Content Security Policy
Secure Your Application
A Content-Security-Policy is a header which instructs a browser how to interpret & allow or deny various types of active content (images, fonts, frames, …). It helps mitigate certain types of attacks including Cross-Site-Scripting (XSS) or data injection.
Concepts
A Content-Security-Policy is a header which instructs a browser how to interpret & allow or deny various types of active content (images, fonts, frames, …). It helps mitigate certain types of attacks including Cross-Site-Scripting (XSS) or data injection.
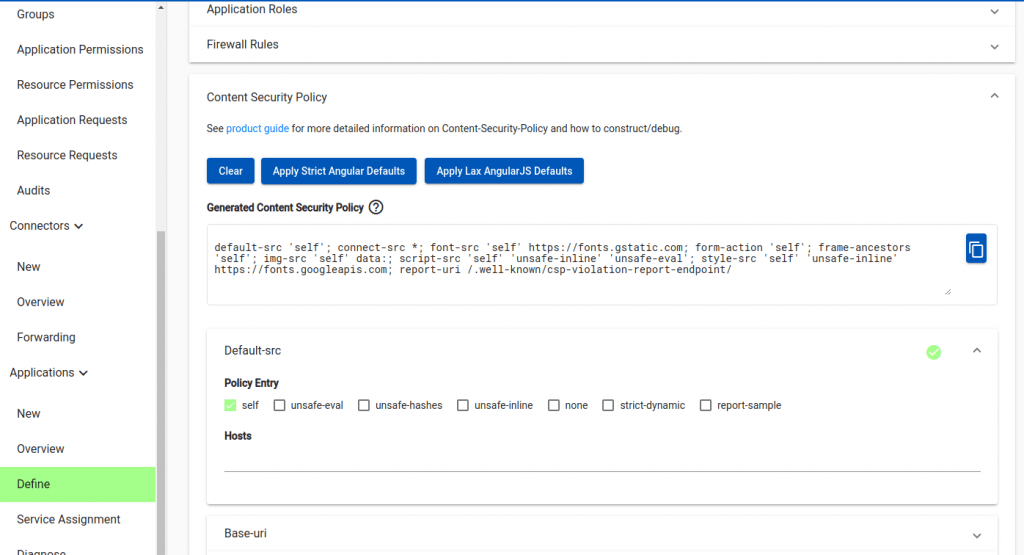
The Agilicus Web Application Firewall allows setting and editing this header. You can see it on the ‘Define’ tab of the application. 3 macro-settings may be applied:
- clear — remove (unset) the Content-Security-Policy
- strict angular defaults — this is a set of defaults suitable for an Angular application compiled with AOT and subresource-integrity
- lax angularjs defaults — this is a set of defaults suitable for an older AngularJS application (including unsafe-inline)
Once you set one of these buttons you may then edit the individual types.
In addition to the check-box settings, a set of ‘hosts’ may be configured. This can include ‘data:’ , ‘*’, ‘https:’, ‘https://example.com’, etc. For more information see Content Security Policy (CSP) in the Mozilla Web Docs.
Additional Information
Want Assistance?
The Agilicus team is here for you. The ‘Chat‘ icon in the lower left, here, or in the administrative web page, goes to our team.
Or, feel free to email support@agilicus.com
Not yet a customer? The TRY NOW button will walk you through the process.