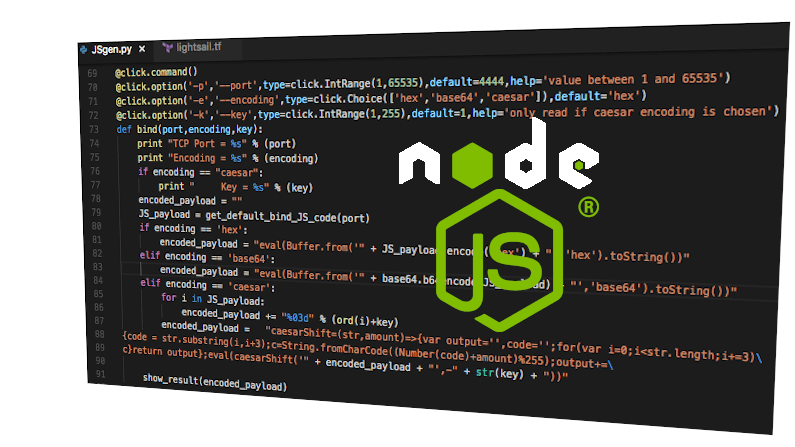
A popular nodejs library (ua-parser-js) was recently subverted to introduce some malicious code. The (legitimate) package author posted a note to Github, but, the tl;dr: is that a developer had permission to publish, had no multi-factor authentication, and got spearphished.
And, on reading that, you are probably thinking one of a few things:
- This doesn’t apply to me, I’m not a programmer, I don’t even know what a nodejs is
- Seems like they should have used multi-factor authentication
- Seems like a browser issue
- $!@#$ open-source, insecure i tells ya!
- Oh no, not again
Well, on #1, you are wrong. I guarantee you are using something in nodejs, as an end user if not as a developer. In fact, you have used it in the last couple of minutes. It is everywhere. JavaScript is what makes the web go round, and this is a popular package.
And, on #2, yes, for sure. The amount of protection you get by enabling multi-factor is amazing. It moves these attacks from ‘easy’ to ‘not worth it’ for most attackers.
On #3, well, nodejs is on the server as well as your browser. Its in the CI of your suppliers. Trojans were dropped, who knows where, affecting who knows what else in the build process. During the day or so this was out there there will have been hundreds of thousands of ‘pull’s into totally unknown environments, some of which will have long running ripple effects.
Now, on #4. You would be wrong. You are only seeing this because its open. And, others saw it, got it correct. I bet for every one of these found and fixed in open source, the time is very short compared to those in proprietary code that go hidden by the lack of eyeballs.
Now, on the Oh No, Not Again. I’ve written of this before. This exact attack has happened over and over. So, what is our call to action?
- Developer support platforms (github, nodejs, pypi, …) should have multi-factor on by default. This is not onerous, the target audience are developers, they can figure it out without trouble.
- Open source should have some reputation we can check, and, it should include some score card of best practices. How many developers have push access? Do all have multi-factor? How is the supply chain protected? If one was compromised, would that be enough?
- Update early, update often.