Zero Trust
Overview
Zero-Trust security. Switch from a perimeter-based (firewall and VPN) model of access to a user to resource model.
Implement strong, simple identity. Identity for both a person, but also a system. Decouple the identity from the corporation: make it affinitive to the user, a single identity.
Enforce entitlements and authorisation in the network.
This micro-segmentation is simpler to use, more accessible, and, more secure. It reduces the lateral-traversal, it empowers the users, it increases the audit capability. And, its more economical, more scalable. Everybody wins.
Articles
-
Securing Canada’s Critical Energy Infrastructure: Navigating New Cybersecurity Regulations with Zero-Trust Architecture
For Canadian energy and utility operators, complying with stringent new cybersecurity mandates like the Canadian Standards Association Z246.1:21, Alberta Regulation 84/2024, and British Columbia Utilities Commission guidelines is no longer optional. Discover how Agilicus AnyX enables operators to seamlessly implement multi-factor authentication, strict network segmentation, and zero-trust remote access for legacy industrial control systems—without ripping and replacing existing infrastructure or relying on vulnerable virtual private networks.
-

The Fragility of Interdependence: Securing the Industrial Mesh
The £1.9bn JLR breach exposed supply chain fragility. Download the Agilicus whitepaper to learn how Zero Trust secures the industrial mesh against cyber threats.
-

Digital Disenfranchisement: Stop Treating Your Frontline Like Second-Class Citizens
Are your bus drivers and contractors stuck using paper because IT can’t secure their devices? It’s time to stop the ‘Digital Disenfranchisement’ and use Zero Trust to safely connect everyone, everywhere.
-
The 4-Day Warning: New SEC Cyber Rules Hit the Factory Floor
Consequently, trying to scope an attack in a sprawling operatioanl tech network is like trying to find a needle in a haystack, except the haystack is currently on fire, and you are not allowed to use water because it might short-circuit the only machine that is still running.
-

Cleaning Up the Mess: How One Disgruntled Contractor Trashed a Network (And How to Stop It)
An ex-contractor’s revenge cost a firm $862K. This cybersecurity story reveals a critical flaw in vendor access and how to prevent it.
-
Ditch the Digital Ostrich: How Zero Trust is Saving Municipalities (and Their Wallets) from Cyber Chaos
Facing rising cyber insurance costs? For municipalities, risky VPNs are a major hurdle. Learn how Zero Trust secures systems and lowers insurance risk.
-

Your Air Gap is a Lie, and Other Inconvenient Truths About Industry 4.0
For years, the security model for water systems has been the air gap—a mythical wall where everything inside is trusted and everything outside is not. The problem? That air gap already has a bunch of holes in it, and Industry 4.0 is making more.
-
You Have a Login, But You Shall Not Pass: The Magic of Fine-Grained Authorisation
Authentication gets you in the door, but fine-grained authorisation decides which rooms you can enter. This principle ensures users access only the specific resources they need, making your systems more secure by rendering everything else invisible to them.
-

AI-Powered Cyber Threats: Protecting Your Critical Infrastructure
AI amplifies cyber risks for critical infrastructure, making attackers more effective. CISA’s FY23 report shows 80% of successful attacks exploit identity weaknesses like valid accounts and spearphishing. AI isn’t creating new vulnerabilities, but leveraging existing ones. Implementing Zero Trust and universal Single Sign-On significantly reduces these risks, making organizations a harder target.
-
CityWorks CVE Breaches IIS
CityWorks breach leads to lateral traversal through IIS and onwards into your network. Protect it with Agilicus AnyX while you work on upgrading.
-

Krooked Kriminals Krack Krispy Kreme
Krispy Kreme materially impacted by cyber security issue, files SEC-8K disclosure.
-

CityNews The Mike Farwell Show Interview
This morning I was interviewed on the Mike Farwell Show (CityNews). You can check the interview here @ 54:50.
-

