Synology Connector Install
Synology NAS. Agilicus Connector.
Overview
The Agilicus Connector can install on an embedded NAS product such as Synology. The devices (usually) have either an Intel or an Arm processor. The instructions are the same for each, but the link is different. The instructions below are for a Synology NAS but will be similar on other devices.
NOTE: Upgrades
Note: it is possible that when you upgrade the OS to your Synology you may need to re-install your Agilicus Connector.
No changes are needed to your firewall. No VPN is needed. You can administer users via their Active Directory or Apple, Google, Linkedin accounts.
The high level steps are:
- Enable SSH on your NAS
- Create a Connector (Agilicus admin interface)
- SSH to the NAS
- Run the given command
after this, the Agilicus Connector will be entirely automatic, and controlled via the Agilicus admin interface.
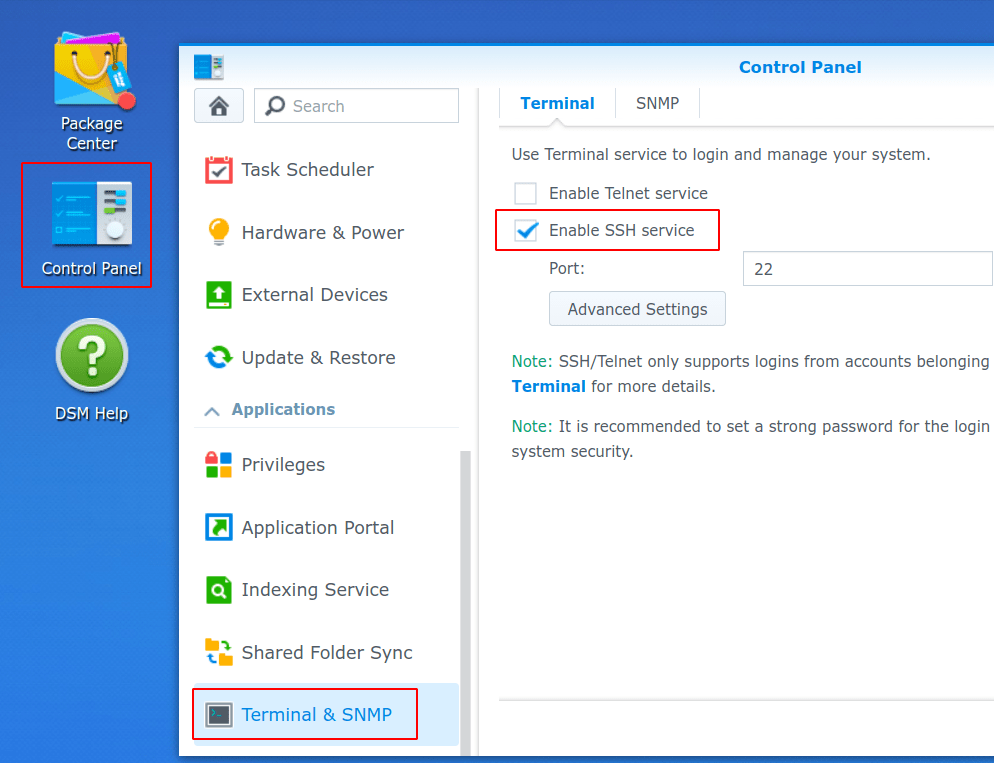
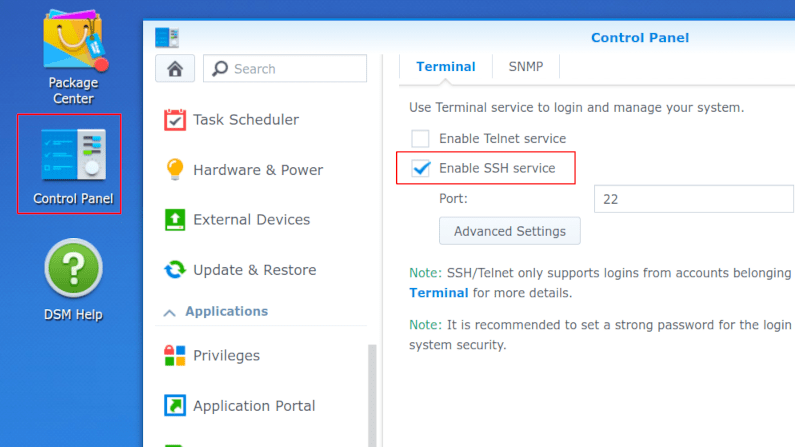
1. Enable SSH
In order to install the Agilicus Connector on your Synology NAS, you will first need to enable SSH. We can do this from the Synology Web Interface Control Panel, select “Terminal & SNMP” under Applications.
If you are not familiar with SSH, it is a Secure Shell remote command line interface. We will only use it for the installation step here, after which we don’t need it. You may use ssh from the command line on your Windows, Mac, Linux machine (it is typically installed on all of these). You may also use Putty, or, you may install SSH into Chrome and use from your browser.
