WHITE PAPERS
Zero Trust with Agilicus AnyX
Learn how organisations are using Agilicus AnyX to adopt Zero Trust. Read more about industry best practices with our white papers, and learn why the platform stands out when it comes to enhancing security with our brochures.
White Papers
-

Industrial Cyber Security Best Practices
Best practices guide for cyber security practices in hybrid information and operational technology networks.
-

Enabling NIS2 Compliance for VNC Remote Access in Industrial Control Systems
Learn how to secure legacy factory screens and HMIs without replacing your existing architecture. Agilicus AnyX applies zero trust to legacy protocols, delivering multi-factor authentication seamlessly.
-
Why traditional VPNs are the weak link in NERC CIP-003-9 compliance
Discover why legacy virtual private networks fail NERC CIP-003-9 standards and how zero trust provides a secure, invisible alternative for energy utilities.
-

The energy utility’s guide to replacing VPNs for NERC CIP secure remote access
A guide for energy utilities replacing VPNs. See how zero trust identity-aware proxies solve OT network complexity and ensure NERC CIP-003-9 compliance.
-

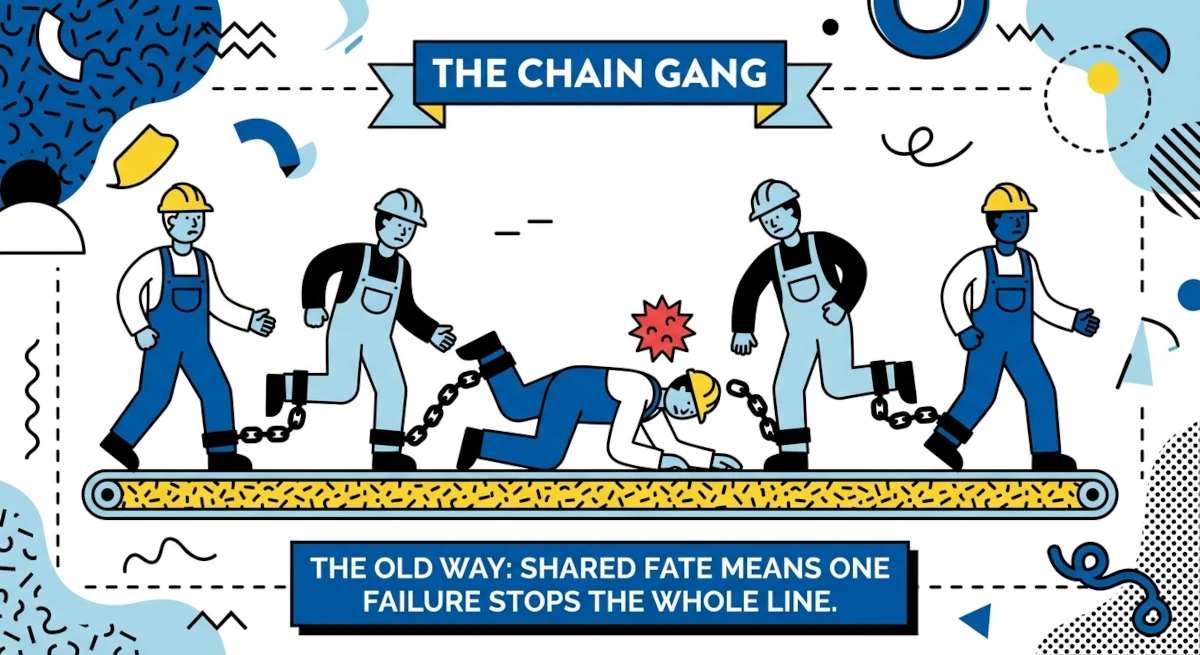
The Fragility of Interdependence: Securing the Hyper-Specialised Supply Chain in the Age of Cyber-Physical Convergence
Hyper-specialised supply chains are fragile. Download this whitepaper to see how zero trust secures the industrial mesh against evolving cyber threats.
-
Multi-Site Manufacturing
Multi-site manufacturing requires seamless access. Discover how identity-based zero trust delivers secure connectivity for staff and contractors at every site.
-
The Frictionless Factory: Solving the Connectivity Crisis in Hyper-Specialised
Solve the connectivity crisis in hyper-specialised factories. Decouple access from the network with Agilicus AnyX to eliminate VPN friction and cyber risk.
-

Agilicus AnyX Configuration Security
Is cloud configuration secure? Learn how Agilicus AnyX protects your settings and discover why it offers superior security compared to on-premise systems.
-

How zero trust architecture secures critical energy infrastructure and satisfies NERC CIP
Energy providers: satisfy NERC CIP-005 and CIP-003-9 with zero trust. Deliver unified authentication and precise authorisation without network changes.
-