SolarWinds Gives Federal Agencies Labour Day Present
SolarWinds Web Help Desk CVE-2024-28986 (rated 9.8 our of 10) is now included in CISA’s Known Exploited Vulnerabilities (KEV) Catalog, indicating its active use in cyber attacks, giving affected agencies until September 5, 2024 to fix the flaw under Binding Operational Directive 22-01. How fun.
-
10 Billion Reasons Shared Passwords Are Bad: RockYou2024
Shared password bad. 10 billion passwords leaked. Your team installed some shadow IT remote access solution with a shared password.
-
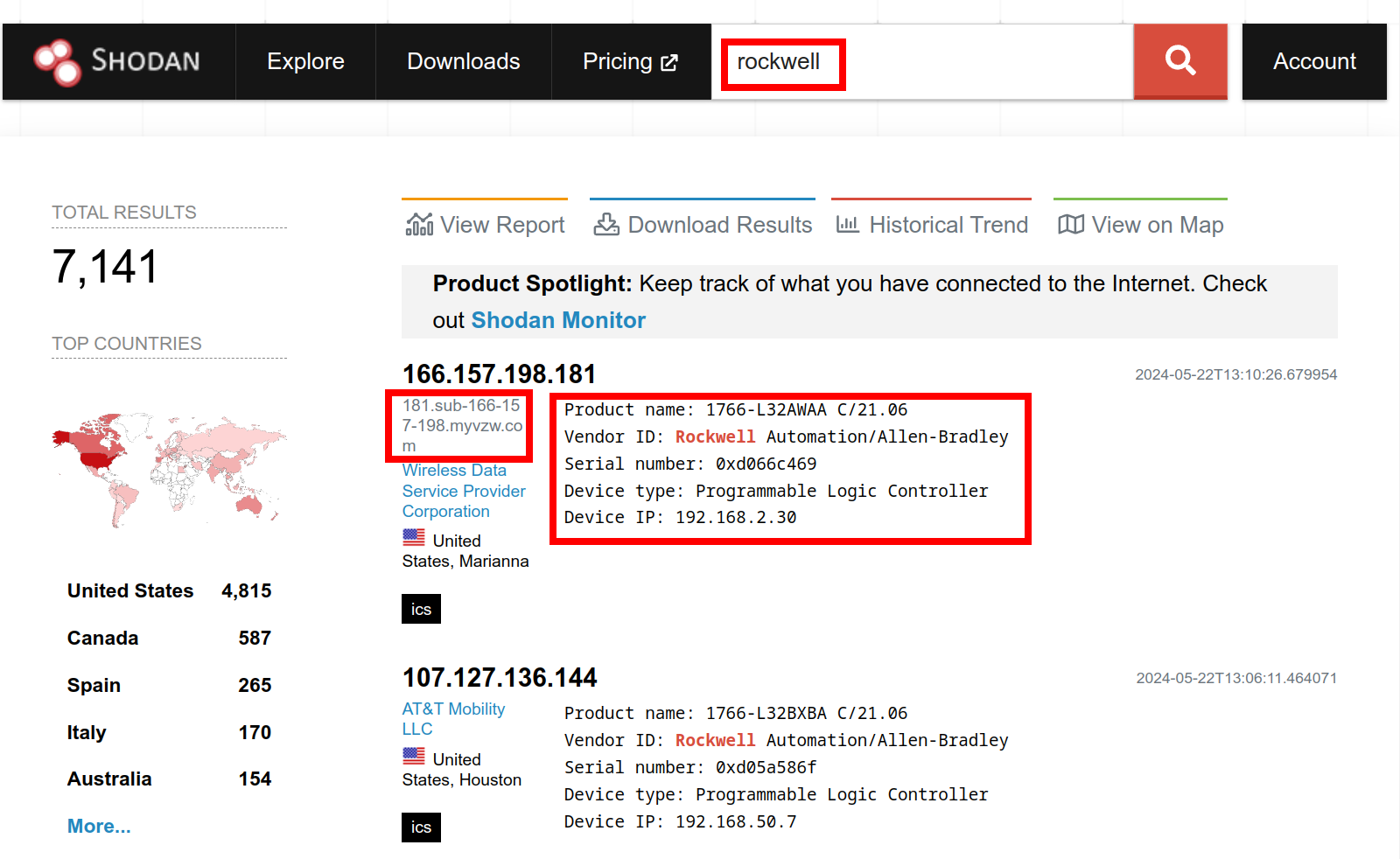
Get Thee From BGP Rockwell: Ethernet/IP Is not Internet
You wouldn’t download a PLC, would you? Rockwell Automation alert on public access to PLC, and a Shodan search to fact check it.
-