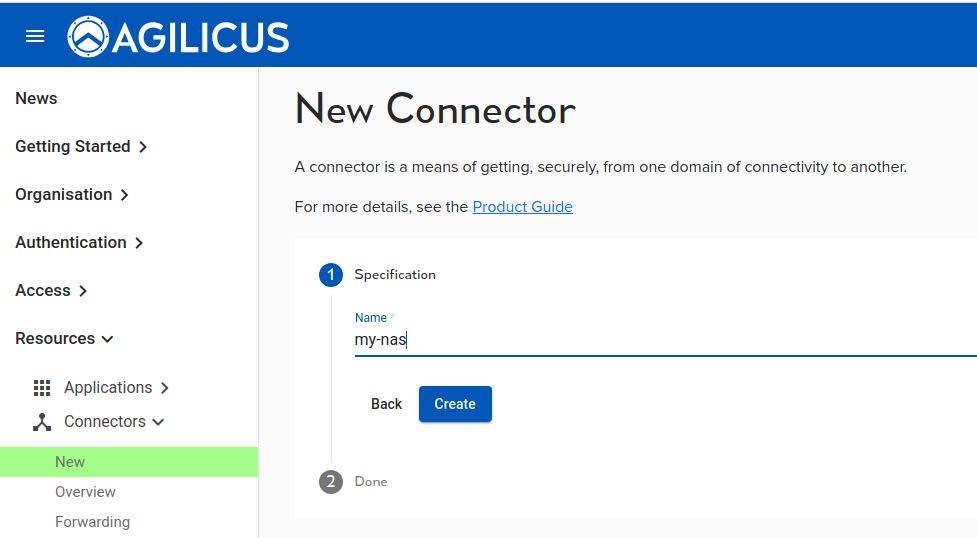
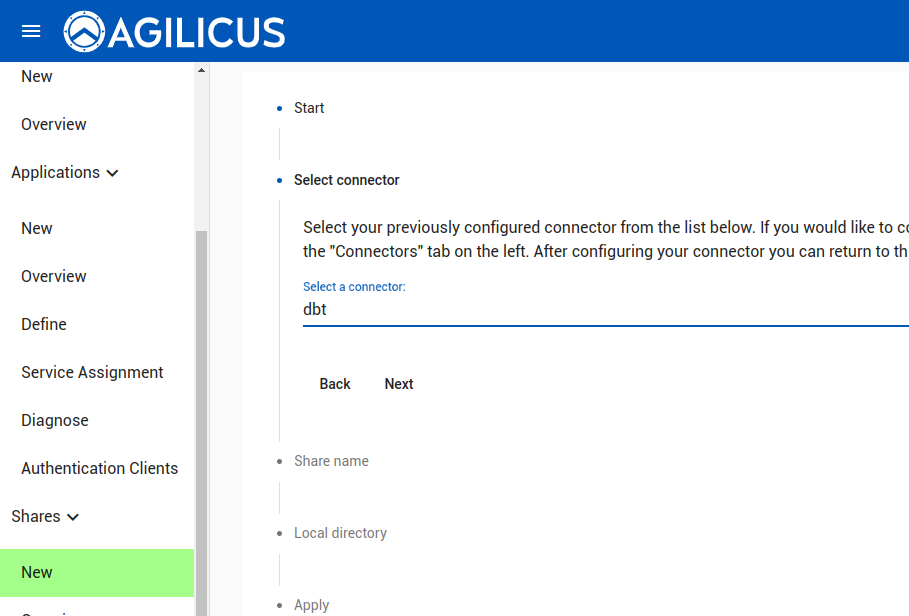
2. Create Agilicus Connector
First we will create a Connector. This logical endpoint allows reverse inbound connectors to safely occur.
We give the connector a name. This is used for statistics and diagnostics purposes.
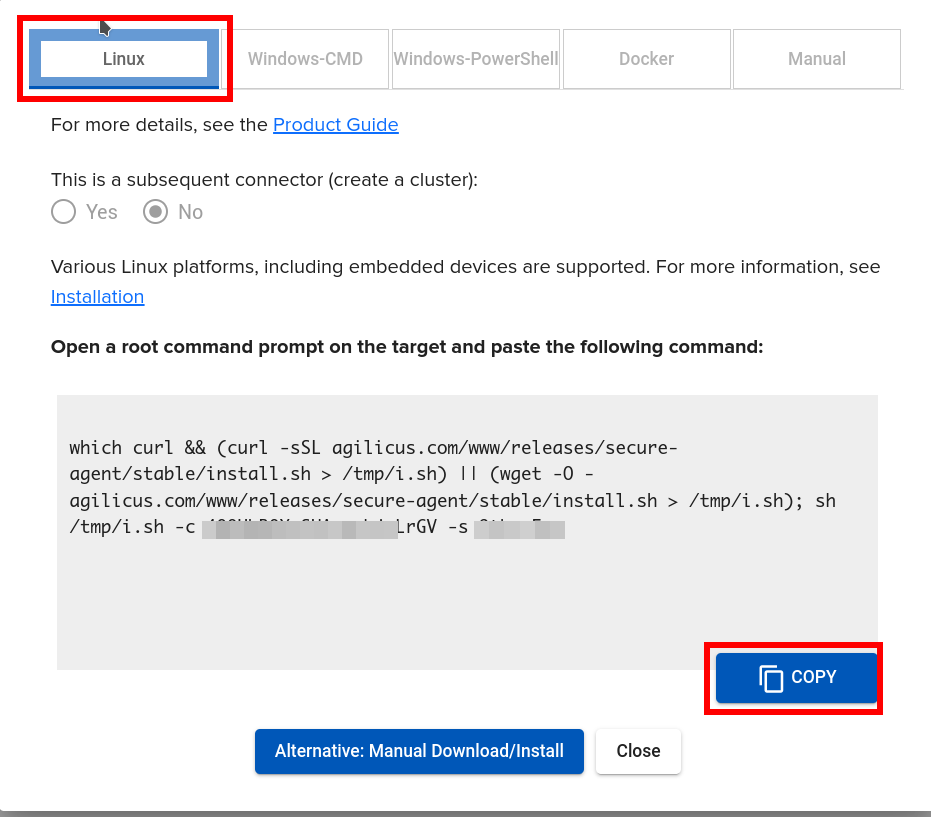
You will now be presented with some download instructions. Copy the command line given for Linux.
