Your corporate firewall. That invulnerable bastion that lets you fearlessly run less-than-secure internal tools like a CRM, a Finance portal. But, is it really invulnerable? Or is it a paper wall at best? We look at how Cross-Site-Scripting vulnerabilities, known session ID cookies or access tokens can allow content from the world to pierce it as if it were not there. We do this using the weakest link: you.
How you ask? Assume that internal system contains some session cookie. You have access to it in your browser because, well, you logged in and you are you. Now lets assume it has some weak library. Perhaps an older version of jQuery or Bootstrap. This is a safe bet, these are two of the most popular libraries going. Now, lets assume you use some site with user-generated content. Or, I can influence you to open something in an email. This malware now runs in your browser in another tab, and boom, it walks sideways. Think it can’t happen to you?
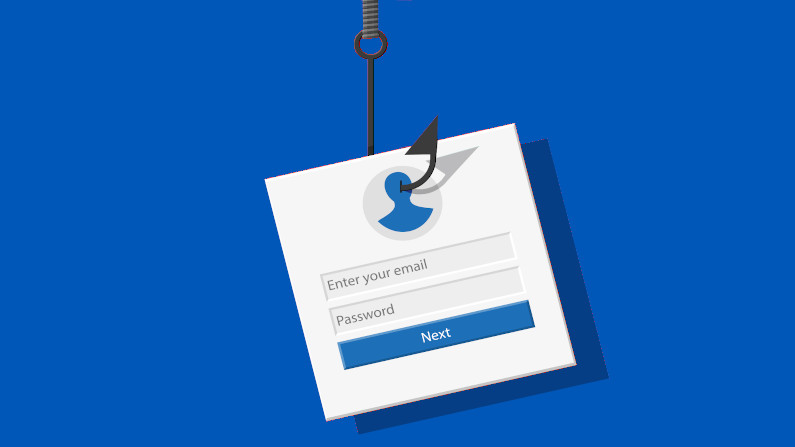
With phishing we are often concerned about the message. Is it trying to get me to change payment info? To get me to login to some site and steal my info? What if all it is trying to do is get you to click? And then make it look as if nothing happened? Your browser is inside the firewall, its logged in to that other system.
Let’s take a snippet of HTML and try. Take the below, save it to a file, open in your browser. This is from a vulnerability discussed in #20184.
<script src="https://ajax.googleapis.com/ajax/libs/jquery/2.2.4/jquery.min.js"></script>
<script src="https://maxcdn.bootstrapcdn.com/bootstrap/3.3.7/js/bootstrap.min.js"></script>
<button data-toggle="collapse" data-target="<img src=x onerror=alert('You-are-hacked');>">Click Me, I'm Safe</button>What can we do about this? Well, introduce a Web Application Firewall in front of each application you use (including that internal Finance or CRM system). Make it identity and role aware so that it blocks requests that are inappropriate. Periodically run campaigns to teach & test your team, perhaps using Gophish. Ensure that all sites you have control over have strong Content-Security-Policies. I use Mozilla Observatory to check this. Perhaps use a tool like retirejs in your browser.