Begone Ivanti Industrial VPN Sayeth CISA
ED 24-01 directs agencies to instantly remove Ivanti Industrial VPN from industrial operations. Defence In Depth, Zero Trust give you more time to react.
-

Using Zero Trust to Enable Secure Remote Access to SCADA for Water Systems
This blog post explores the challenges of securing remote access to SCADA systems and how Zero Trust can act as a solution.
-
Zero Trust vs. VPN: A Comprehensive Comparison for Secure Remote Access
In this blog post, we’ll dive into the Zero Trust vs. VPN security model differences and why the former is ultimately the far superior choice for secure, seamless remote access.
-
SSH for Remote Access: Every User, Every Device, Every Application
In this blog post, we’ll delve into the challenges of enabling SSH for remote access and how you can do so without compromising security through Zero Trust.
-
Simplifying Secure Access: Enabling Rockwell Automation Remote PLC Access Without a VPN
In this post, we’ll explore the limitations of VPNs and delve into how to enable Rockwell Automation remote PLC access.
-
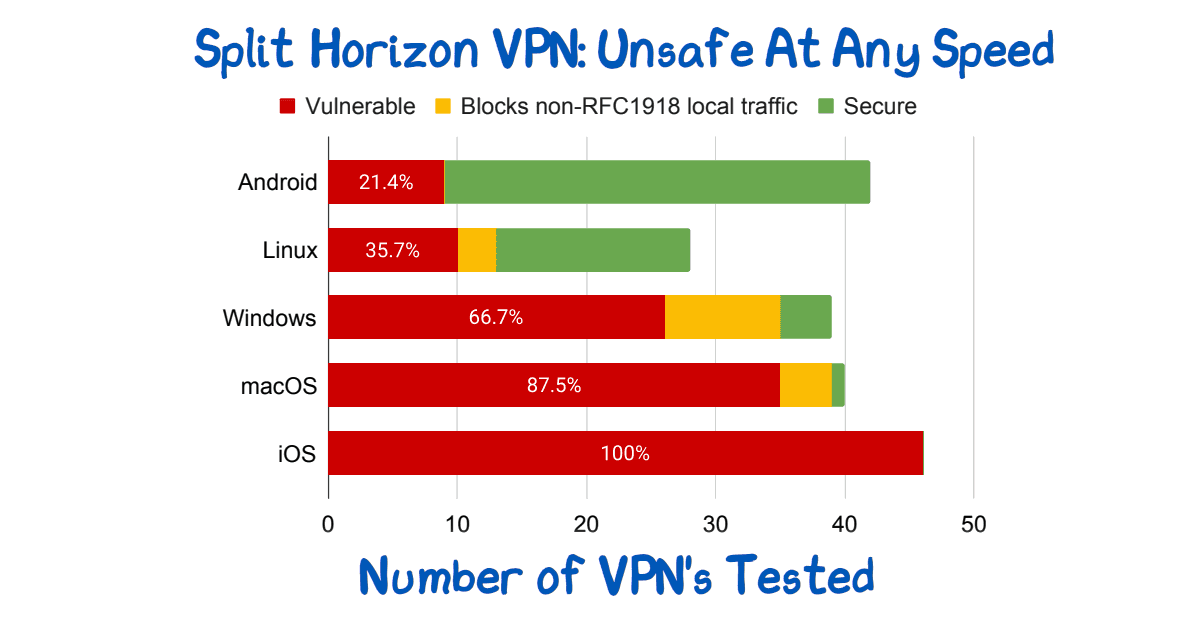
Split Horizon VPN: Unsafe At Any Speed
Split Horizon VPN’s are used to avoid breaking video conferencing. They are unsafe. See paper for route injection issues.
-