3. SSH to the NAS
SSH to your NAS. Run ‘sudo -i’. Now paste the command line
...
INFO[2024-01-07T17:14:35-05:00] Starting connector - version v0.237.1
INFO[2024-01-07T17:15:00-05:00] Check if the agilicus connector is already running as a service. If so stop it
...
INFO[2024-01-07T17:15:09-05:00] creating connector instance
INFO[2024-01-07T17:15:10-05:00] Join a connector cluster
INFO[2024-01-07T17:15:10-05:00] Start agilicus-agent service
INFO[2024-01-07T17:15:18-05:00]
INFO[2024-01-07T17:15:18-05:00] Installation Complete
At this stage we are complete. Let us look at some sample first resources.
Sample: Synology Web Interface
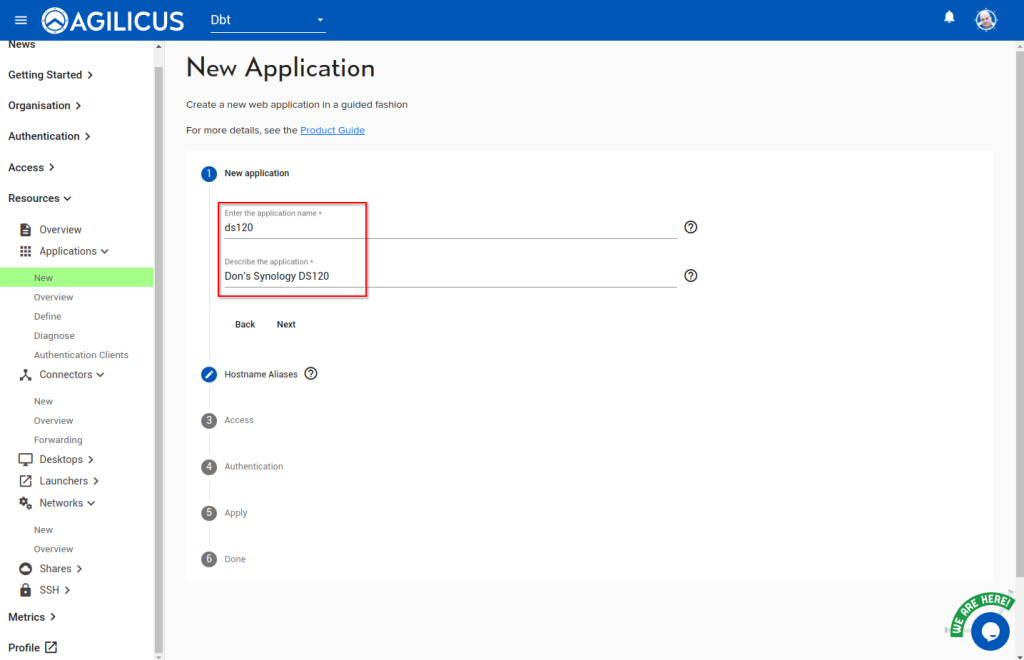
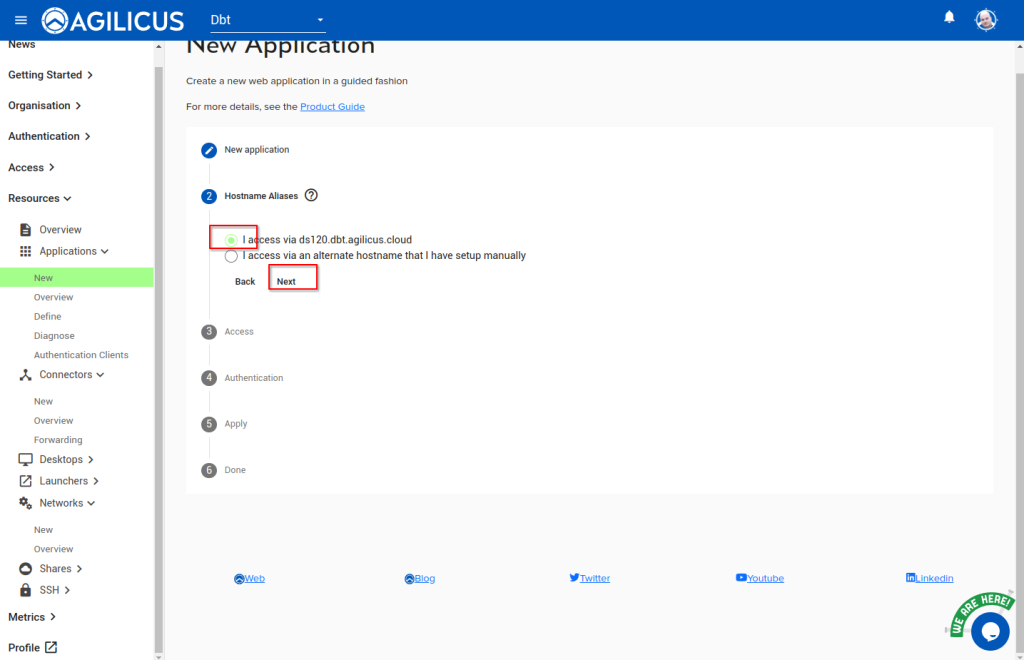
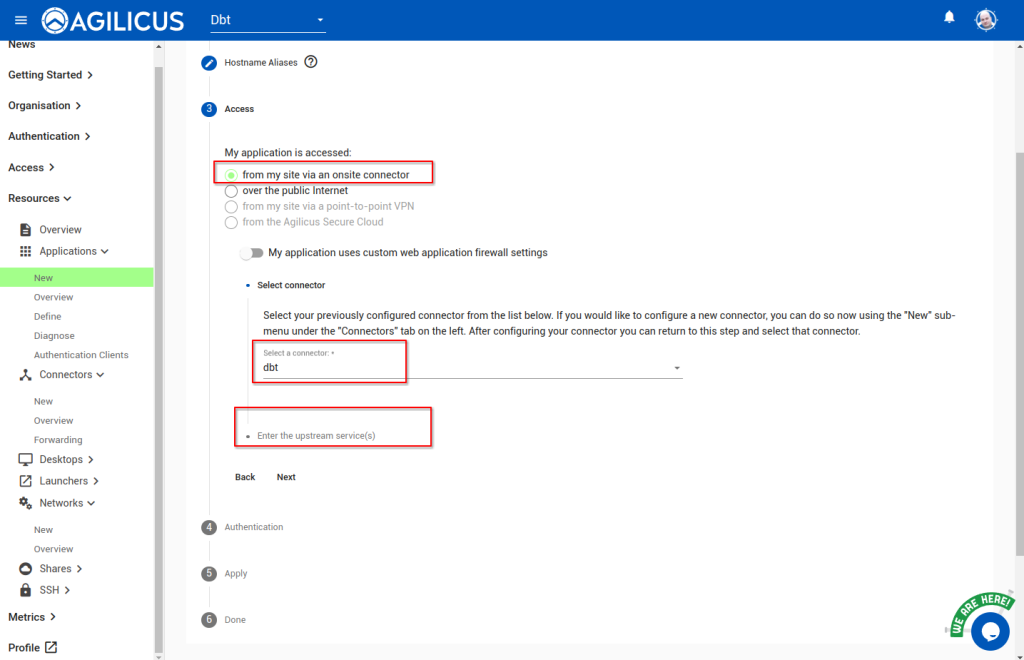
As a first example, let us make the Synology Web interface available via Agilicus. The detailed screen shots are below, but the steps are:
