter and begins communicating with a programmable logic controller using native industrial protocols, the business is completely blind. Visibility and detection represent the crucial ability to identify a breach in its early stages, allowing for rapid response before a cyber event becomes a physical disaster.
Asset Inventory and Discovery
The foundation of visibility is an accurate asset inventory. You cannot detect an anomalous device if you do not know what devices are supposed to be there. In industrial environments, rogue laptops, undocumented cellular modems, and forgotten test equipment frequently blur the network topology.
Continuous, passive asset discovery is required to illuminate the environment. By listening to network traffic, you can automatically build a dynamic inventory of every device, its firmware version, and its communication patterns. This is the baseline upon which all detection capabilities are built.
Network Security Monitoring
Traditional Information Technology monitoring focuses on corporate web traffic and email. Operational Technology monitoring must understand industrial protocols like Modbus, DNP3, and Ethernet/IP. An attacker altering the setpoint of a safety valve will not trigger a standard corporate intrusion detection system; it simply looks like standard network traffic.
Deploying network security monitoring specifically designed for industrial environments is essential. These systems parse deep packet inspection to identify malicious commands, firmware uploads, or abnormal reads and writes to process controllers. This deep visibility is the only way to detect threat actors living off the land within the industrial control system.
Centralised Log Aggregation
When investigating an incident, piecing together logs from disparate firewalls, Windows servers, and identity providers is a painstakingly slow process. In a crisis, time is the enemy. If logs are stored locally on individual machines, an attacker can simply delete them to cover their tracks.
Centralised log aggregation solves this by securely forwarding all security events to a unified platform. This allows security analysts to correlate events across the five dimensions. For example, a failed login attempt on the perimeter followed by a configuration change on an internal workstation provides a clear picture of an unfolding attack.
Anomaly Detection and Alerting
Alert fatigue is a massive issue in cyber security. If a system generates thousands of low-level warnings a day, the critical alerts will be ignored. Detection mechanisms must be tuned to identify genuine anomalies, not just routine operational noise.
By establishing a baseline of normal communication patterns, anomaly detection engines can highlight deviations. If an engineering workstation that typically communicates with three specific programmable logic controllers suddenly attempts to scan the entire subnet, this is a high-fidelity alert indicative of lateral movement.
Incident Response Integration
Detection is useless without a coordinated response. When an alert fires indicating a potential compromise of a safety instrumented system, the operations team and the security team must know exactly what to do.
Visibility mechanisms must integrate directly into the incident response plan. This means defining clear escalation paths, establishing out-of-band communication channels, and practicing tabletop exercises. The goal of visibility is to compress the mean-time-to-repair, allowing operators to isolate the threat and restore normal operations swiftly.
Visibility ensures that when the first four layers of defence are tested, you are not caught off guard. Take our Cyber Security Assessment to evaluate your detection capabilities, and download the best practices guide. In our final post, we will wrap up the series and bring all five dimensions together.
Industrial Cybersecurity Best Practices
- Assessing Your Industrial Cyber Security Posture
- Boundary Defence: The First Layer of Industrial Cyber Security
- Identity and Credentials: The New Air Gap
- Halting Lateral Movement in Operational Technology
- System Hardening: Fortifying Industrial Infrastructure
- Visibility and Detection: Illuminating the Industrial Network
- A Pragmatic Blueprint for Industrial Cyber Security