On Friday February 5th a water treatment plant in Florida was breached by an attacker looking to increase the chemical flow, poisoning people, destroying pipes. It was caught more or less by chance. How did the hacker get in, and how would we systematically make this more secure? Can Zero Trust secure SCADA? Read more about the ISA/IEC 62443 Micro Segmentation Zones and Conduits and how it inter-relates to Zero-Trust.
Well, we have some information in the Cybersecurity Advisory for Public Water Suppliers. And, in a nutshell, a Windows 7 PC was setup with internal access to industrial SCADA devices. The PC was also running TeamViewer, which allowed anyone with the password, from anywhere in the world, to behave as if they were in front of the monitor/keyboard/mouse. Your critical infrastructure defeated.
Now, clearly not a best practice, but, behind every bad practice is an unmet product need. Its easy to scold the folks who set this up and then shared the password around. But, they had a need to safely, securely, remotely control something that was very poorly designed for the purpose (SCADA).
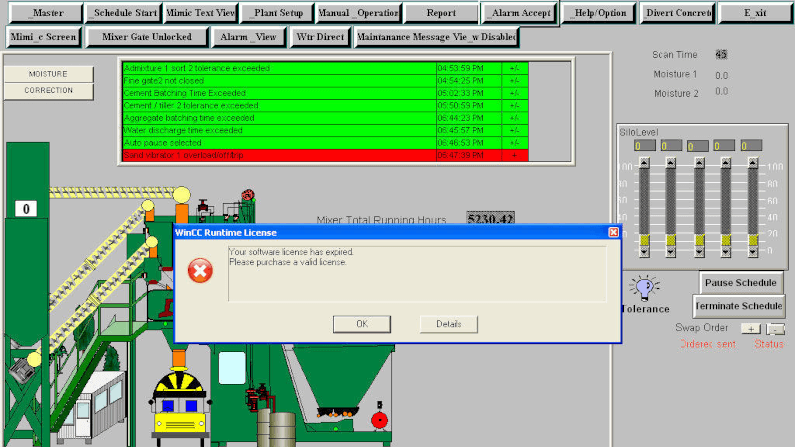
If we were to architect SCADA today, we would do it using modern API’s, API gateways, JSON Web Tokens, etc. But, redesigning it means revisiting a lot of industrial power plants and manufacturing systems. So, you find this sort of setup fairly frequently, VNC or TeamViewer etc, bridging the air-gapped network. Its not a new threat, its fairly well documented, e.g. “Scared? Or Bored? Terrorists and teh power grid“. If we use Shodan.io we find many SCADA devices exposed one way or another. My favourite was this one which showed a cement plant on unauthenticated VNC.
So, given we have a system that should not be Internet exposed, and given that we have remote lights out installations it runs in that are expensive and inconvenient to staff, and given that people are bridging this gap unsafely, how can we enable to them to do so safely?
Enter Zero Trust. The principle that we move from bastion-based security to user<->resource pairs. We have a choice of how we would use it here. We would either use it to “remote” the SCADA devices themself (so each one would become a resource, and we would ensure only the right user had access, cryptographically secure), or, the remote desktop software itself. On the latter, what we might do is leave that facility-PC as-is, but, instead of allowing it to have TeamViewer or VNC (which have built-in or no authentication), we would prevent the PC from reaching the Internet. Instead, we would use a Zero Trust agent, securely exposing the local Remote Desktop (RDP) software.
This means team members could achieve their exact goal: when needed, safely access that PC, from any device, any network. But, we could control who, and have a full audit trail. There would be no “shadow IT authentication system”, it would be full single-sign-on, single identity provider.
So, would you like to know more or discuss how to use zero trust to secure SCADA? I’d love to get your feedback or questions. info @ agilicus.com,