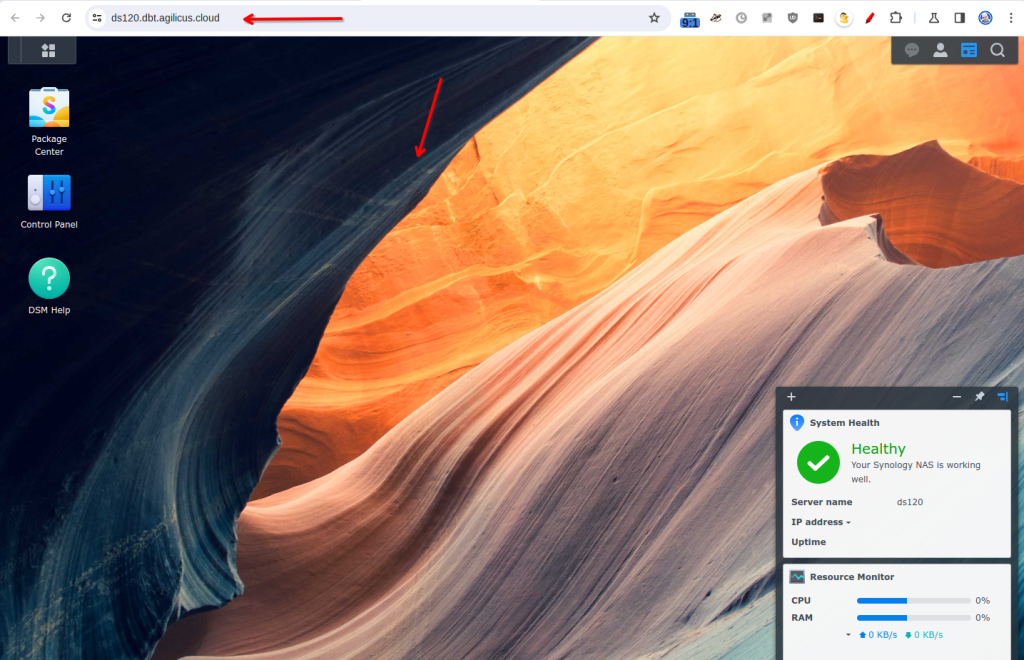
- Resources/Application New. Select a name (this will become an internet host name, so it cannot have spaces or special characters)
- Select which connector (the one we just installed) is on the same site as the Synology
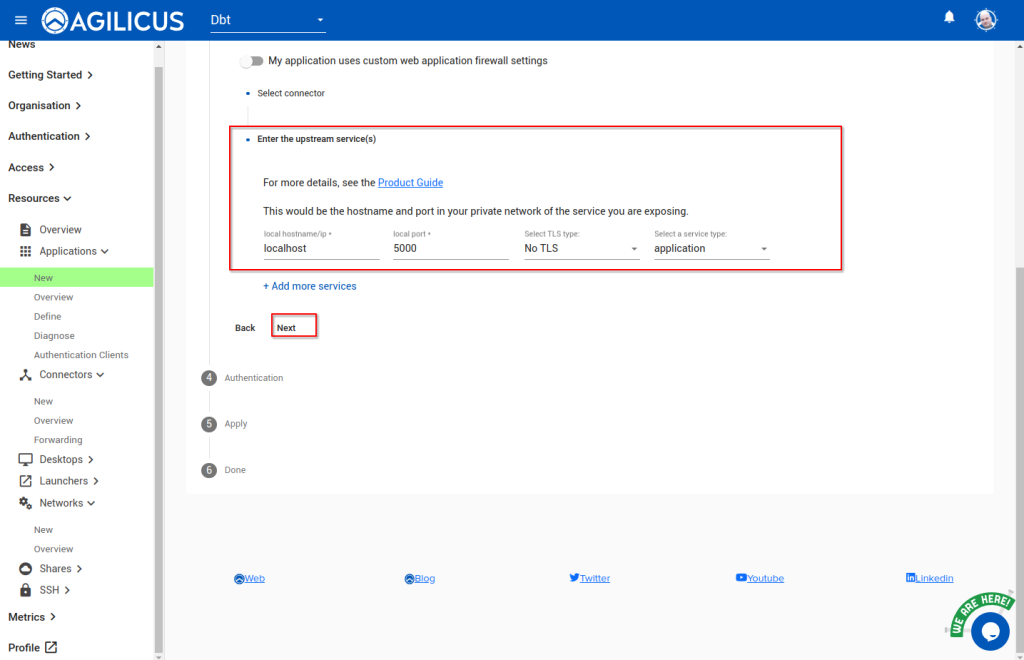
- Select the network coordinates of the Synology web interface. Since we are running inside the NAS, we can use ‘localhost’ and 5000 for a port (these are the internal coordinates of the web interface)
