Industrial Cybersecurity Best Practices
- Assessing Your Industrial Cyber Security Posture
- Boundary Defence: The First Layer of Industrial Cyber Security
- Identity and Credentials: The New Air Gap
- Halting Lateral Movement in Operational Technology
- System Hardening: Fortifying Industrial Infrastructure
- Visibility and Detection: Illuminating the Industrial Network
- A Pragmatic Blueprint for Industrial Cyber Security
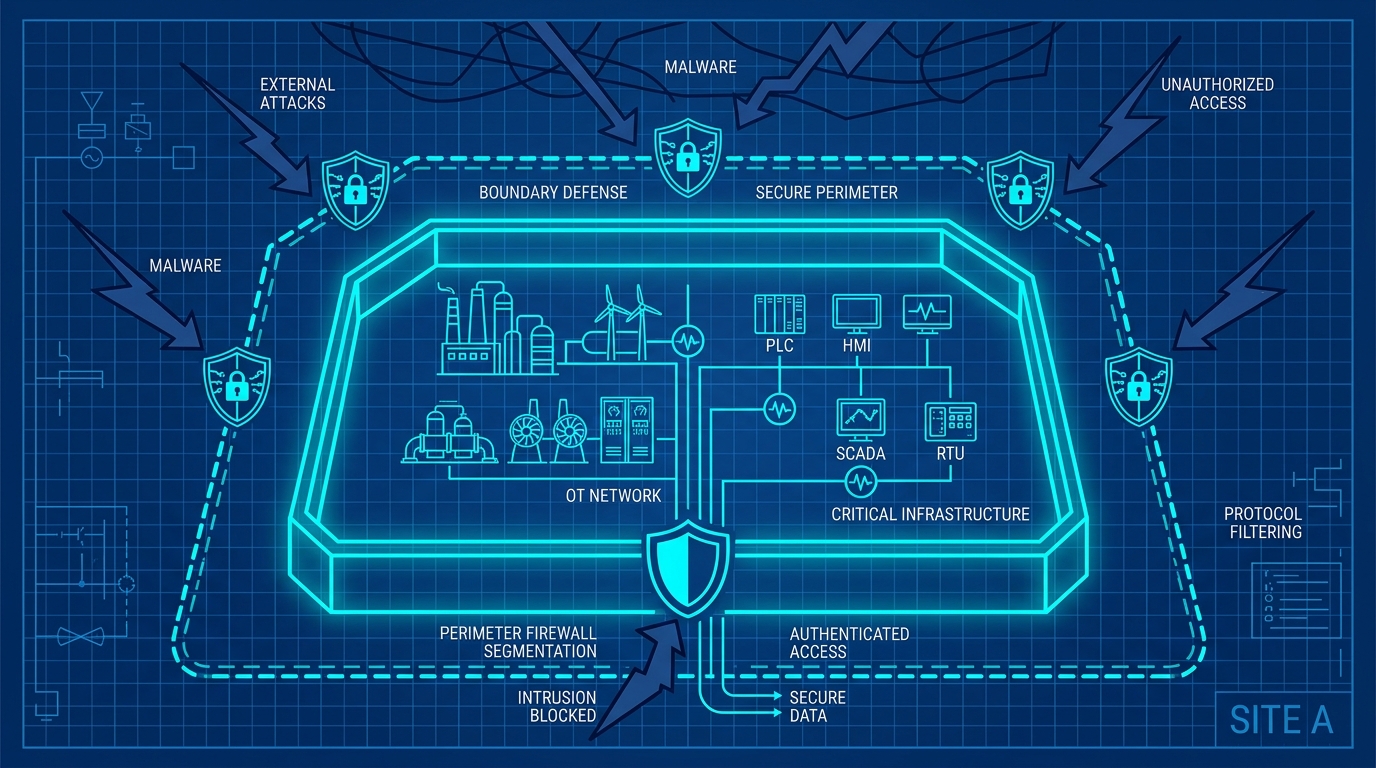
Welcome to the second post in our seven-part series on industrial cyber security best practices. In our previous post, we introduced the five orthogonal dimensions of our security scorecard, designed for mid-market companies managing hybrid Information Technology and Operational Technology environments. Today, we focus on the first of these dimensions: Boundary Defence.
