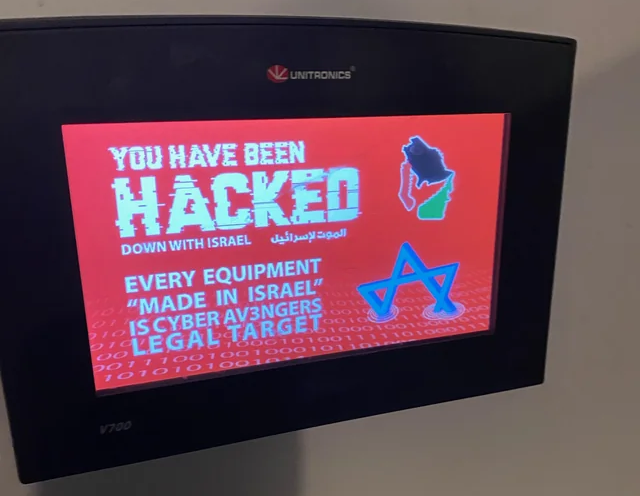
In “Avoid Exploitation of Unitronics PLCs used in Public Water Systems” I wrote of a group named Cyber Av3ngers affiliated with the IRGC targetting, modifying the HMI of the Municipal Water Authority of Aliquippa along with several other water systems.
According to Cisa, thanks to a simple default password – like 1, 2, 3, 4, 5, 6 – the Iranian hackers were able to disable a monitor regulating water pressure, but plant managers were able to take over manually.
The Iranian attackers, posing as anti-israel / pro-palestinian, changed some pressure regulating settings. Well, they got noticed. The US has issued sanctions, personally, against those responsible, using Executive Order 13224 and the long arm of the US financial system. This order, September 23, 2001, by George W Bush, was about a different kind of terrorism, but had the same objective.
Today, the Department of the Treasury’s Office of Foreign Assets Control (OFAC) sanctioned six officials in the Iranian Islamic Revolutionary Guard Corps Cyber-Electronic Command (IRGC-CEC), an Iranian government organization responsible for a series of malicious cyber activities against critical infrastructure in the United States and other countries.
https://home.treasury.gov/news/press-releases/jy2072
CISA uses the words ‘target rich, resource poor’ to describe a set of sectors, the critical infrastructure of water being one of them. Their key sectors, “Water, Hospitals, K-12 Eduction”.
As for that password mentioned above, yes, of course it should be stronger. Yes we all enjoy a bit of schadenfreude knowing full well we do it better.
But, you can’t. Some of that equipment is a permanent fixture, and permanently insecure. You need to haul the authentication up in front of it, an identity-aware proxy, Zero Trusts. There is no safe method to operate these things with a VPN or other layer-3 remote access systems either to them, or to the network they live in. So operating within the constraints of budget (are you going to redesign and rebuild this plant?), manufacturer equipment practices (are you going to reverse engineer the firmware and fix it?) and the asymmetric nature of cyber warfare (blue team needs to be right 24x7x365, red team only needs to be right once), are you really going to be better? YES, since you read this blog, and you now know that Agilicus can help.