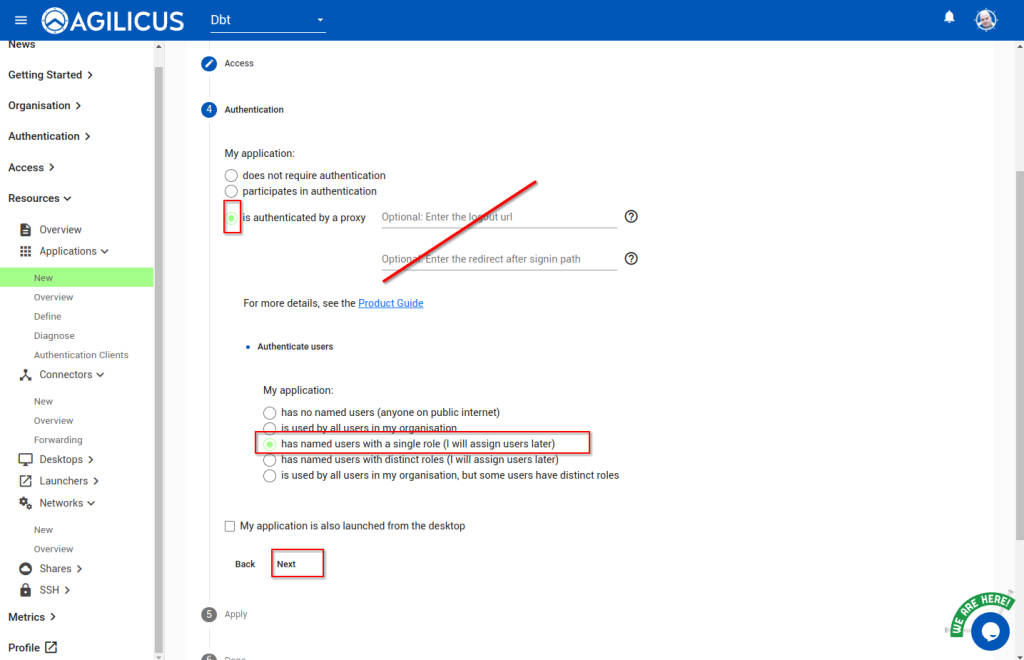
- Select authenticated by Proxy. This means a user will be forced to provide credentials in order to see the web interface
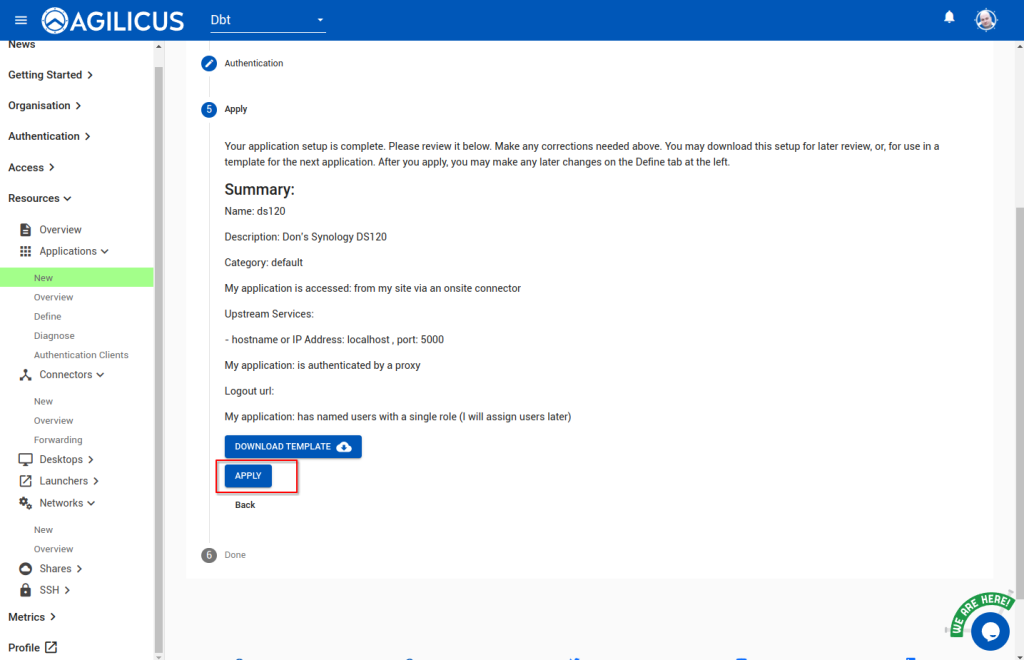
- Select ‘named users, single role’, we will assign permissions in the next step. Hit apply, this will create the application.
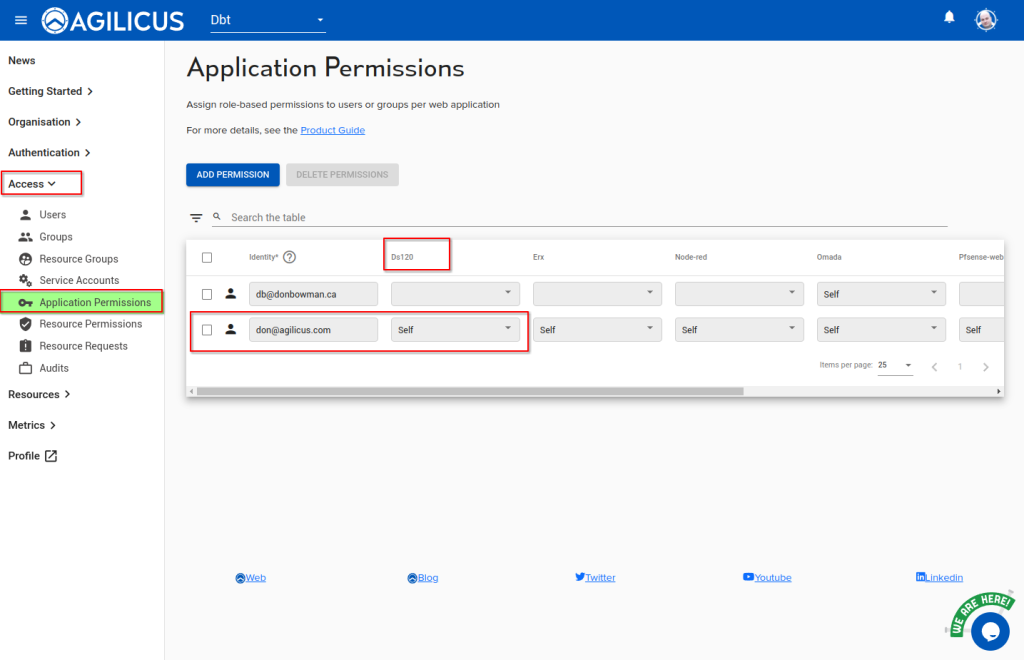
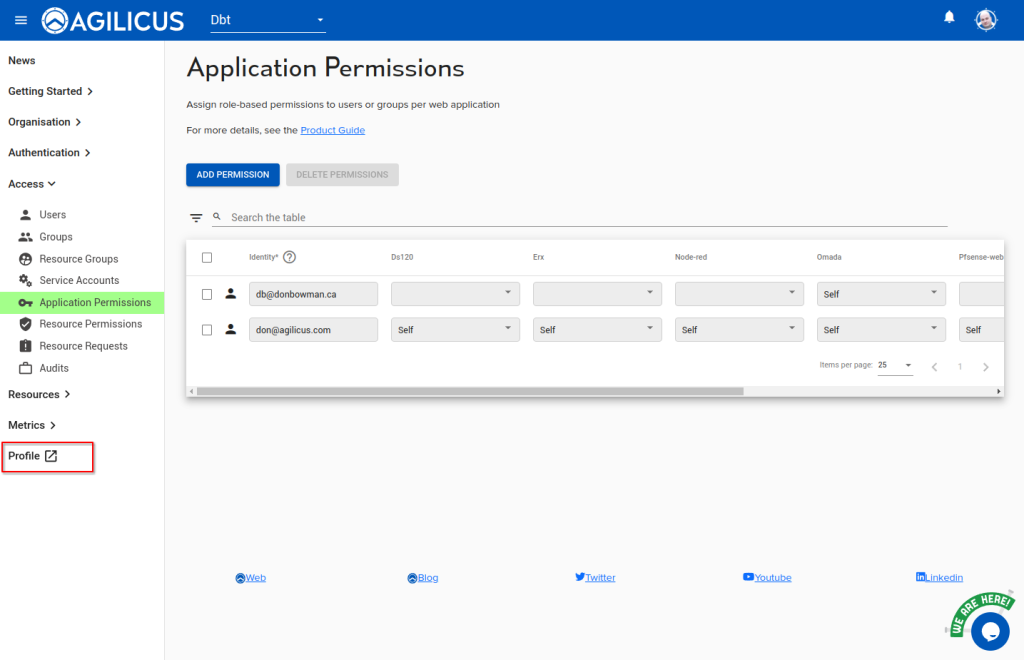
