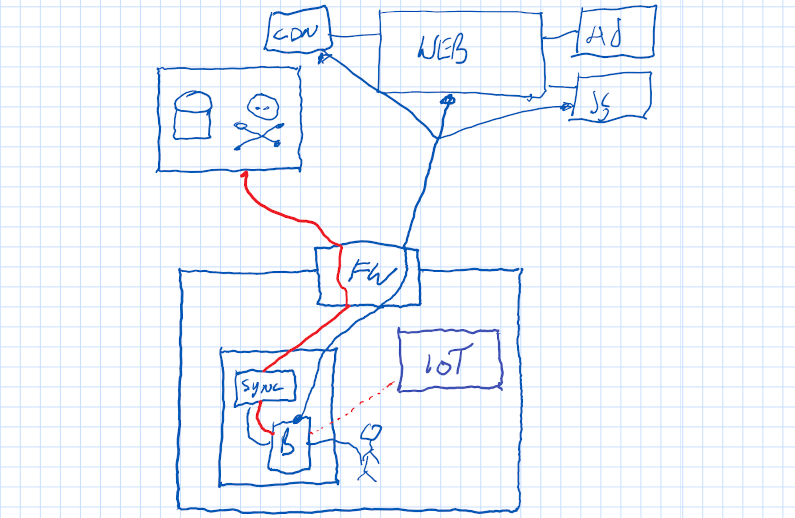
Zero Trust. The general premise is you move from perimeter-based security to focusing on the user and the resource, forcing them to prove their identity to each other on each connection. Gone are the days of the VPN as a big giant switch moving you from infinitely untrusted to infinitely trusted.
It sounds very esoteric and “Not for me”. But it is for you. If you have recently been working from home, and, if your company has a VPN, you know how bad that can be. Yesterday, for example, I had a standard video conference call (Google Meet) with a company. All 3 attendees were unable to join. The reason? They run a corporate VPN, this means that 100% of traffic flows from their house into the company. In turn, the company filters out all the nasty content (YouTube being the culprit here). So, when the VPN is connected, their Internet is broken.
Do you wish you could use the device of your choice, wherever you were, and just have to prove who you were? You can for all your personal activities (your bank, your email), so why not your corporate?
Well, the good folks at the US National Insititude of Standards agree. And they have published this architecture guide to help you on your implementation. https://nvlpubs.nist.gov/nistpubs/SpecialPublications/NIST.SP.800-207.pdf
You know what’s even simpler than reading that? Call me. I’ll make it happen for you.