Microsoft Remote Desktop
VIA Zero Trust
If you have Windows servers (or desktops) you need to access from any user, on any device, from anywhere… This is what you need
Most of your applications are now modern, responsive web apps. However, you still have some native Desktop applications. You need to be able to access them remotely, safely, simply. You need to be able to grant access to specific Desktops to specific users, but, they may not work for you. Your Desktop may run in a site without a public IP, or a configurable firewall allowing safe inbound access. Perhaps your house, perhaps a branch office.
In 10 minutes you can have 1-click remote access to that Desktop. With no configuration onsite, no change to the Desktop or the firewall.
Via Remote Desktop Protocol, or via VNC.
Via a Native Client, or via a web interface.
Desktop Access Setup
Note: you can use a site-to-site VPN via IPSEC, or use the onsite Agilicus Connector for each pool of servers. These instructions assume the latter.
CREATE ORGANISATION
See SIGNUP
SETUP IDENTITY
Also setup initial users and group membership.
CREATE CONNECTOR PER SITE
CREATE DESKTOP RESOURCE
ASSIGN PERMISSIONS
CONNECT
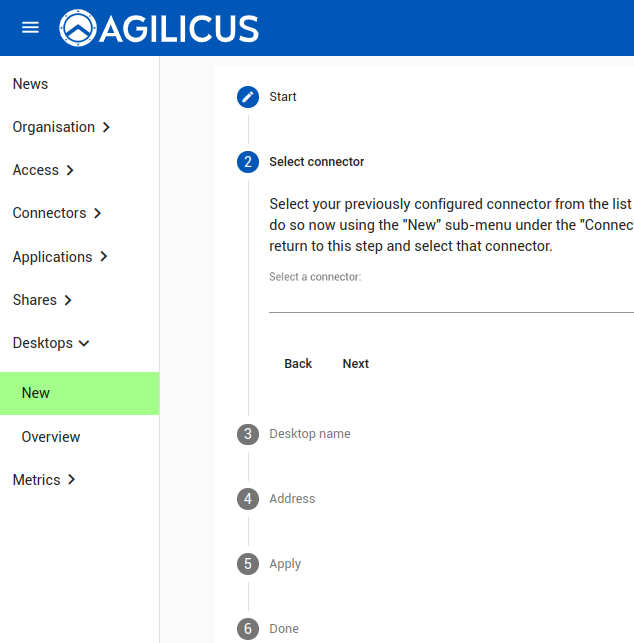
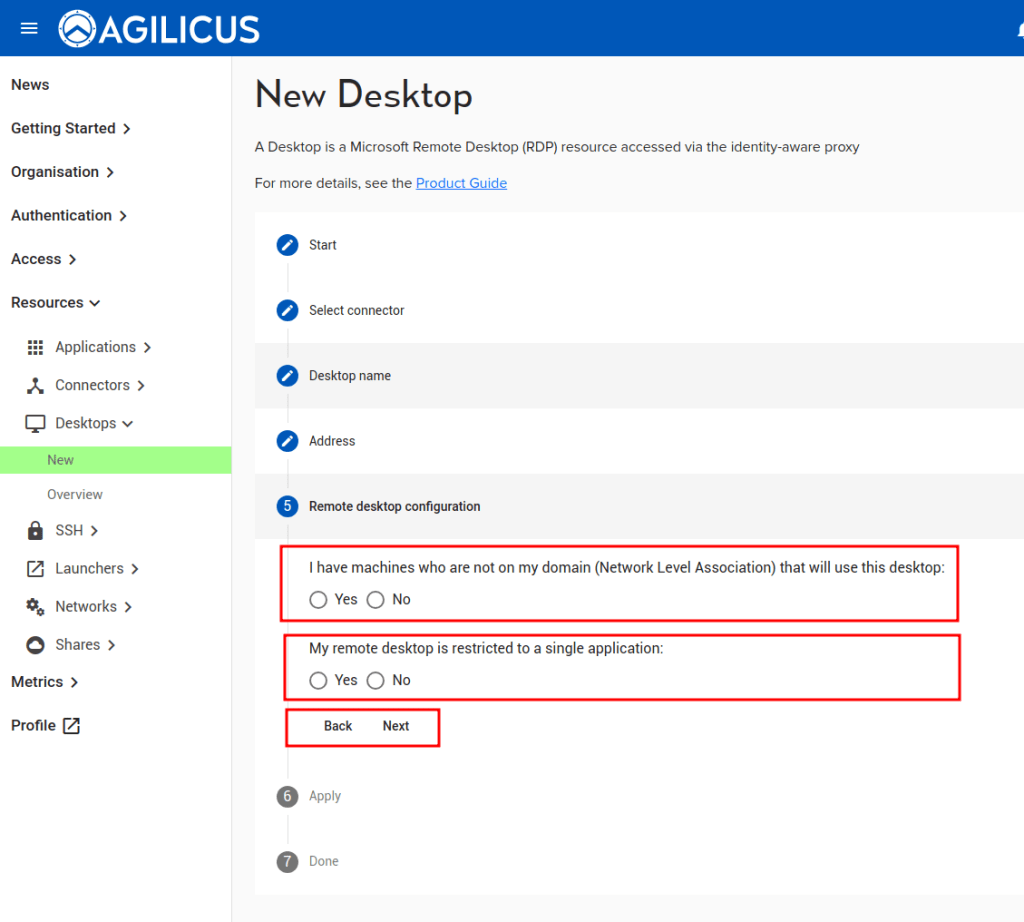
Detailed Desktop Creation
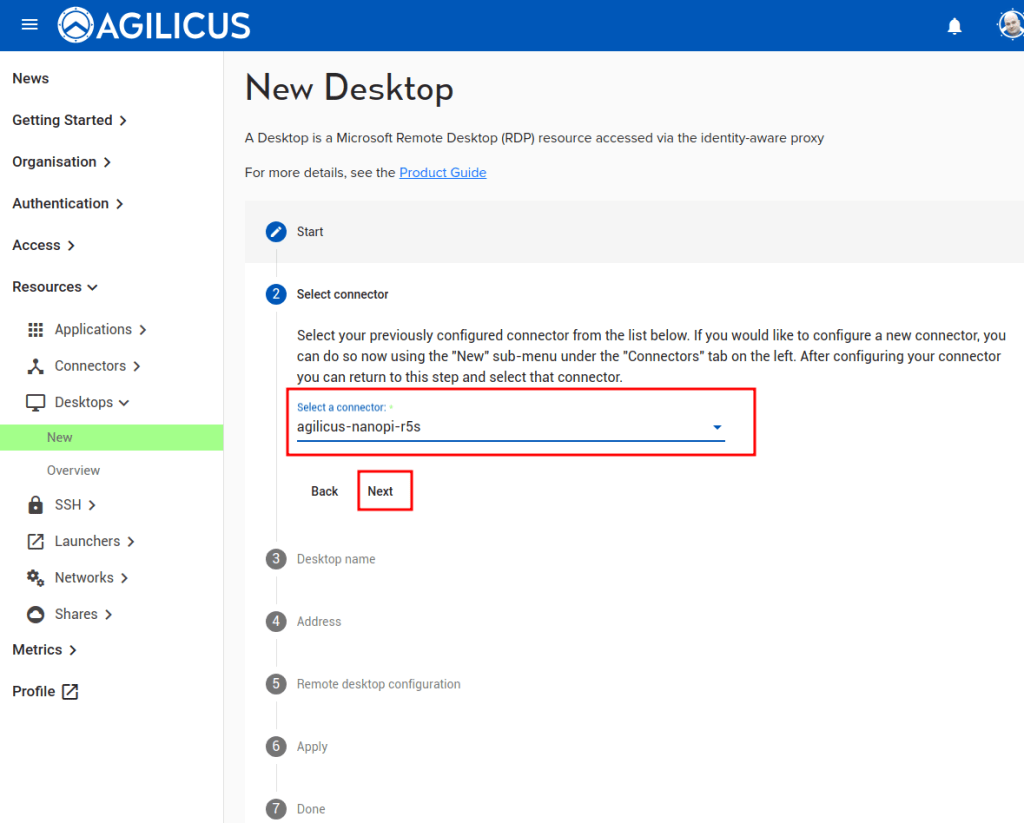
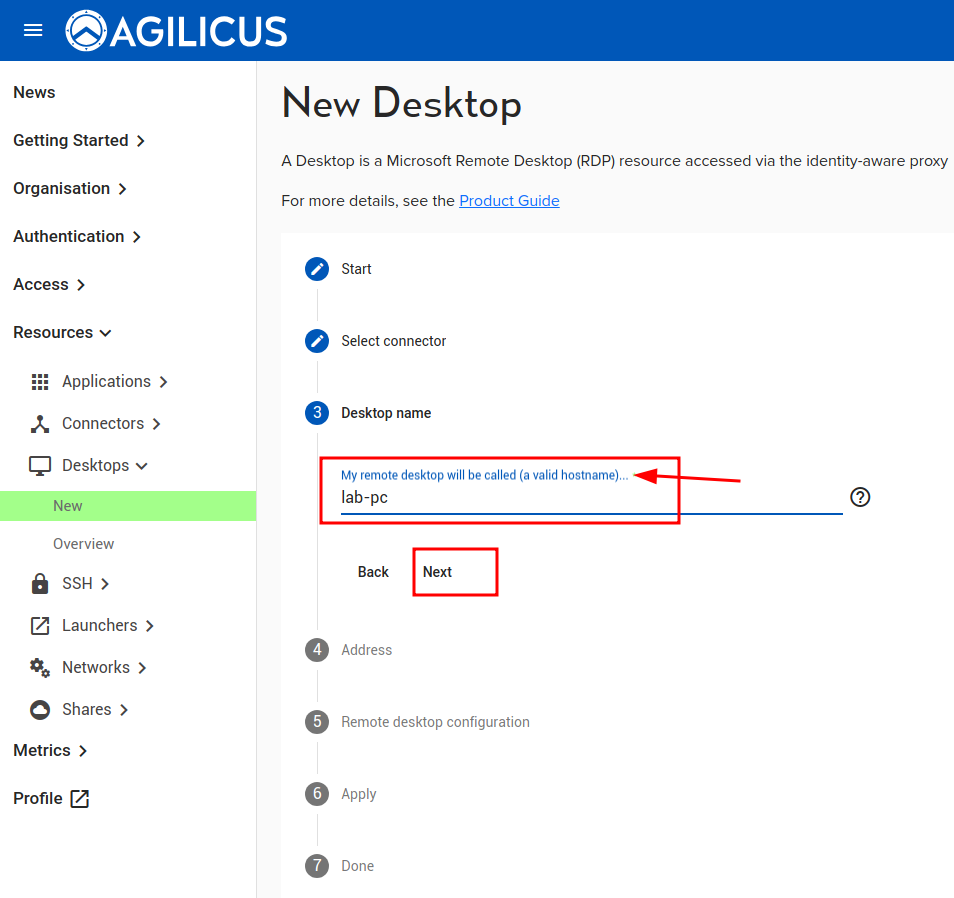
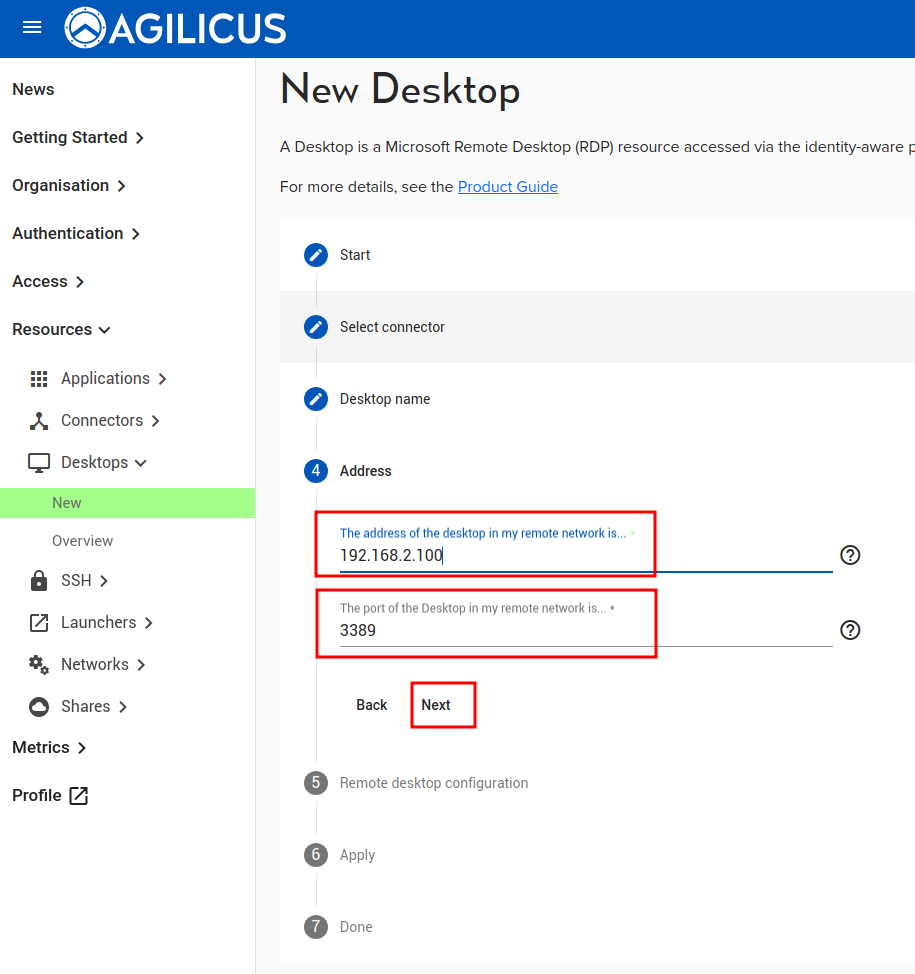
The ‘Desktops/New’ asks 3 questions:
- Connector. This you will have already setup, you need 1 per site (or more if you wish, e.g. 1 per host)
- Name. This will be the ‘name’ you assign permission to, it will show in the audit, the end-user will see it
- Hostname/IP. This is how you would address the Desktop within the (private) site.
Once you have completed these steps, as an Administrator you will be offered the opportunity to download an RDP file. This will open in your native Remote Desktop application (on all platforms). The Desktop will become available approximately 1-2 minutes after you apply the config. (This is to test the configuration)
You may now assign permissions (by group, or by user). Each user who has access will see, in https://profile.MYDOMAIN, an icon for the same Remote Desktop. They may also install the Agilicus Launcher which will create start menu icons automatically.
The detailed steps and screen shots are shown below.