- Assign permissions. Access/Application Permissions. We can assign permissions to groups or individual users. Select the row for the user/group, and the column for the application.
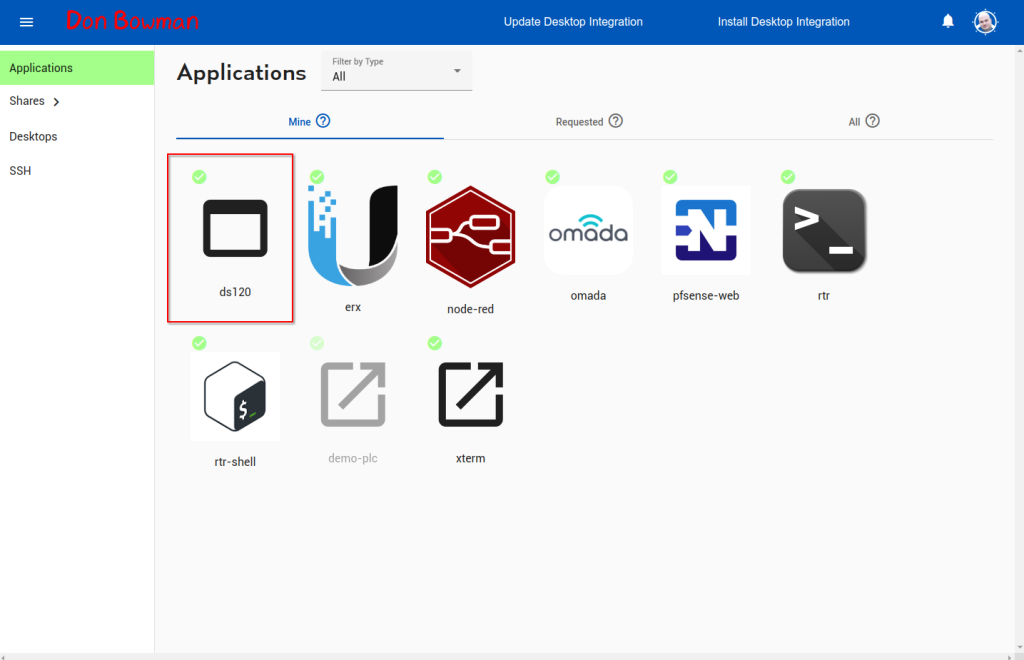
- We are done. Let’s test. We can use ‘profile’ (https://profile.YOURDOMAIN), or, directly, https://APPNAME.YOURDOMAIN. let’s use the link to profile in the lower left, note (and bookmark) the URL it goes to.
