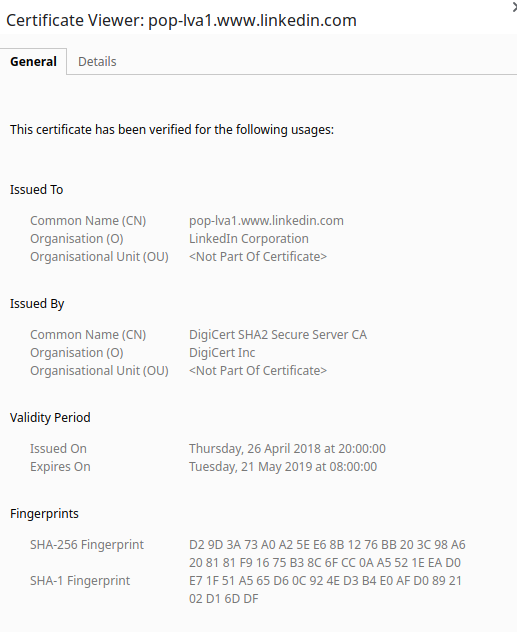
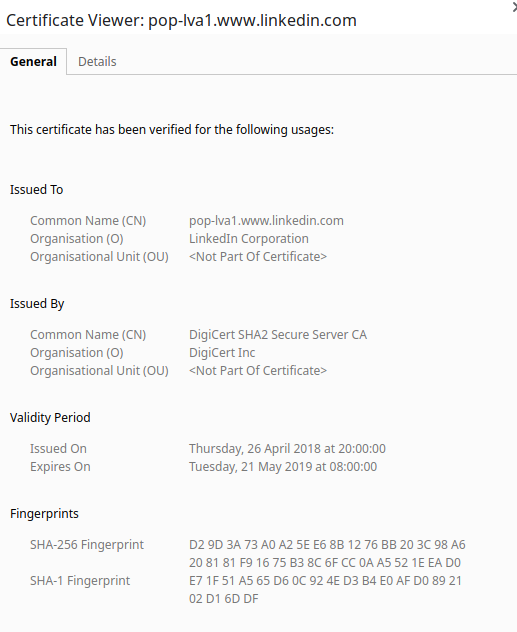
Imagine my surprise this am to find a post on LinkedIn, with their shortener, inaccessible. It turns out the TLS certificate expired this am for linkd.in. Hmm.
This is a general problem, and one for which some great solutions exist. E.g. using Let’s Encrypt, we can use CertManager to auto-create/refresh. There are tools to watch the expiry date as well.
When good certificates go bad it trains users to ‘accept’ the error (curl -k, accept in browser, etc). This is not acceptable, users should see a NET:ERR_CERT_DATE_INVALID as a hard-fail, not as a “oh, security, we’ll yada yada that”.