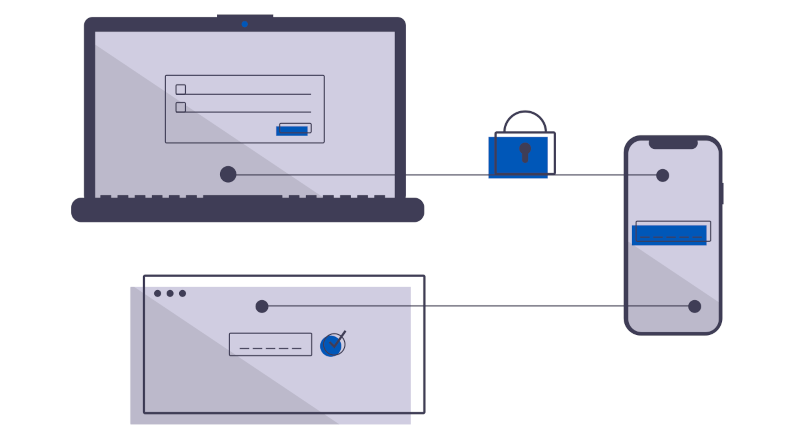
Your cyber insurance is up for review. If you can get all applications authenticated with multi-factor, you can afford it. But, you have only managed to get the new ones done, leaving the miscellaneous. Let’s talk about how an authenticating proxy can get the rest done, with no work, no fuss. Become compliant right quick.
Learn More?
Recent Articles
-
NERC CIP-003-9: Why your VPN is a compliance dumpster fire
-
Speed To Chaos: What The Stryker Breach And CrowdStrike Outage Teach Us About Centralised Systems
-
The SERC regional risk report: Why vendor remote access is a critical vulnerability
-
Asset inventories are great, but who is actually logging into your PLC?
-
Securing Canada’s Critical Energy Infrastructure: Navigating New Cybersecurity Regulations with Zero-Trust Architecture
-
CSA Z246.1: Security management for petroleum and natural gas industry systems