NIST sp 800-63A: Introduce Yourself
Who are you? Identity involves knowing who you are, and then later proving it. NIST sp 800-63A enrollment is the first step, let’s talk about that!
-
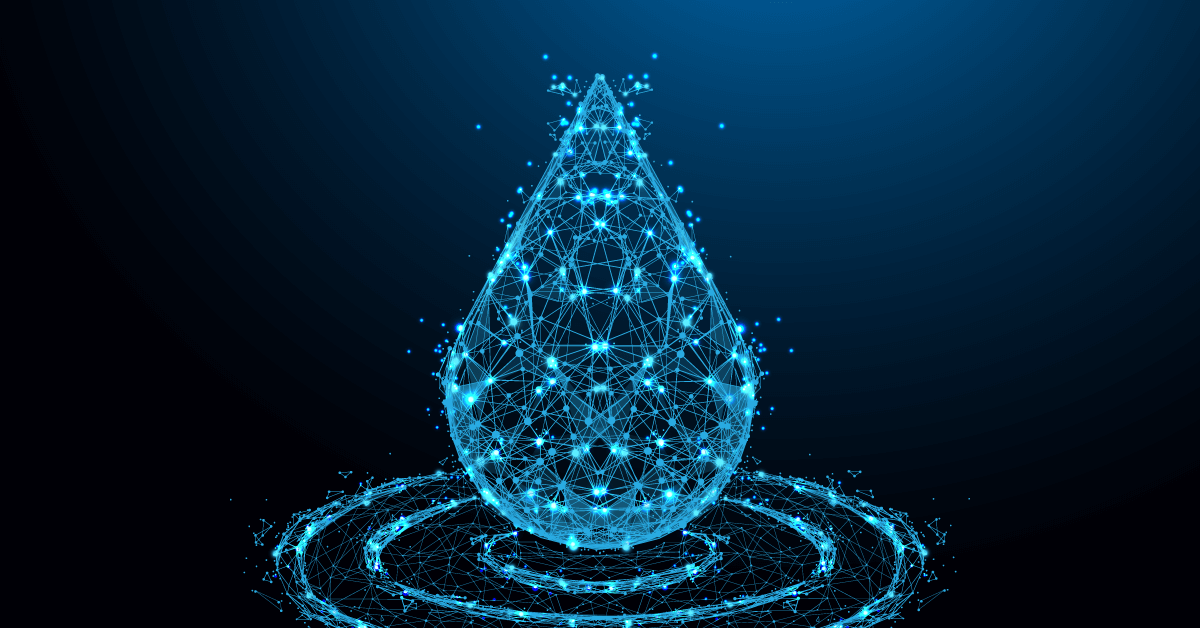
The Security Risks of Using VPNs in Water and Wastewater Facilities
What are the risks of using VPNs in water and wastewater facilities? We’ll help you answer that question and understand what to do instead.
-
The Security Risks of Using Shared Credentials in Water and Wastewater Facilities
There are many security risks of using shared credentials in water and wastewater facilities. Here’s why you should eliminate them and how to do it.
-
Zero Trust Troika: The Who, The What, The How
Perimeter security approaches are no longer effective. A Zero Trust Network Architecture is a powerful, modern way to protect your network from cyber attacks.
-
Strengthen Your Industrial Network Cybersecurity with Vendor Access Management
Securing your third-party vendors can help reduce the cyber risk to your control systems and improve overall industrial network cybersecurity.
-
Understanding the CISA Zero Trust Maturity Model: A Framework to Improve Your Security Posture
This article will give you an overview of the CISA Zero Trust Maturity Model, the changes made in Version 2.0, and how it can benefit your organization.
-

The Zero Trust Roadmap: Understanding NIST 800-207 and How to Align With It
This article will give you an overview of NIST 800-207 and the different ways your organization can implement Zero Trust to meet the guidelines.
-
Best Practices In Vendor Privileged Access Management
Vendor privileged access management best practices: Access control, strong, unified authentication, fine-audit, secure access.
-

Identity Provider Versus Single-Sign-On
Single-Sign-On and Identity Providers are often treated as the same. But, the IdP facilitates the SSO. You can have multiple IdP if desired.