Traditional perimeter security relied on the illusion of an air gap. The theory was simple: if the industrial control system is not physically connected to the outside world, it cannot be hacked. This was a comforting thought, but in modern environments, the air gap is a dangerous myth. Economic pressures and operational requirements demand remote monitoring, predictive maintenance, and vendor support. The networks are connected.
This operational shift creates technical friction. When corporate networks bleed into industrial environments, a single compromised workstation on the business side easily cascades into a physical disruption on the plant floor. We must construct hard boundaries.
Multi-Layer Boundary Enforcement
The proliferation of interconnected devices means that a flat network is an open invitation for total compromise. We must define strict physical and logical separation between the corporate network and the operational technology network. This structural separation forms the bedrock of defence in depth.
An attacker who breaches the corporate perimeter must face an entirely isolated, heavily inspected environment before they can touch a programmable logic controller or a safety instrumented system. This requires mandating firewall inspection at every boundary crossing, isolating safety systems entirely, and denying all direct routing between the internet and operational technology assets.
Elimination of Inbound Ports
Publicly exposed inbound ports are a liability. Search engines and automated scanners actively exploit them. Relying on an open listener on your perimeter firewall guarantees that adversaries will repeatedly test your defences until they find a weakness.
The architectural shift requires eliminating inbound ports completely. By forcing all external integrations to rely on polled, outbound-only connections, you render the operational technology environment invisible from the public internet. This removes the attack surface at the edge, drastically reducing the friction of constant patching and external monitoring. Close direct inbound access for legacy remote desktop tools and replace them with outbound-only reverse tunnels.
Modern Remote Access Architecture
Granting full network routing via legacy virtual private networks is equivalent to handing a contractor the master keys to the building just so they can fix a single sink. Traditional jump boxes and shared remote access tools fail to provide the granular control required in modern industrial environments.
Access must be brokered through an identity-aware proxy that limits the user strictly to the application they need. Terminating the session at the application layer breaks the direct routing path. This means an infected remote machine cannot spread malware laterally into the operational technology network. Deprecate legacy virtual private network appliances and require continuous authorisation for every remote session.
Alternate Perimeter Control
Vendors frequently install rogue cellular modems or undocumented wireless access points to bypass strict corporate firewalls, prioritising maintenance convenience over security. These alternate perimeters act as hidden backdoors, entirely subverting the primary boundary defences you have meticulously designed.
Identifying and eliminating these undocumented connections is critical. By enforcing strict network access control and physically auditing the environment, you ensure that all traffic is forced through designated, heavily inspected chokepoints. Conduct physical audits and block unauthorised vendor backdoors installed during commissioning.
Outbound Traffic Restriction
A compromised internal device must communicate with an external command and control server to receive instructions or exfiltrate data. If outbound traffic from the operational technology network is permitted by default, attackers face zero resistance once inside.
Implementing a strict default-deny posture for outbound traffic turns this vulnerability into a containment trap. By explicitly defining which internal devices are allowed to communicate externally and filtering that traffic through deep inspection, you ensure that malicious beacons fail to connect, buying time for the security team to respond.
Boundary defence is not about building an impenetrable wall; it is about creating structural friction that isolates critical assets. It is the first layer of our orthogonal defence strategy. We encourage you to evaluate your own boundary defences by taking our Cyber Security Assessment and downloading the Industrial Cyber Security Best Practices guide. In our next post, we will explore the second dimension: Identity and Credentials.
Industrial Cybersecurity Best Practices
- Assessing Your Industrial Cyber Security Posture
- Boundary Defence: The First Layer of Industrial Cyber Security
- Identity and Credentials: The New Air Gap
- Halting Lateral Movement in Operational Technology
- System Hardening: Fortifying Industrial Infrastructure
- Visibility and Detection: Illuminating the Industrial Network
- A Pragmatic Blueprint for Industrial Cyber Security