Secure remote access for energy utilities: Meeting NERC CIP standards without a VPN
Secure energy utility remote access without VPN headaches. Learn how identity-aware proxies ensure NERC CIP compliance for third-party vendors and OT networks.
-
Simplified NERC CIP compliance for low-impact BES cyber assets
Meet NERC CIP-003-9 requirements for low-impact BES assets. Agilicus AnyX delivers seamless multi-factor authentication without complex network configuration.
-

NERC CIP-003-9: Automating access control and authorisation for remote power sites
Automate access control for remote power sites. Replace manual processes and legacy VPNs with agile zero trust to meet NERC CIP-003-9 requirements efficiently.
-

NERC CIP-003-9 and the shift to multi-factor authentication
Energy utilities: secure low-impact systems with multi-factor authentication. Discover how zero trust enables NERC CIP-003-9 compliance for legacy OT.
-

NERC CIP-003-9 – Legacy Remote Access Tools are Not Sufficient
On April 1, 2026, CIP-003-9: Cyber Security – Security Management Controls will become enforceable. Meet those requirements with a Zero Trust platform.
-
VPNs: Complex, non-compliant, and lacking security for modern remote access
VPNs are no longer sufficient for modern security. Explore why traditional remote access fails to meet compliance and how zero trust provides a safer foundation.
-

Securing the Distributed Supply Chain: Why Identity is the New Air Gap
Secure the distributed supply chain in Industry 4.0. Learn why zero trust architecture makes identity the new air gap for complex manufacturing ecosystems.
-

