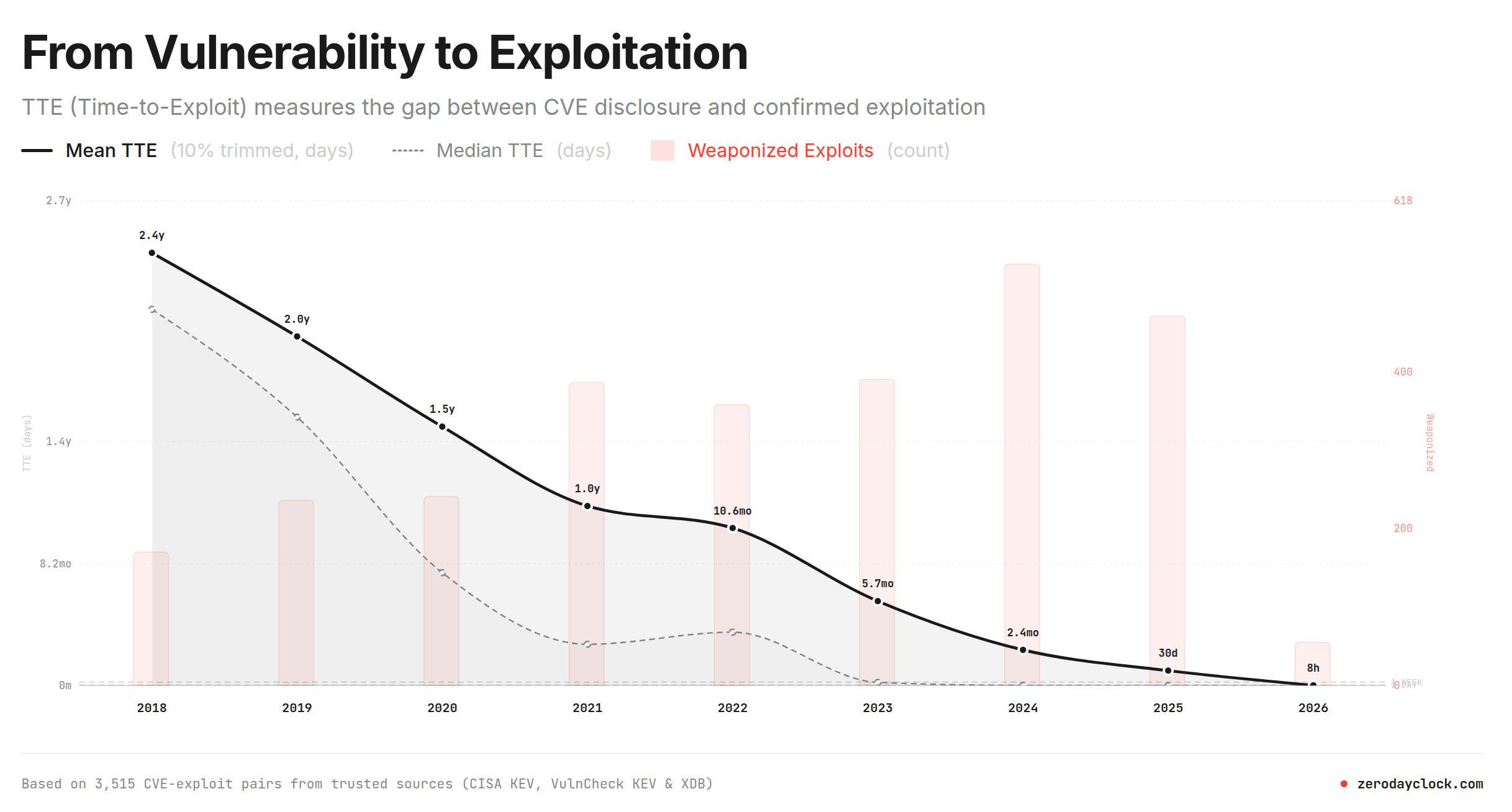
The time between a vulnerability being detected to exploited has been declining. This web site https://zerodayclock.com has a great graph, below. It shows that in 2018 you had 2.5 years from detection to get a fix deployed. This worked its way through your supply chain and you updated. Think of a ‘log4j‘ type vulnerability, its a library inside a component inside a larger component inside a product you buy. The ‘gear lash’ speed takes a bit of time, but eventually you get it.
Fast forward to 2025. You had a month. Ouch. The schedule crunch on you, the deployer, was harsh. Maybe the first vendor took 20 days, the second took 5 days, the third 3 days. You have 1 day.
Now. poof. Its 2026. 8 hours. The magic AI means even if you became aware instantly, the sheer build-time of the steps can’t get there. Continuous Deployment + Dependabot can’t save you, and those are modern cloud-native.
You need a fallback strategy. Defence In Depth. You need to plan for each layer being exploited, rather than solely relying on a single unexploitable perimeter.
The engineer in me wonders if this can go anti-causal, if it will go below zero. The short answer is, nearly certainly it already has. The attacker doesn’t disclose the CVE, they just find and use. I talked about this in “AI-Powered Cyber Threats: Protecting Your Critical Infrastructure“. The philosopher in me wonders… is this how it all ends?