Somewhere in your basement lurks a challenge. A web application that people need, but you don’t trust. Maybe its your timesheet or vacation planner. Maybe its your HR policies portal. But you know if it meets the Internet that you’ll be in the news. We need Secure Exposed Access!
Sure, you could retool it. Add some 2-Factor Authentication. Audit its east-west traffic flows. Add a SIEM in the path. But, would you feel confident? Maybe we’ll just let it lay, internal use only. But, the costs are rising. We are now creating accounts in Active Directory for our temps and contractors solely to access this system. This is in turn causing a cost issue associated with Named Users licenses. Some of these temps don’t otherwise have a desk or PC in the building, and we are forced to create access locations. There has to be a better way.
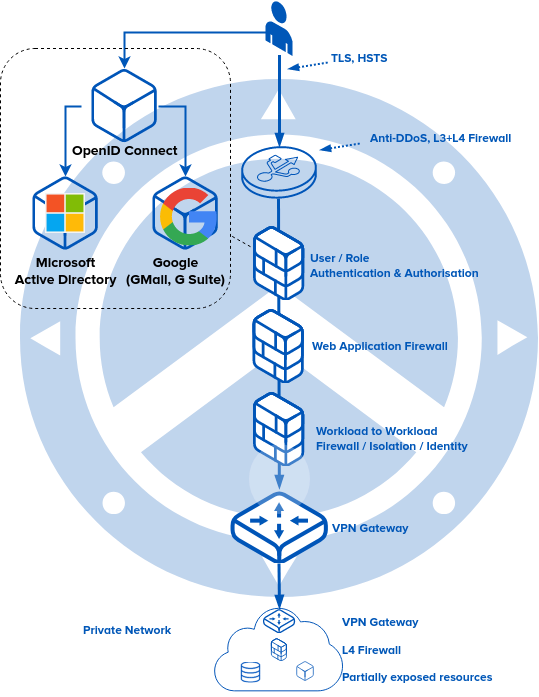
Spoiler: there is, and we can help. Let’s use our concept of Zero Trust and Strong Identity. Let’s add an authentication & authorisation gateway on the public Internet, owning the domain name and TLS. Let’s add a web application firewall that is authz aware in the middle, enforcing that only authenticated users can access, and, that the access is appropriate for the role. Let’s endow that web application firewall with some rules to prevent common cross-site-scripting and click-jacking.
Now, let’s keep that site in the basement. But, let’s add a simple VPN, and, on top of that, a workload identity-aware firewall, using a crypto-technology like SPIFFE.
Boom. Our users think the site is now on the public Internet. BYOD works, any device, any user, any location, any time. 2-Factor (your YubiKey or TOTP) just works.
Security is actually higher than when you were using it inside the building: those XSS attacks are mitigated, in the building they were still possible.
Want to know more? Secure Exposed Access. contact us!