Netgate SG-1100 pfSense
Connector Install
The Netgate SG-1100 pfSense is a small-form factor router. it is a good vantage point to run the Agilicus Connector.
Agent Connector Install: Netgate SG-1100 pfSense
The Netgate SG-1100 pfSense is a small-form factor router. it is a good vantage point to run the Agilicus Connector.
Other pfSense appliances may work, they will need to be arm or x86 based, and have at least 120MiB of storage available. The Agilicus connector will consume approximately 50MiB of RAM.
The below instructions were tested on a Netgate SG-1100 with v22.01, specifically:
# cat /etc/version
22.01-RELEASE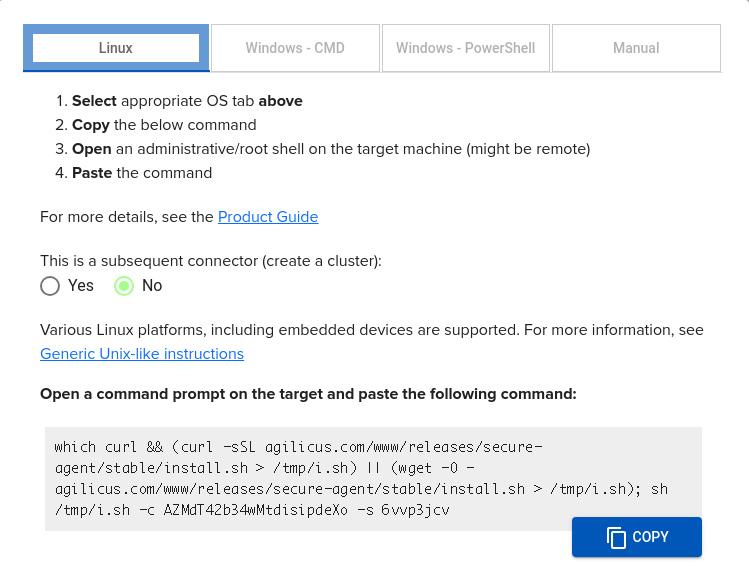
The pfSense installation uses the same instructions as the Linux ones (image at right) A sample command line is offered in the Agilicus admin porttal, which may be pasted into the ssh shell.
Once you run this command, you will see output as below. You are now complete.
The Agilicus Agent Connector will self-update over time, no intervention is required.
We may check the status once installed as below.
Logs (if any) are generated to /var/log/agilicus-agent.log (e.g. run ‘tail -F /var/log/agilicus-agent.log’)
# ps |grep agilicus
29415 2 S+ 0:00.01 grep agi
69960 2 I 0:00.00 /bin/sh /etc/rc.d/agilicus-agent start
70184 2 S 0:03.56 /usr/bin/agilicus-agent client --cfg-file /etc/agilicus/agent/agent.conf.enc.yaml (agilicus-agent-free)
# agilicus-agent version
Version: v0.105.3
Git Commit: 7dcef00647c5653d910f56a38e34b852af6ce373Sample Install Log
The complete log of a sample install is below.
[22.01-RELEASE][root@pfSense.home.arpa]/root: which curl && (curl -sSL agilicus.com/www/releases/secure-agent/stable/install.sh > /tmp/i.sh) || (wget -O - agilicus.comw
/usr/local/bin/curl
Check time synchronisation/NTP is active
OS: <FreeBSD>, Machine: <arm64>, END: <le>
Fetching https://www.agilicus.com/www/releases/secure-agent/stable/agilicus-agent-freebsd-arm64 into /tmp/agilicus-agent-freebsd-arm64
-rwxr-xr-x 1 root wheel 45613056 Jun 3 18:52 /tmp/agilicus-agent-freebsd-arm64
+ /tmp/agilicus-agent-freebsd-arm64 client --install --challenge-id XXXX --challenge-code XXXX
INFO[2023-06-03T18:52:48Z] Starting connector - version v0.201.0
INFO[2023-06-03T18:53:01Z] Check if the agilicus connector is already running as a service. If so stop it
INFO[2023-06-03T18:53:01Z] Create file /usr/bin/agilicus-agent-wrapper.sh
INFO[2023-06-03T18:53:01Z] Create file /usr/local/etc/rc.d/agilicus-agent
INFO[2023-06-03T18:53:01Z] Will install to /agilicus-agent-freebsd.rc -> {/usr/local/etc/rc.d/agilicus-agent -r-xr-xr-x <nil>}
INFO[2023-06-03T18:53:01Z] Will install to /agilicus-agent-freebsd.sh -> {/usr/local/etc/rc.d/agilicus-agent.sh -r-xr-xr-x <nil>}
INFO[2023-06-03T18:53:01Z] Will install to /agilicus-agent-wrapper.sh -> {/usr/bin/agilicus-agent-wrapper.sh -rwxr-xr-x <nil>}
INFO[2023-06-03T18:53:01Z] Create a directory at /opt/agilicus/agent/tufmetadata/latest
INFO[2023-06-03T18:53:01Z] Create a directory at /opt/agilicus/agent/tufmetadata/stable
INFO[2023-06-03T18:53:02Z] Create a user and group named Agilicus to run the agilicus-agent service
INFO[2023-06-03T18:53:02Z] Copy executable to /opt/agilicus/agent
INFO[2023-06-03T18:53:02Z] Set permissions to Agilicus on /opt/agilicus/agent
INFO[2023-06-03T18:53:02Z] Create symlink from /usr/bin/agilicus-agent to /opt/agilicus/agent/agilicus-agent-freebsd-arm64
INFO[2023-06-03T18:53:03Z] creating connector instance
INFO[2023-06-03T18:53:03Z] Join a connector cluster
INFO[2023-06-03T18:53:03Z] Start agilicus-agent service
INFO[2023-06-03T18:53:04Z]
INFO[2023-06-03T18:53:04Z] Installation Complete
INFO[2023-06-03T18:53:04Z]
[22.01-RELEASE][root@pfSense.home.arpa]/root:Want Assistance?
The Agilicus team is here for you. The ‘Chat‘ icon in the lower left, here, or in the administrative web page, goes to our team.
Or, feel free to email support@agilicus.com
Not yet a customer? The TRY NOW button will walk you through the process.