/ontainer
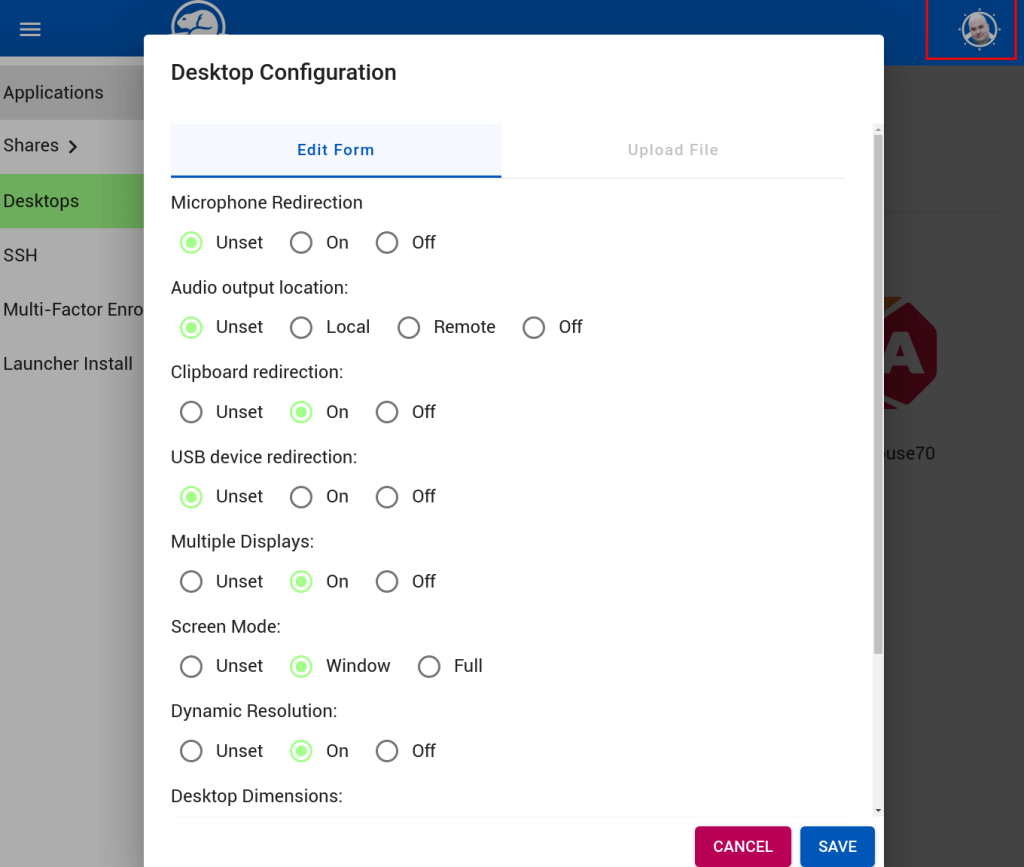
Connection Parameter Override
End users may wish to configure specific overrides regarding their local displays, resolution, clipboard, etc.
The configuration options are found in their Profile (https://profile.YOURDOMAIN), under their account icon.
Users may choose to passthrough their microphone or audio output, clipboard (cut and paste), usb devices.
Some remote desktop servers have multiple displays, these can be passed through if desired.
The user may select dynamic resolution (e.g. they can resize the current window and it will resize the remote), or a specific dimension.
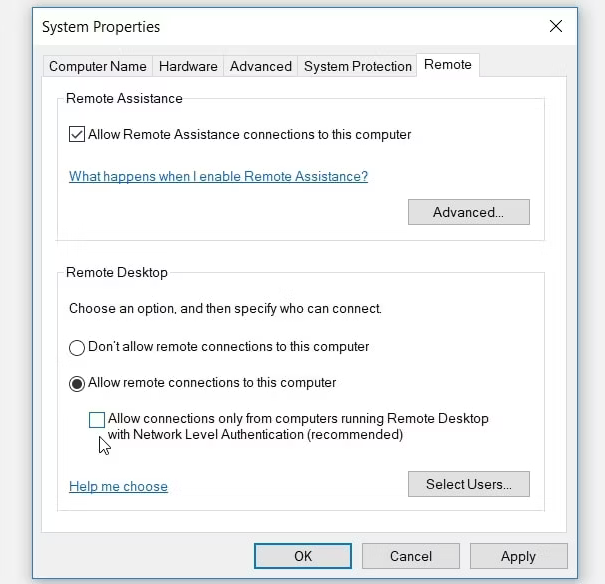
NOTE: You may need to change the Network Level Authentication on the server
- Press Win + R to open the Run command dialog box.
- Type sysdm.cpl and press Enter to open the System Properties window.
- Navigate to the Remote tab.
- Uncheck the Allow connections only from computers running Remote Desktop with Network Level Authentication (recommended) box.
- Press Apply and then press OK. From there, restart your PC to save these changes.