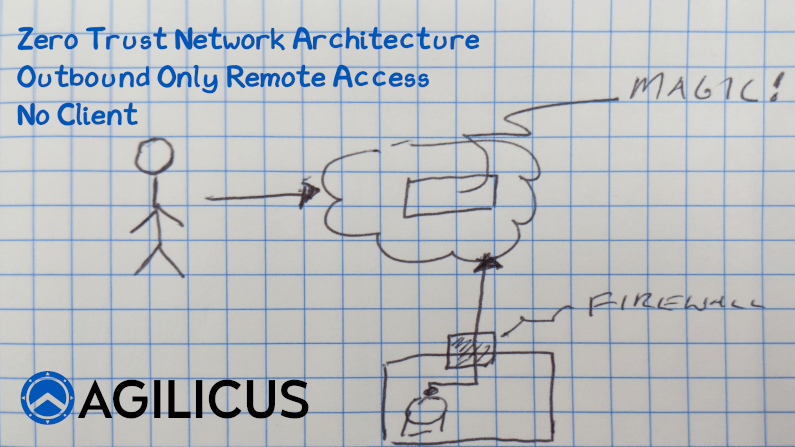
Zero Trust Network Access. The principle of managing security between a user and a resource, rather than a user and a perimeter. By Identifying the user, providing Authorisation in the network, and then remote access to individual resources, we increase security and simplify at the same time. But, did you know you can do this with 0 inbound connections open? Nothing. No ports open to see on a pentest, on nmap, on Shodan. How? In this video I explain. In a nutshell, the resource makes a permanent outbound connection to the cloud. The user makes an outbound connection to the same cloud. Identity is confirmed, Authorisation is confirmed. The connections are stitched together. Simple and secure, no reconfiguration of firewalls. No client VPN software.
Learn More?
Recent Articles
-
NERC CIP-003-9: Why your VPN is a compliance dumpster fire
-
Speed To Chaos: What The Stryker Breach And CrowdStrike Outage Teach Us About Centralised Systems
-
The SERC regional risk report: Why vendor remote access is a critical vulnerability
-
Asset inventories are great, but who is actually logging into your PLC?
-
Securing Canada’s Critical Energy Infrastructure: Navigating New Cybersecurity Regulations with Zero-Trust Architecture
-
CSA Z246.1: Security management for petroleum and natural gas industry systems