- You should see an icon for your new Synology NAS web interface. If not, refresh the page. If you select it, it will navigate to a new web page, note the URL.
Sample: Synology Share
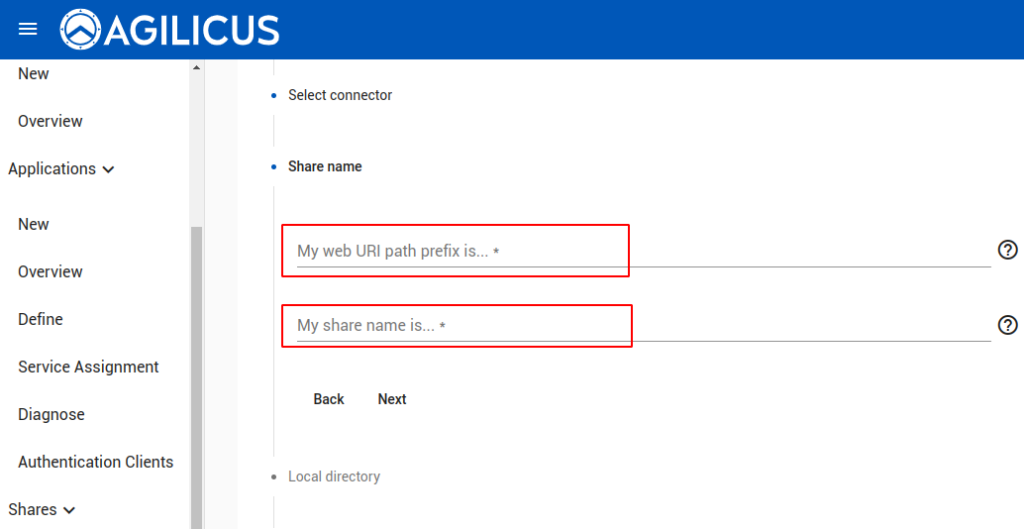
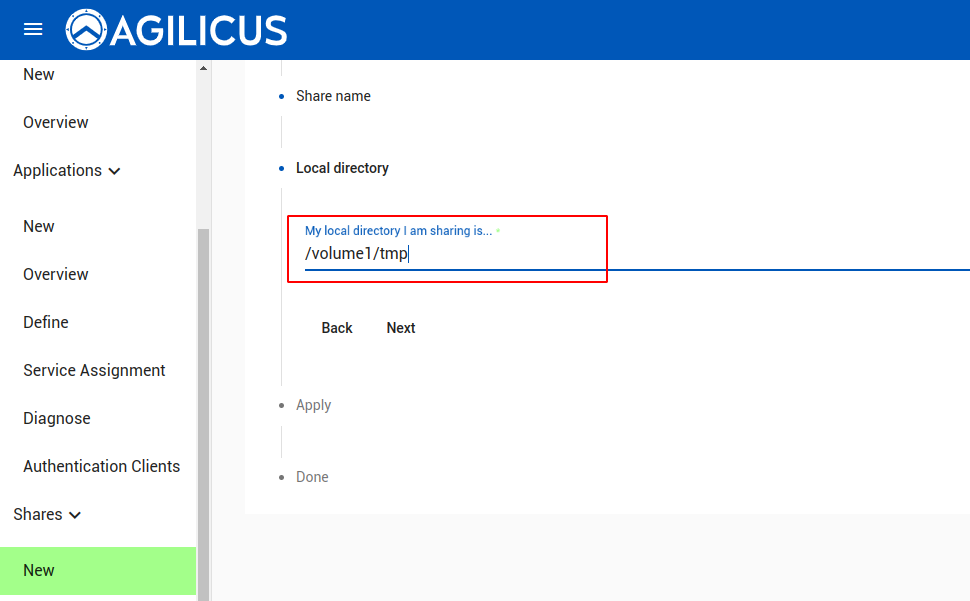
Let’s assume we have a Share existing on our Synology called ‘tmp’. On the filesystem this is in /volume1/tmp. Once we have completed the above steps, we can create a new Share in the Agilicus admin interface (https://admin.YOURDOMAIN).
Next we will be asked for two parameters (web uri path prefix, name). The first will appear in an http path, e.g. if you say “bobcat”, the URI your users will see is https://files.YOURDOMAIN/bobcat. The second is a name which will show up in the audit log. Normally these are the same (unless you have the same share name on multiple hosts).
Now we will indicate the path on the Synology. In our example (The synology has a share called tmp, this will be in /volume1/tmp)
At this stage you will be given the option to test this in the administrative interface, and, your users may navigate to https://profile.MYDOMAIN to get their own mount instructions for their desktops.
Sample: Synology Surveillance Station Remote Cameras
See Synology Surveillance Station for detailed setup, the above web interface setup will give you access to your cameras, the remainder of the setup is on the NAS interface.
Uninstall
agilicus-agent client --uninstall