Industrial Cybersecurity Best Practices
- Assessing Your Industrial Cyber Security Posture
- Boundary Defence: The First Layer of Industrial Cyber Security
- Identity and Credentials: The New Air Gap
- Halting Lateral Movement in Operational Technology
- System Hardening: Fortifying Industrial Infrastructure
- Visibility and Detection: Illuminating the Industrial Network
- A Pragmatic Blueprint for Industrial Cyber Security
The convergence of business networks and industrial control systems creates unprecedented hybrid environments. For years, the prevailing wisdom was to rely on the illusion of an air gap. Today, that air gap is a myth. Mid-market companies operating both Information Technology and Operational Technology find themselves at a crossroads. The economic push for efficiency, remote diagnostics, and integrated supply chains means these systems are connected. This operational shift brings immense technical friction, as the traditional tools used to secure corporate laptops fail spectacularly when applied to programmable logic controllers and safety instrumented systems.
We need a pragmatic approach. You cannot simply install a corporate firewall on a plant floor and declare the environment secure. Security in the industrial space is not a static checklist; it is an architectural reality. To guide this, we have developed a comprehensive cyber security assessment, a scorecard, and a set of best practices explicitly designed for hybrid environments.
Our framework is grounded in reality, drawing heavily on the findings from the CISA’s Risk and Vulnerability Assessments. In their FY23 analysis, the agency highlighted systemic weaknesses across critical infrastructure, from poor boundary protections to easily compromised credentials. The data is clear: adversaries are not using advanced, theoretical exploits. They are walking through open doors.
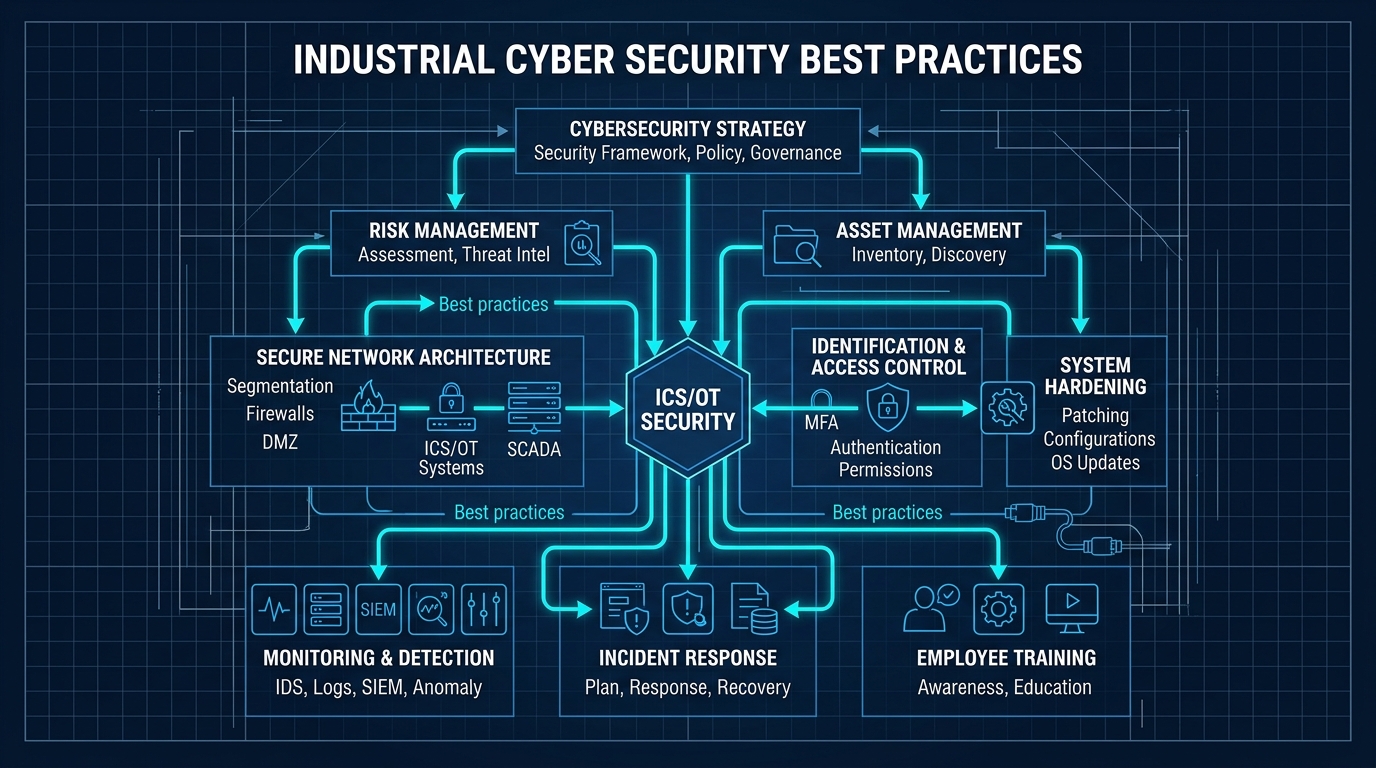
To address this, our program distils industrial cyber security down into five orthogonal dimensions. These are distinct vectors to invest in, measure against, and improve upon. They provide a pragmatic roadmap for what to work on first. The dimensions are:
- Boundary Defence
- Identity and Credentials
- Lateral Movement
- System Hardening
- Visibility and Detection
The crucial aspect of these five dimensions is that they are orthogonal. This means they control different risks using entirely different mechanisms. To understand why this matters, consider the Swiss cheese model of defence in depth. Every defensive layer has inherent flaws—the holes in the cheese. If you stack multiple slices of the same type of cheese, the holes align, and the threat passes straight through. If you stack different layers—orthogonal defences—a failure in one layer does not mean a systemic breach.
We have discussed this concept previously in the context of multi-factor authentication. When you combine something you know (a password), something you have (a hardware token), and something you are (a biometric), you are combining uncorrelated risks. The criminal gang that bought a database of stolen passwords from a forum has no overlap with the burglar who stole your physical keys. The risks are independent.
Our five dimensions work the exact same way. An adversary who manages to bypass a network boundary (Boundary Defence) does not automatically possess the authentication token required to issue a command (Identity and Credentials). If they steal a credential, they are still constrained by network micro-segmentation that prevents them from reaching the critical asset (Lateral Movement). An escape of one layer is not an escape of another.
Over the next six posts in this series, we will examine each of these dimensions in depth. We will explain the cause and effect of vulnerabilities in each area, and provide actionable, pragmatic steps to reduce your risk. We will cut through the marketing fluff and focus on the structural realities of securing operational technology.
In the meantime, you do not have to wait to understand your current posture. We encourage you to take our Cyber Security Assessment. It will benchmark your environment against these five dimensions and the CISA guidelines. Once completed, download our companion Industrial Cyber Security Best Practices guide to map out your next steps. The threats are real, but the defences are within your control. Take the assessment today and start building a resilient architecture.
Industrial Cybersecurity Best Practices
- Assessing Your Industrial Cyber Security Posture
- Boundary Defence: The First Layer of Industrial Cyber Security
- Identity and Credentials: The New Air Gap
- Halting Lateral Movement in Operational Technology
- System Hardening: Fortifying Industrial Infrastructure
- Visibility and Detection: Illuminating the Industrial Network
- A Pragmatic Blueprint for Industrial Cyber Security