Secure Remote Updates For Air-Gapped Systems
Challenges with, and solutions for, Secure Remote Updates in modern complex control systems deployed in locked-down, air-gap-style networks. Agilicus AnyX enables and secures remote updates for air gaps.
-
High Availability Dual WAN Remote Industrial Connectivity
Industry cannot stop. Industry is also commonly located in remote areas with less network connectivity choices. Learn how Agilicus AnyX facilitates High Availability Dual WAN Remote Industrial Connectivity.
-
Subscription Model and Remote Access In Industrial Control
Subscription Model and Remote Access In Industrial Control. The quest for revenue creates risks for operation.
-
Merging Local Identity With Online Identity
Modern online Identity with Azure, Google, Okta. Manufacturing plants with Local Identity — onsite users Unify with Agilicus AnyX
-
NIST SP 800 53 Mapping To Zero Trust
NIST SP 800 53 Mapping To Zero Trust. NIST SP 800 53 is a comprehensive set of security controls. Zero Trust Network Architecture is a technology. Explore the intersection.
-
NIST SP 800-53 in Critical Infrastructure
NIST SP 800-53 is a core part of the NIST cybersecurity framework. It provides mappings of controls to various other standards. Zero Trust is a complementary architecutre supporting these controls.
-
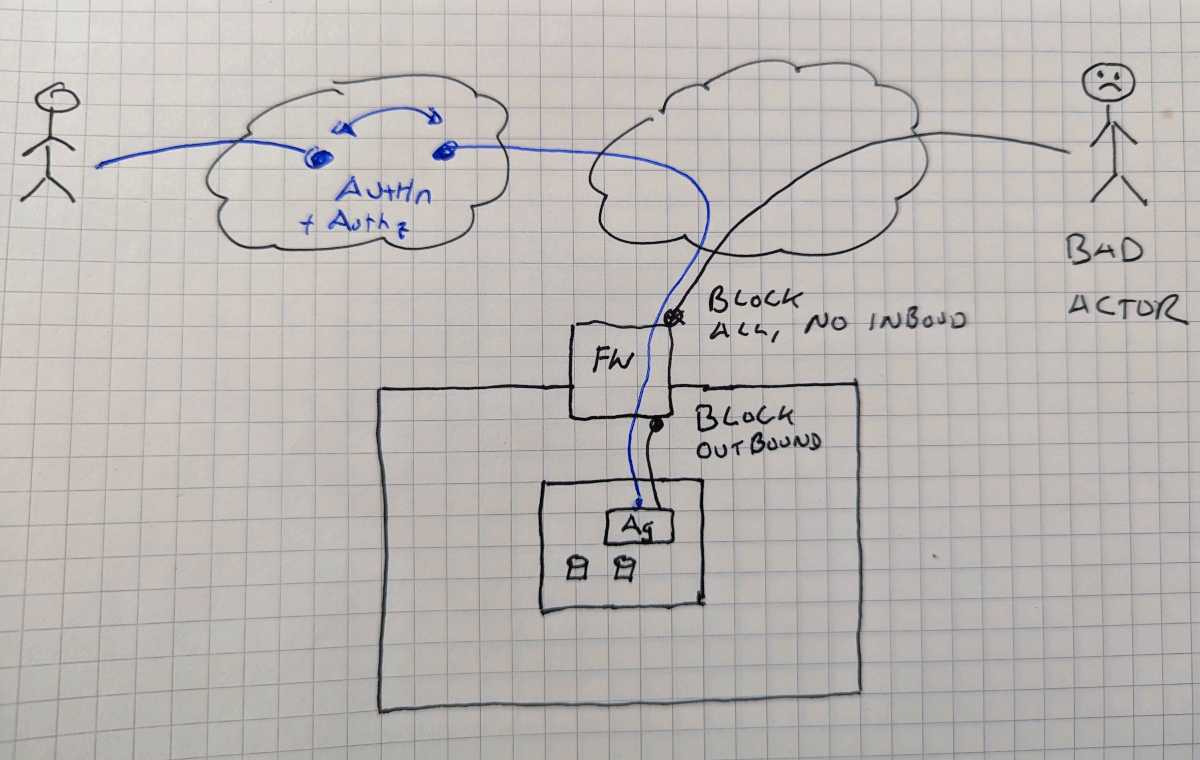
Zero Trust Air Gap Lock Down Inbound and Outbound
Air Gaps are a useful but inconvenient tactic as a part of a defense in depth strategy. Learn how a Zero Trust Air Gap Lockdown Inbound and Outbound can provide convenience and security together.
-
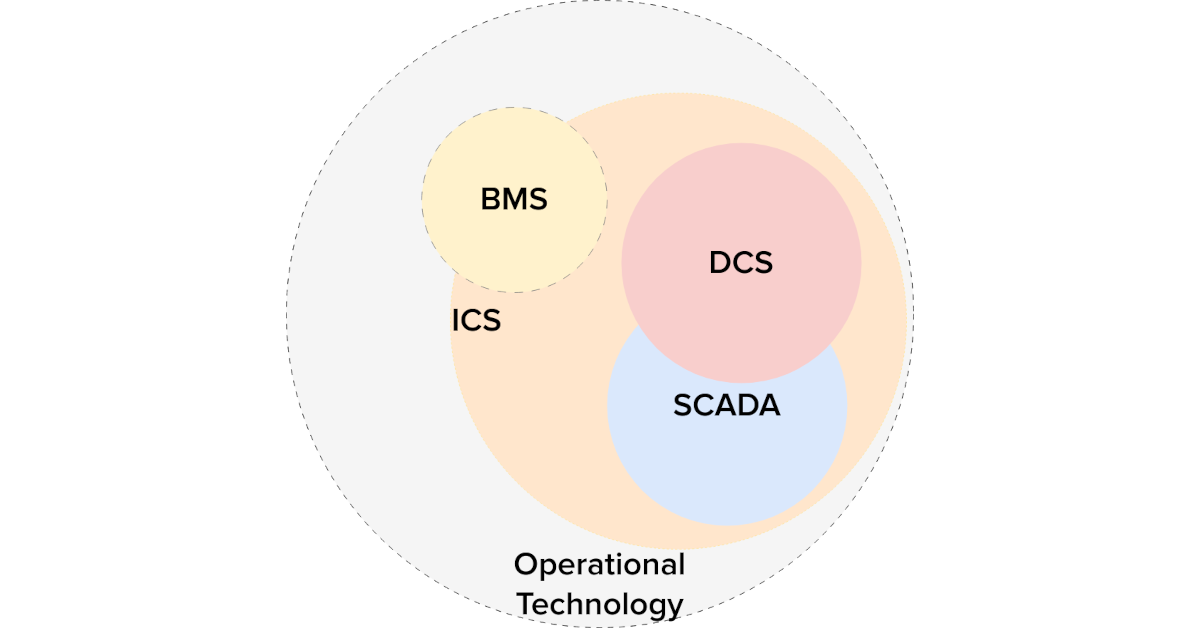
Piercing The Purdue Model: Zero-Trust In Operational Technology
Unravelling the interaction between the Purdue Model and Zero Trust: When married together in operational technology, the outcomes can be transformative.
-
Multi-Factor Authentication On The Internal Network
Cyber-Insurance compliance require multi-factor on internal network resources? Routers? Servers? Learn how to implement without a VPN, without changes.
-
Industrial Zero-Trust Micro-Segmentation
Micro-Segmentation Zones are a best practice for Industrial Control security. Simplify and increase effectivity with identity-based Zero-Trust. Industrial Zero-Trust Micro-Segmentation
-

Eliminate Attack Vectors and Stop Cyber Threats in Their Tracks with a Zero Trust Architecture
Eliminate Attack Vectors and Stop Cyber Threats in Their Tracks with a Zero Trust Architecture. Cyber threats come from all angles these days, yet most businesses are still ill equipped to properly keep the bad actors out.
-

Remote Desktop Access: Managing Cyber Risk with Zero Trust Network Access
Eliminate unmanaged cyber risk by securing remote desktop access through zero trust network access and improve your cybersecurity posture.
-
Azure Application Consent
The Agilicus AnyX platform uses external Identity Providers rather than creating ‘parallel’ identities for users to remember. What permissions are being granted on those upstream systems?
-

Starlink Port Forwarding
Starlink. Good enough except for starlink port forwarding. Reach your devices from remote with Agilicus, securely, simply, reliably.