Industrial Cybersecurity Best Practices
- Assessing Your Industrial Cyber Security Posture
- Boundary Defence: The First Layer of Industrial Cyber Security
- Identity and Credentials: The New Air Gap
- Halting Lateral Movement in Operational Technology
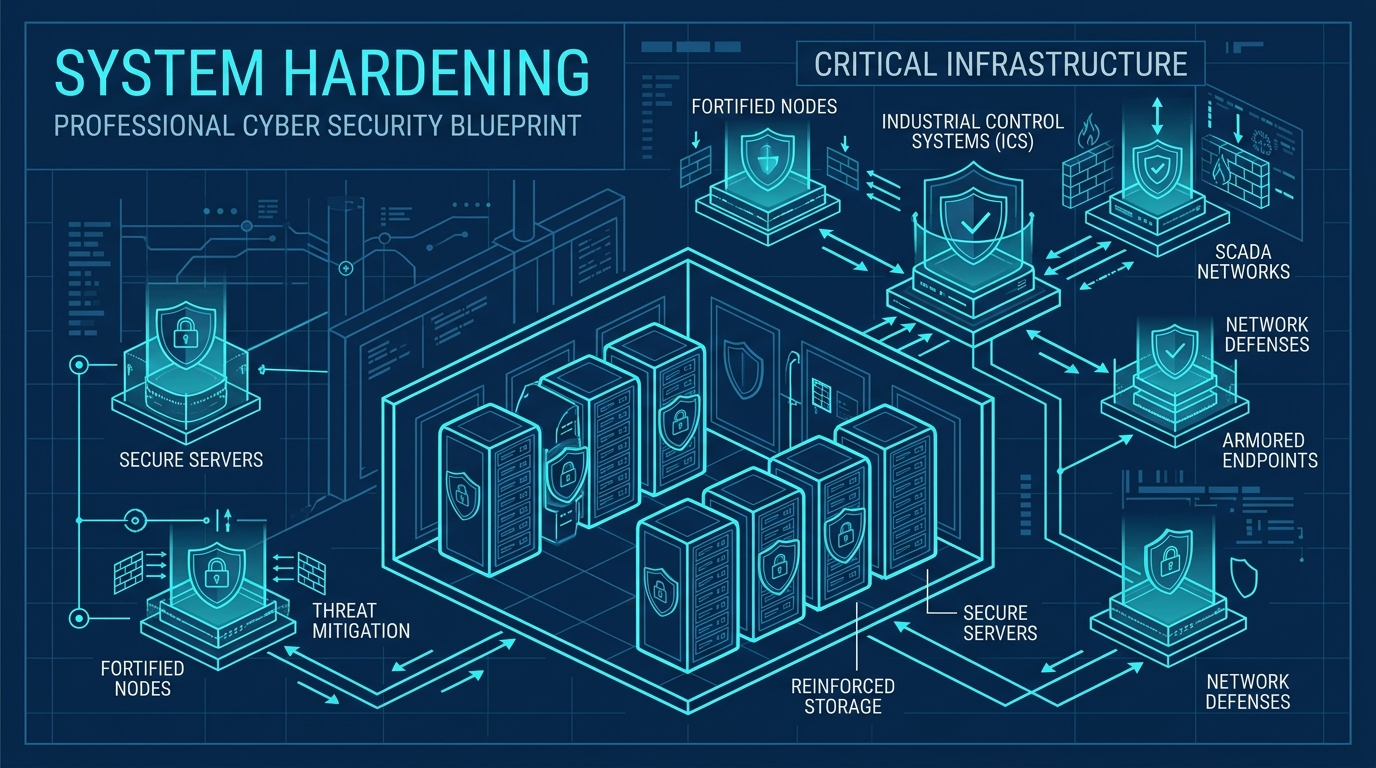
- System Hardening: Fortifying Industrial Infrastructure
- Visibility and Detection: Illuminating the Industrial Network
- A Pragmatic Blueprint for Industrial Cyber Security
Welcome to the fifth post in our series exploring the dimensions of industrial cyber security. We have built strong boundaries, secured identities, and restricted lateral movement. Now, we must look at the assets themselves. This is the fourth orthogonal dimension: System Hardening.
In operational technology, patching is notoriously difficult. Systems run constantly, maintenance windows are rare, and legacy software often relies on outdated operating systems. However, leaving systems in their default, vulnerable state is a massive risk. System hardening is the process of reducing the attack surface of individual devices, ensuring that even if an attacker reaches them, exploiting them is exceptionally difficult.
Eradicating Default Credentials
It is a harsh reality that many industrial control devices ship with hardcoded, publicly documented default passwords. Worse, these devices are often commissioned and placed into production without these credentials ever being changed. An attacker scanning the network only needs to consult a vendor manual to gain administrative access to a critical process controller.
Eradicating default credentials is a non-negotiable first step in system hardening. Every device must be configured with a unique, complex password before it is connected to the operational network. This simple act removes the lowest-hanging fruit for threat actors and forces them to use more complex, detectable methods.
Disabling Unused Services
Every running service, open port, and enabled feature is a potential vulnerability. Industrial devices often come with secondary web interfaces, file transfer protocols, and legacy management services enabled by default, even if the operator never uses them.
System hardening requires a ruthless audit of device configurations. If a service is not strictly required for the operational function of the asset, it must be disabled. By aggressively trimming the attack surface, you reduce the number of avenues an attacker can exploit, significantly increasing the resilience of the individual component.
Application Allowlisting
Traditional antivirus software relies on identifying known bad files, a strategy that is increasingly ineffective against novel malware and custom ransomware. In a static operational technology environment, where servers and human-machine interfaces run the exact same software every day, we must invert this paradigm.
Application allowlisting ensures that only explicitly approved executables are permitted to run. If an attacker manages to drop a malicious payload onto a hardened system, the operating system simply refuses to execute it. This is a highly effective control in industrial environments, locking down systems and preventing unauthorised code execution.
Secure Configuration Management
Configuration drift is a silent killer in industrial security. Over time, temporary firewall rules become permanent, test accounts are forgotten, and security settings are inadvertently downgraded during troubleshooting. Without a baseline, you cannot know if a system is hardened.
Implementing secure configuration management involves defining a strict security baseline for all asset classes and continuously monitoring against it. When a device deviates from the baseline, it must trigger an immediate alert. This ensures that the hardened posture you establish on day one is maintained throughout the lifecycle of the equipment.
Patch Management Strategy
While patching programmable logic controllers may require scheduled downtime, the Windows-based servers and engineering workstations that manage them are frequent targets and must be kept up to date. Relying on an air gap as an excuse not to patch is a recipe for disaster.
A pragmatic patch management strategy acknowledges the operational constraints while aggressively addressing critical vulnerabilities. This means triaging patches based on actual risk, testing them in a representative environment, and deploying them systematically. Where patching is impossible, compensating controls like micro-segmentation must be enforced.
System hardening ensures that your foundational assets are resilient. To see where your vulnerabilities lie, complete our Cyber Security Assessment and review our Industrial Cyber Security Best Practices guide. In our next post, we will explore the final dimension: Visibility and Detection.
Industrial Cybersecurity Best Practices
- Assessing Your Industrial Cyber Security Posture
- Boundary Defence: The First Layer of Industrial Cyber Security
- Identity and Credentials: The New Air Gap
- Halting Lateral Movement in Operational Technology
- System Hardening: Fortifying Industrial Infrastructure
- Visibility and Detection: Illuminating the Industrial Network
- A Pragmatic Blueprint for Industrial Cyber Security